Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Do This in Ubuntu ( a Linux distribution)!!! You already know the theory on crypto-systems for assuring various security measures including confidentiality, authentication, authorization and
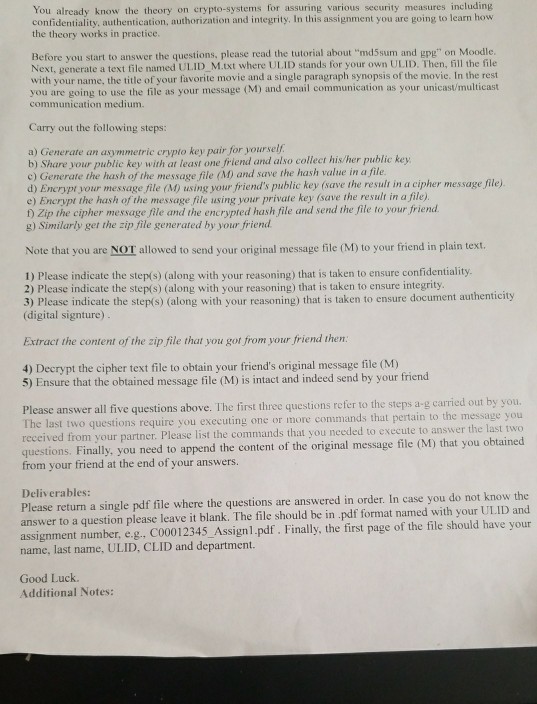
Do This in Ubuntu ( a Linux distribution)!!!
You already know the theory on crypto-systems for assuring various security measures including confidentiality, authentication, authorization and integrity. In this assignment you are going to learn how the theory works in practice Before you start to answer the questions, please read the tutorial about "md5sum and gpg" on Moodle Next, generate a text file named ULID M.txt where ULID stands for your own ULID. Then, fill the file with your name, the title of your favorite movie and a single paragraph synopsis of the movie. In the rest you are going to use the file as your message (M) and email communication as your unicast communication medium. Carry out the following steps: a) Generate an asymmetric crypto key pair for yoursel b) Share your public key with at least one friend and also collect his/her public key c) Generate the hash of the message file (M) and save the hash value in a file d) Encrypt your message file (M) using your friend's public key (save the result in a cipher message file). e) Encrypt the hash of the message file using your private key (save the result in a file) t) Zip the cipher message file and the encrypted hash file and send the file to your friend g) Similarly get the zip file generated by your friend Note that you are NOT allowed to send your original message file (M) to your friend in plain text 1) Please indicate the step(s) (along with your reasoning) that is taken to ensure confidentiality 2) Please indicate the step(s) (along with your reasoning) that is taken to ensure integrity 3) Please indicate the step(s) (along with your reasoning) that is taken to ensure document authenticity (digital signture Extract the content of the zip file that you got from your friend then 4) Decrypt the cipher text file to obtain your friend's original message file (M) 5) Ensure that the obtained message file (M) is intact and indeed send by your friend Please answer all five questions above. The first three questions refer to the steps a-g carried out by you. The last two pertain to the message you questions require you executing one or more commands that list the commands that you needed to execute to answer the last two 1) that you obtained received from your partner. Please questions. Finally, you need to append the content of the origi from your friend at the end of your answers Deliverables: Please return a single pdf file where the questions are answered in order. In case you do not know the answer to a question please leave it blank. The file should be in .pdf format named with your ULID and assignment number, e.g., c00012345_Assign1.pdf. Finally, the first page of the file should have your name, last name, ULID, CLID and department. Good Luck. Additional NotesStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started