Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Find at least one malicious software for each of the following categories: (1) Virus, (2) Worms, (3) Spyware, and (4) Trojan Horse. a. Find
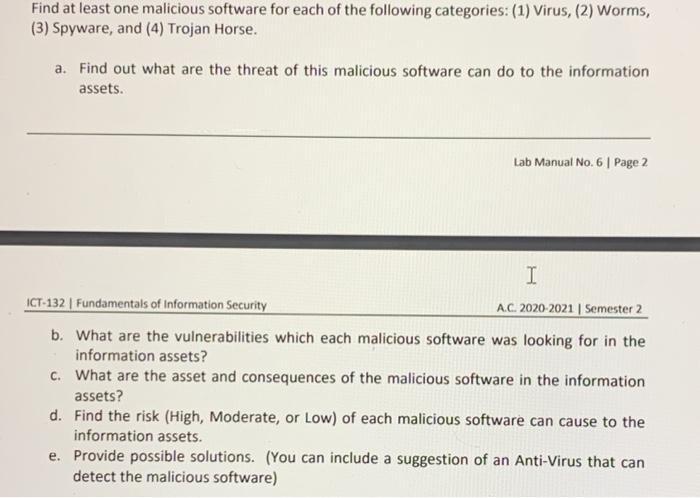
Find at least one malicious software for each of the following categories: (1) Virus, (2) Worms, (3) Spyware, and (4) Trojan Horse. a. Find out what are the threat of this malicious software can do to the information assets. Lab Manual No. 6 | Page 2 I ICT-132 | Fundamentals of Information Security A.C. 2020-2021 | Semester 2 b. What are the vulnerabilities which each malicious software was looking for in the information assets? c. What are the asset and consequences of the malicious software in the information assets? d. Find the risk (High, Moderate, or Low) of each malicious software can cause to the information assets. e. Provide possible solutions. (You can include a suggestion of an Anti-Virus that can detect the malicious software)
Step by Step Solution
★★★★★
3.53 Rating (156 Votes )
There are 3 Steps involved in it
Step: 1
Task 1 Answer Malicious software of 1 Virus MemoryResident Virus Program File Virus Boot Sector Virus Stealth Virus Macro Virus and Email Virus 2 Worms The infamous Iloveyou worm SQL Slammer and MS Bl...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started