Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Consider the following network. Use distance vector algorithm to calculate and fill in the distance-vector table for node x by answering the following questions.
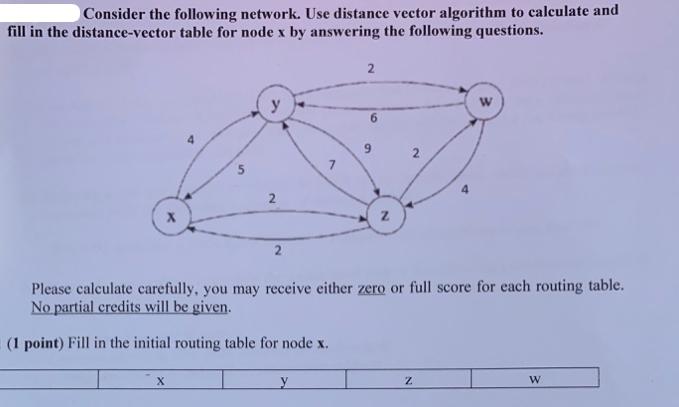
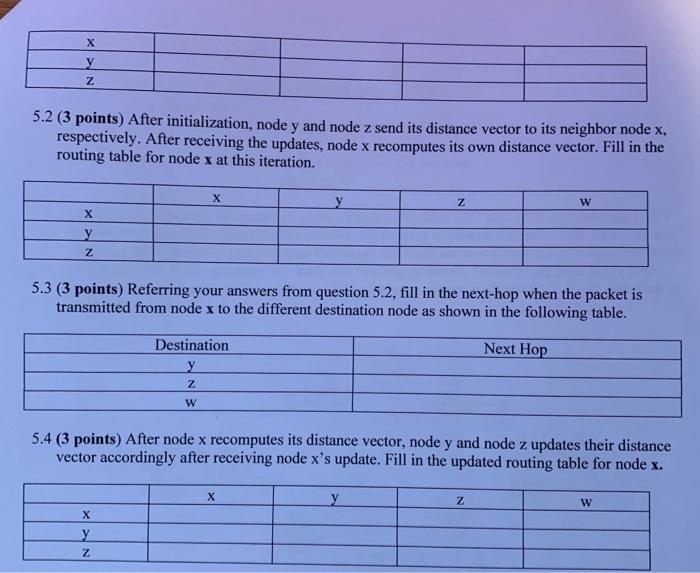
Consider the following network. Use distance vector algorithm to calculate and fill in the distance-vector table for node x by answering the following questions. S X y 2 2 y Z Please calculate carefully, you may receive either zero or full score for each routing table. No partial credits will be given. (1 point) Fill in the initial routing table for node x. 2 Z W X y Z 5.2 (3 points) After initialization, node y and node z send its distance vector to its neighbor node x, respectively. After receiving the updates, node x recomputes its own distance vector. Fill in the routing table for node x at this iteration. X y Z X X y Z 5.3 (3 points) Referring your answers from question 5.2, fill in the next-hop when the packet is transmitted from node x to the different destination node as shown in the following table. Next Hop Destination y Z W Z 5.4 (3 points) After node x recomputes its distance vector, node y and node z updates their distance vector accordingly after receiving node x's update. Fill in the updated routing table for node x. X W Z W
Step by Step Solution
★★★★★
3.51 Rating (148 Votes )
There are 3 Steps involved in it
Step: 1
Remember that signal will be transferred via shortest path in our network Initially one only has con...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


