Answered step by step
Verified Expert Solution
Question
1 Approved Answer
During your study of T215B, you have been introduced to public key cryptographic systems which play a major role of ensuring the confidentiality of
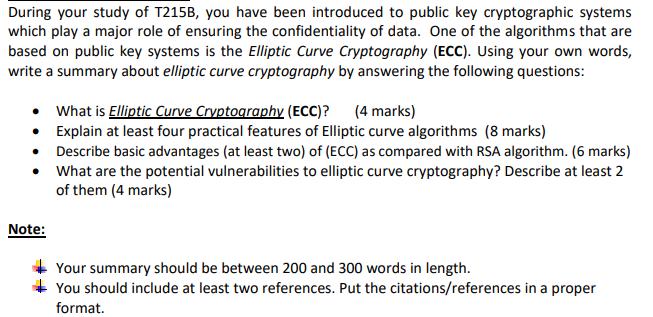
During your study of T215B, you have been introduced to public key cryptographic systems which play a major role of ensuring the confidentiality of data. One of the algorithms that are based on public key systems is the Elliptic Curve Cryptography (ECC). Using your own words, write a summary about elliptic curve cryptography by answering the following questions: What is Elliptic Curve Cryptography (ECC)? (4 marks) Explain at least four practical features of Elliptic curve algorithms (8 marks) Describe basic advantages (at least two) of (ECC) as compared with RSA algorithm. (6 marks) What are the potential vulnerabilities to elliptic curve cryptography? Describe at least 2 of them (4 marks) Note: Your summary should be between 200 and 300 words in length. You should include at least two references. Put the citations/references in a proper format.
Step by Step Solution
There are 3 Steps involved in it
Step: 1
Elliptic Curve Cryptography ECC is a public key cryptographic system that utilizes the mathematics of elliptic curves to provide secure communication and data encryption It is widely used in various a...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started