Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Consider the simplified SSH protocol using certificates only given in the figure below: Notation: - CP= proposed symmetric ciphers; CS= selected symmetric cipher - K=g2bmodp
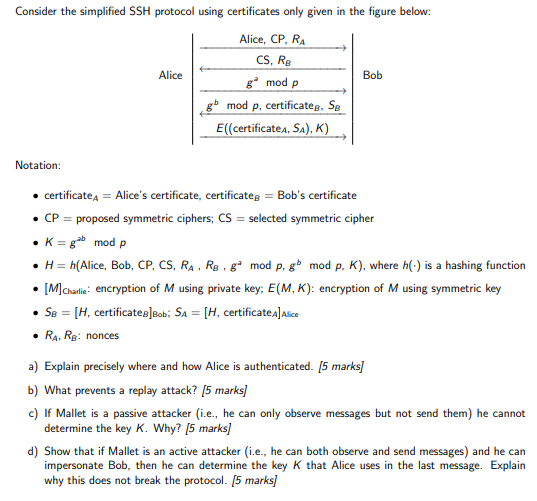 Consider the simplified SSH protocol using certificates only given in the figure below: Notation: - CP= proposed symmetric ciphers; CS= selected symmetric cipher - K=g2bmodp - H=h( Alice, Bob, CP, CS, RA,RB,gamodp,gbmodp,K), where h() is a hashing function - [M]Charlie : encryption of M using private key; E(M,K) : encryption of M using symmetric key - SB=[H,certificateB]Bob;SA=[H,certificateA]Alice - RA,RB : nonces a) Explain precisely where and how Alice is authenticated. [5 marks] b) What prevents a replay attack? [5 marks] c) If Mallet is a passive attacker (i.e., he can only observe messages but not send them) he cannot determine the key K. Why? [5 marks] d) Show that if Mallet is an active attacker (i.e., he can both observe and send messages) and he can impersonate Bob, then he can determine the key K that Alice uses in the last message. Explain why this does not break the protocol. [ 5 marks]
Consider the simplified SSH protocol using certificates only given in the figure below: Notation: - CP= proposed symmetric ciphers; CS= selected symmetric cipher - K=g2bmodp - H=h( Alice, Bob, CP, CS, RA,RB,gamodp,gbmodp,K), where h() is a hashing function - [M]Charlie : encryption of M using private key; E(M,K) : encryption of M using symmetric key - SB=[H,certificateB]Bob;SA=[H,certificateA]Alice - RA,RB : nonces a) Explain precisely where and how Alice is authenticated. [5 marks] b) What prevents a replay attack? [5 marks] c) If Mallet is a passive attacker (i.e., he can only observe messages but not send them) he cannot determine the key K. Why? [5 marks] d) Show that if Mallet is an active attacker (i.e., he can both observe and send messages) and he can impersonate Bob, then he can determine the key K that Alice uses in the last message. Explain why this does not break the protocol. [ 5 marks] Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started