Answered step by step
Verified Expert Solution
Question
1 Approved Answer
HW2.doc 2.pdf This set of homework is for the contents covered in Chapter 3 Data Encryption Standard. 1. Answer the following concept questions about DES
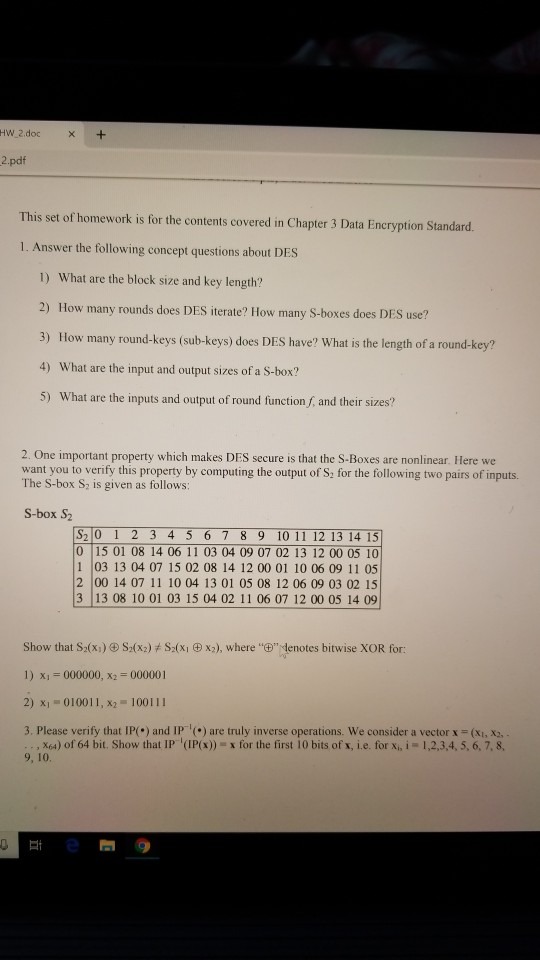
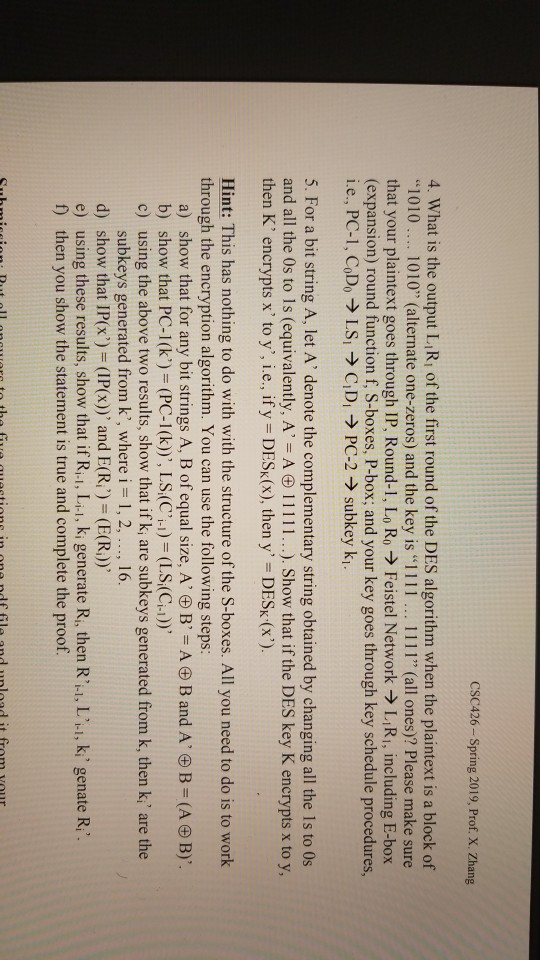
HW2.doc 2.pdf This set of homework is for the contents covered in Chapter 3 Data Encryption Standard. 1. Answer the following concept questions about DES 1) What are the block size and key length? 2) How many rounds does DES iterate? How many S-boxes does DES use? 3) How many round-keys (sub-keys) does DES have? What is the length of a round-key? 4) What are the input and output sizes of a S-box? 5) What are the inputs and output of round function f, and their sizes? 2. One important property which makes DES secure is that the S-Boxes are nonlinear. Here we want you to verify this property by computing the output of S2 for the following two pairs of inputs. The S-box S2 is given as follows: S-box S2 S2 0 1 2 3 4 5 67 8 9 10 11 12 13 14 15 0 15 01 08 14 06 11 03 04 09 07 02 13 12 00 05 10 1 03 13 04 07 15 02 08 14 12 00 01 10 06 09 11 05 2 00 14 07 11 10 04 13 01 05 08 12 06 09 03 02 15 3 13 08 10 01 03 15 04 02 11 06 07 12 00 05 14 09 Show that S2(X1l S2(xz) t S2(X1X2), where"6",denotes bitwise XOR for: 1) X1-000000, X2-000001 2) x1 010011, x2 100111 3. Please verify that IP() and IP) are truly inverse operations. We consider a vector x (xi, X2 , X64) of 64 bit. Show that IP (IP(s)x for the first lobits of, ie. for x.i-12.3.4. 5. 67, 9, 10. CSC426-Spring 2019, Prof. X. Zhang 4. What is the output L Ri of the first round of the DES algorithm when the plaintext is a block of "1010.. 1010" (alternate one-zeros) and the key is "1111 . 1111" (all ones)? Please make sure that your plaintext goes through IP. Round-1, Lo Ro Feste! Network LiRi, including E-box (expansion) round function f, S-boxes, P-box; and your key goes through key schedule procedures, 5. For a bit string A, let A' denote the complementary string obtained by changing all the 1s to Os and all the 0s to Is (equivalently, A. = A 111 1 1 . . .). Show that if the DES key K encrypts x to y, then K, encrypts x' to y, i.e., ifys DESK(X), then y,-DESK'(x). Hint: This has nothing to do with with the structure of the S-boxes. All you need to do is to worlk through the encryption algorithm. You can use the following steps: a) show that for any bit strings A, B of equal size, A' B' A B and A B (A B)' b) show that PC-l(k')# (PC-l(k)), LS/C'i)-(LS,(Ch)), c) using the above two results, show that if k, are subkeys generated from k, then k,' are the subkeys generated from k', where i 1,2,..., 16. d) show, that IP(x) = (IP(x)), and E(R,,)-(E(R)), e) using these results, show that if Ri-I, Li-1, ki generate Ri, then Ri-i, L', ki, genate Ri". f) then you show the statement is true and complete the proof
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started