Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Diffie Hellman key exchange protocol is used Alice's public key is ' A ' and a private key ' a ' Bob's public key is
Diffie Hellman key exchange protocol is used
Alice's public key is A and a private key a
Bob's public key is B and a private key a
Quin has a public key Q and a private key q
They all know the generator alpha
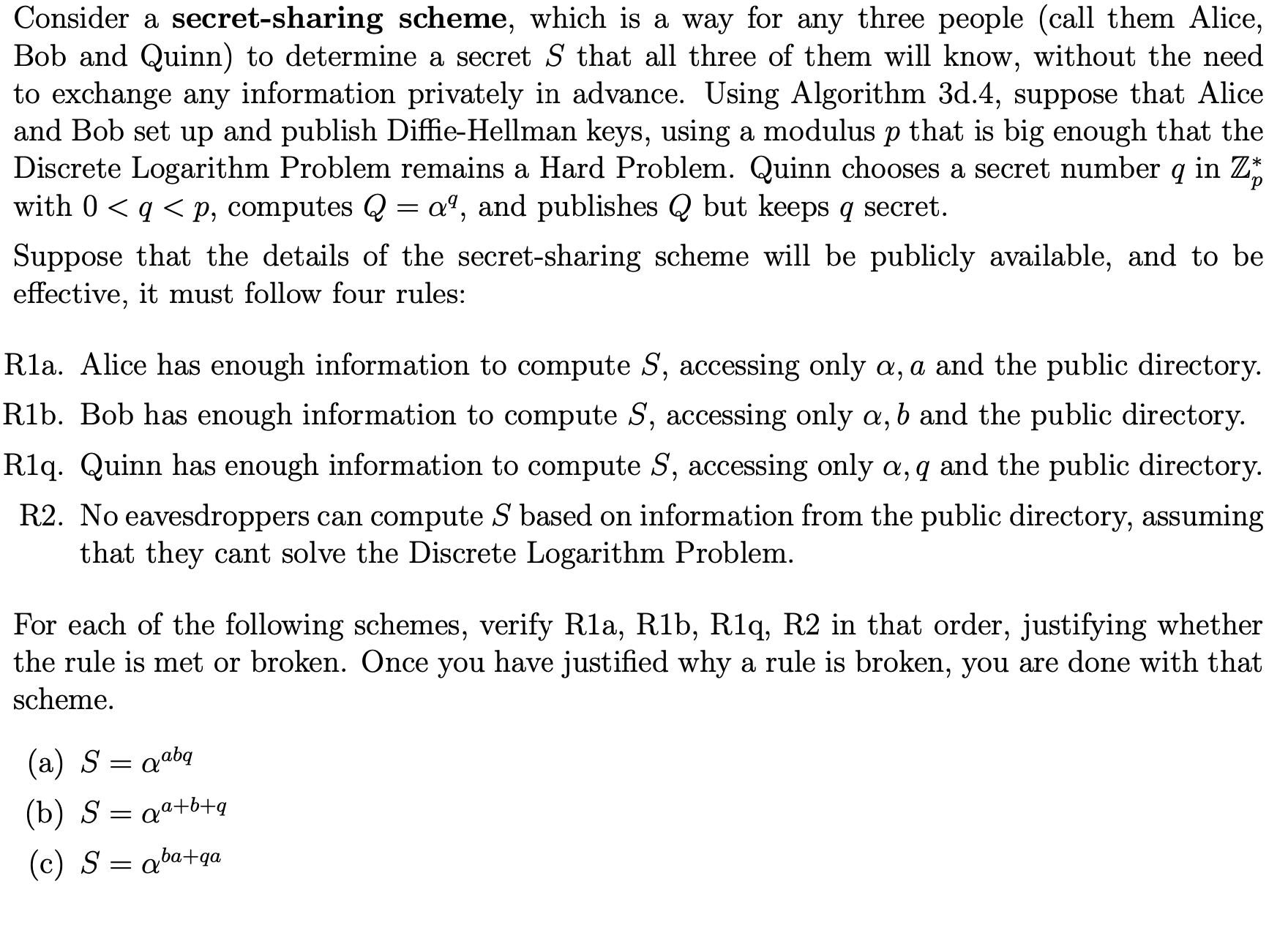
Consider a secretsharing scheme, which is a way for any three people call them Alice,
Bob and Quinn to determine a secret that all three of them will know, without the need
to exchange any information privately in advance. Using Algorithm d suppose that Alice
and Bob set up and publish DiffieHellman keys, using a modulus that is big enough that the
Discrete Logarithm Problem remains a Hard Problem. Quinn chooses a secret number in
with computes and publishes but keeps secret.
Suppose that the details the secretsharing scheme will publicly available, and
effective, must follow four rules:
Alice has enough information compute accessing only a and the public directory.
Bob has enough information compute accessing only and the public directory.
Quinn has enough information compute accessing only and the public directory.
eavesdroppers can compute based information from the public directory, assuming
that they cant solve the Discrete Logarithm Problem.
For each the following schemes, verify that order, justifying whether
the rule met broken. Once you have justified why a rule broken, you are done with that
scheme.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


