Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Help, i dont understand how to solve the problem! Please Help! #21. This problem introduces a hash function similar in to SHA that operates on
Help, i dont understand how to solve the problem! Please Help! 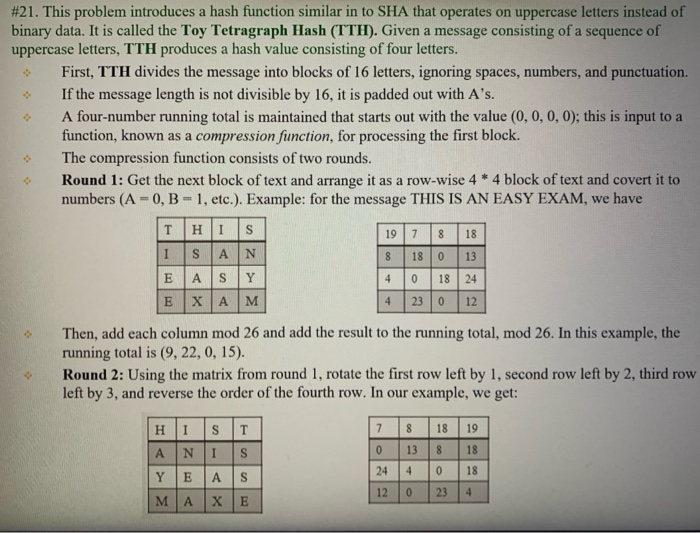
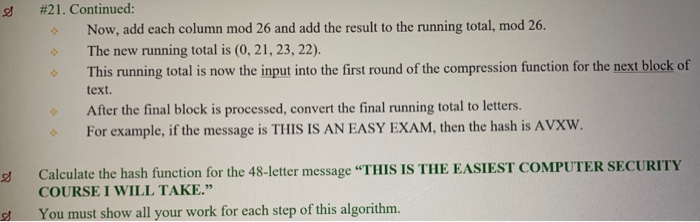
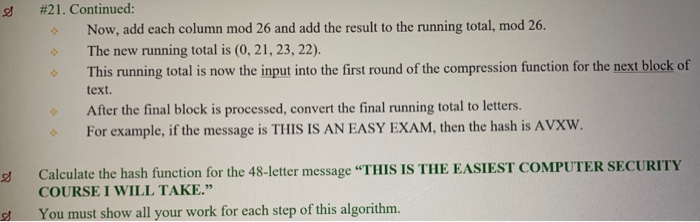
#21. This problem introduces a hash function similar in to SHA that operates on uppercase letters instead of binary data. It is called the Toy Tetragraph Hash (TTH). Given a message consisting of a sequence of uppercase letters, TTH produces a hash value consisting of four letters. First, TTH divides the message into blocks of 16 letters, ignoring spaces, numbers, and punctuation. If the message length is not divisible by 16, it is padded out with A's. A four-number running total is maintained that starts out with the value (0, 0, 0, 0); this is input to a function, known as a compression function, for processing the first block. The compression function consists of two rounds. Round 1: Get the next block of text and arrange it as a row-wise 4 * 4 block of text and covert it to numbers (A - 0, B = 1, etc.). Example: for the message THIS IS AN EASY EXAM, we have THIS 1978 18 ISAN 8 18 13 EASY | 4 o 18 | 24 Ex AM Then, add each column mod 26 and add the result to the running total, mod 26. In this example, the running total is (9, 22, 0, 15). Round 2: Using the matrix from round 1, rotate the first row left by 1, second row left by 2, third row left by 3, and reverse the order of the fourth row. In our example, we get: HIST ANIS Y E AS 7 8 18 19 0 13 8 18 244 0 18 120 234 #21. Continued Now, add each column mod 26 and add the result to the running total, mod 26. The new running total is (0, 21, 23, 22). This running total is now the input into the first round of the compression function for the next block of text. After the final block is processed, convert the final running total to letters. For example, if the message is THIS IS AN EASY EXAM, then the hash is AVXW. Calculate the hash function for the 48-letter message "THIS IS THE EASIEST COMPUTER SECURITY COURSE I WILL TAKE. You must show all your work for each step of this algorithm 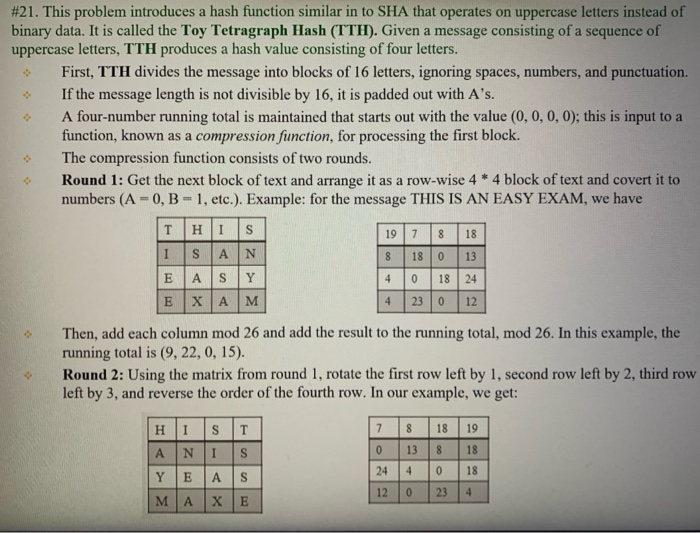
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


