Question
Code from Part 1: void read_file(){ FILE *file = fopen(myfile.txt, r); //Opens file to read char c = fgetc(file); int cnt = 0; while((c =
Code from Part 1:
void read_file(){ FILE *file = fopen("myfile.txt", "r"); //Opens file to read
char c = fgetc(file); int cnt = 0; while((c = fgetc(file)) != EOF) cnt++; printf("%d chars ", cnt); //Prints size of file
int n; char *string = (char*) malloc(n); //Allocates n bytes to string free(string); //Deallocates the memory
rewind(file); //Rewinds file to the beginning
fclose(file); //Closes file }
void write_file(){ FILE *file = fopen("myfile.txt", "w"); //Opens file to write
char *string = "Hello World!";
int i=strlen(string); int j = 0; while(j
fclose(file); //Closes file }
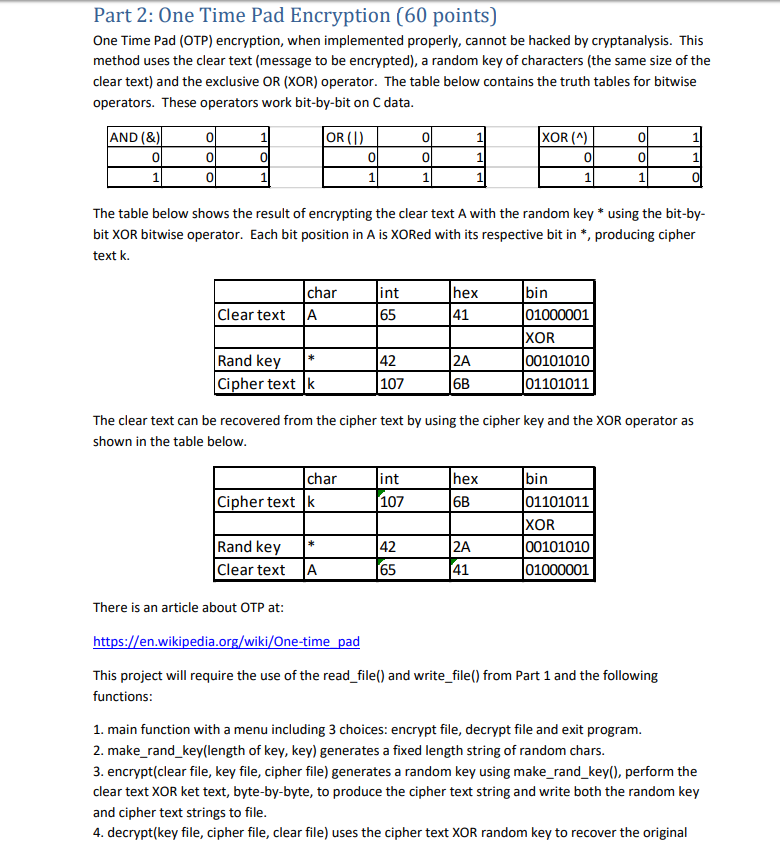
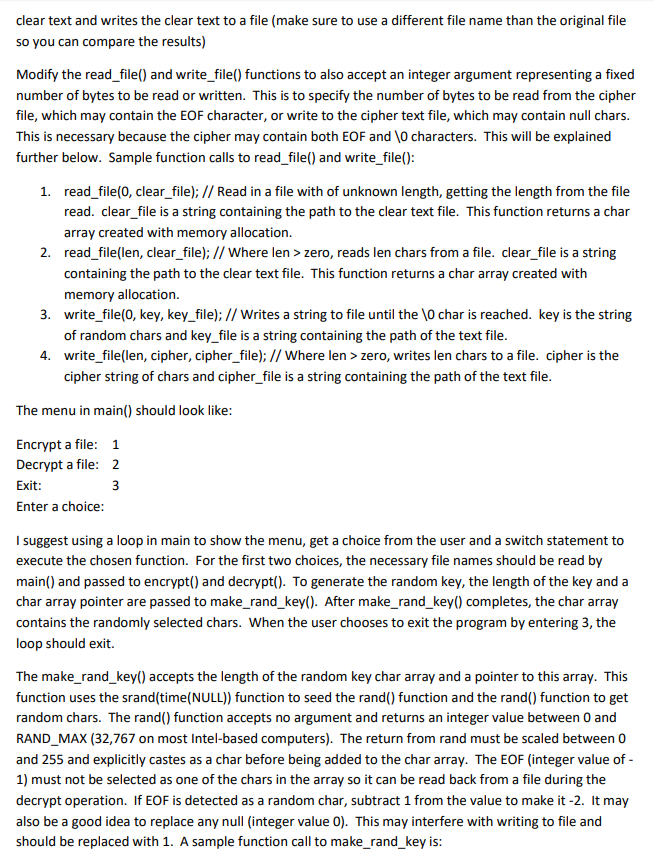
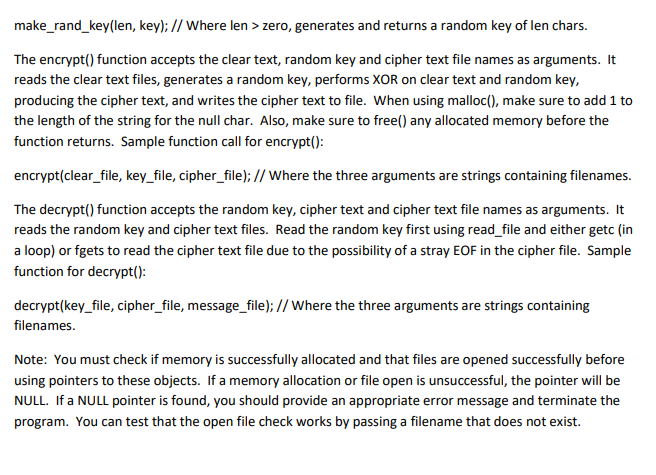
Part 2: One Time Pad Encryption (60 points) One Time Pad (OTP) encryption, when implemented properly, cannot be hacked by cryptanalysis. This method uses the clear text (message to be encrypted), a random key of characters (the same size of the clear text) and the exclusive OR (XOR) operator. The table below contains the truth tables for bitwise operators. These operators work bit-by-bit on C data AND (&) 0 XOR (A 0 OR (I 0 0 0 0 0 0 0 0 The table below shows the result of encrypting the clear text A with the random key * using the bit-by- bit XOR bitwise operator. Each bit position in A is XORed with its respective bit in *, producing cipher text k. char int 65 hex 41 bin 01000001 XOR 00101010 01101011 Clear text A Rand key* Cipher text [k 42 107 6B The clear text can be recovered from the cipher text by using the cipher key and the XOR operator as shown in the table below char hex 6B bin 01101011 XOR 00101010 int Cipher text k 107 Rand key 42 65 Clear text A 41 There is an article about OTP at: https://en.wikipedia.org/wiki/One-time pad This project will require the use of the read file() and write file() from Part 1 and the following functions 1. main function with a menu including 3 choices: encrypt file, decrypt file and exit program 2. make_rand key(length of key, key) generates a fixed length string of random chars. 3. encrypt(clear file, key file, cipher file) generates a random key using make_rand_key(), perform the clear text XOR ket text, byte-by-byte, to produce the cipher text string and write both the random key and cipher text strings to file 4. decrypt(key file, cipher file, clear file) uses the cipher text XOR random key to recover the original Part 2: One Time Pad Encryption (60 points) One Time Pad (OTP) encryption, when implemented properly, cannot be hacked by cryptanalysis. This method uses the clear text (message to be encrypted), a random key of characters (the same size of the clear text) and the exclusive OR (XOR) operator. The table below contains the truth tables for bitwise operators. These operators work bit-by-bit on C data AND (&) 0 XOR (A 0 OR (I 0 0 0 0 0 0 0 0 The table below shows the result of encrypting the clear text A with the random key * using the bit-by- bit XOR bitwise operator. Each bit position in A is XORed with its respective bit in *, producing cipher text k. char int 65 hex 41 bin 01000001 XOR 00101010 01101011 Clear text A Rand key* Cipher text [k 42 107 6B The clear text can be recovered from the cipher text by using the cipher key and the XOR operator as shown in the table below char hex 6B bin 01101011 XOR 00101010 int Cipher text k 107 Rand key 42 65 Clear text A 41 There is an article about OTP at: https://en.wikipedia.org/wiki/One-time pad This project will require the use of the read file() and write file() from Part 1 and the following functions 1. main function with a menu including 3 choices: encrypt file, decrypt file and exit program 2. make_rand key(length of key, key) generates a fixed length string of random chars. 3. encrypt(clear file, key file, cipher file) generates a random key using make_rand_key(), perform the clear text XOR ket text, byte-by-byte, to produce the cipher text string and write both the random key and cipher text strings to file 4. decrypt(key file, cipher file, clear file) uses the cipher text XOR random key to recover the originalStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started