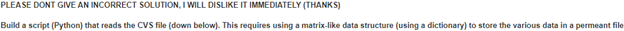
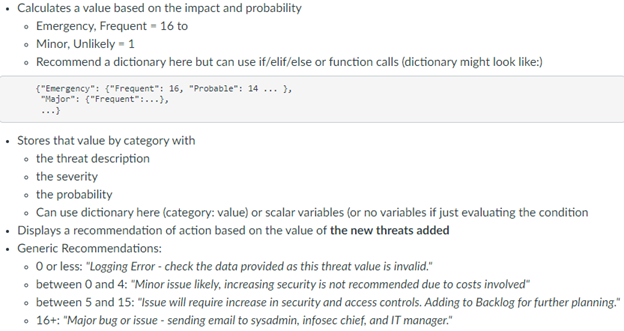
Question
cvs file ID Start time Completion time Provide a Description of the Risk Select its severity 1 12:03 12:11 sabotaging confidential data Major 2 9:51
cvs file
|
ID | Start time | Completion time | Provide a "Description of the Risk" | Select its severity |
| 1 | 12:03 | 12:11 | sabotaging confidential data | Major |
| 2 | 9:51 | 9:54 | Sensitive data | Major |
| 3 | 10:16 | 10:16 | no security system | Moderate |
| 4 | 10:13 | 10:16 | Natural disaster | Emergency |
| 5 | 10:16 | 10:16 | Hurricane | Emergency |
| 6 | 10:16 | 10:16 | Natural disaster | Moderate |
| 7 | 10:16 | 10:16 | Hurricane | Emergency |
| 8 | 10:16 | 10:16 | smashing a window | Minor |
| 9 | 9:51 | 10:17 | hurricane damage | Emergency |
| 10 | 10:16 | 10:17 | Hurricane | Emergency |
| 11 | 10:12 | 10:17 | thief | Major |
| 12 | 9:56 | 10:17 | Robbery | Major |
| 13 | 10:16 | 10:17 | Home Security | Major |
| 14 | 9:54 | 10:17 | Home robbery | Major |
| 15 | 10:16 | 10:26 | Building Maintenance | Major |
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


