Answered step by step
Verified Expert Solution
Question
1 Approved Answer
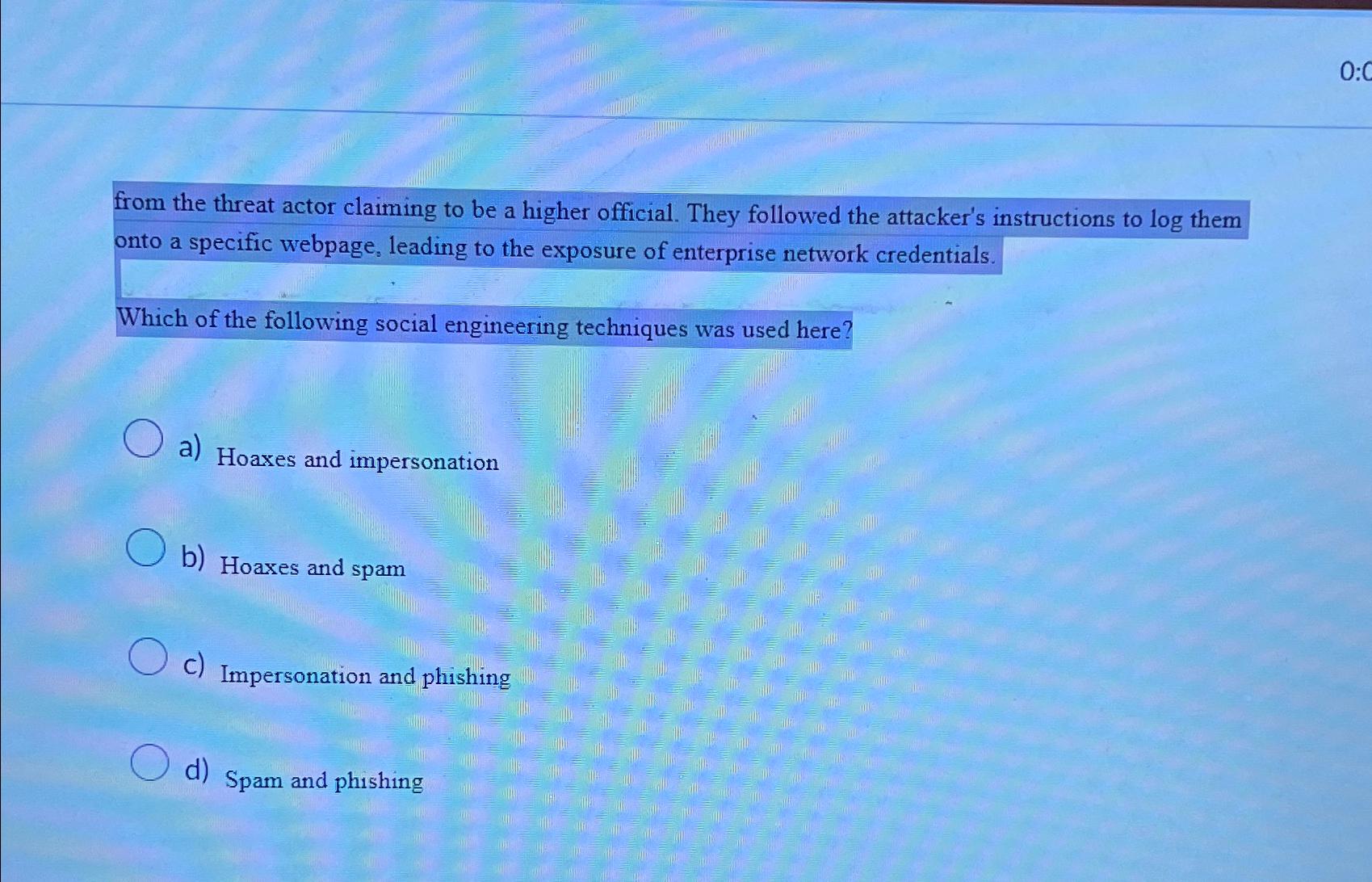
from the threat actor claiming to be a higher official. They followed the attacker's instructions to l o g them onto a specific webpage, leading
from the threat actor claiming to be a higher official. They followed the attacker's instructions to them onto a specific webpage, leading to the exposure of enterprise network credentials.
Which of the following social engineering techniques was used here?
a Hoaxes and impersonation
b Hoaxes and spam
C Impersonation and phishing
d Spam and phishing
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started