Answered step by step
Verified Expert Solution
Question
1 Approved Answer
i need the correct answers from the options Question 1 (1 point) Saved Which type of intrusion detection system (IDs) can be considered an expert
i need the correct answers from the options
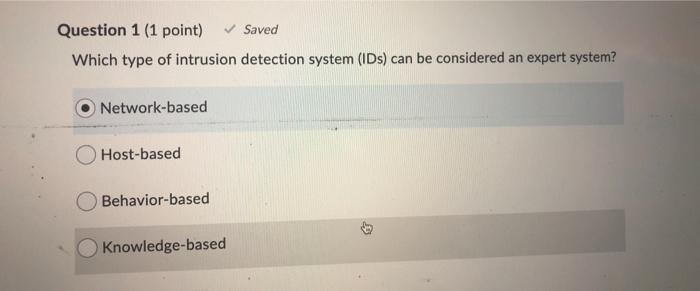
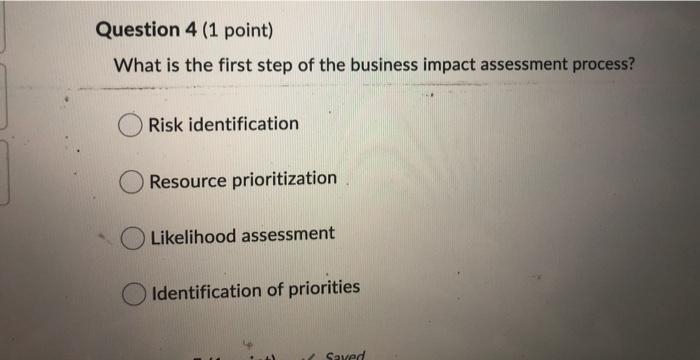
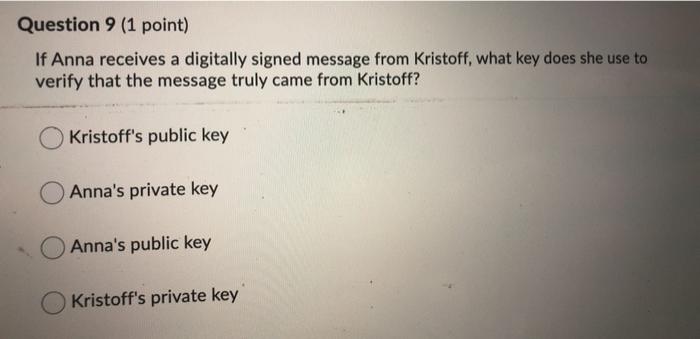
Question 1 (1 point) Saved Which type of intrusion detection system (IDs) can be considered an expert system? Network-based Host-based Behavior-based Knowledge-based Question 4 (1 point) What is the first step of the business impact assessment process? Risk identification Resource prioritization Likelihood assessment Identification of priorities Saved Question 9 (1 point) If Anna receives a digitally signed message from Kristoff, what key does she use to verify that the message truly came from Kristoff? Kristoff's public key Anna's private key Anna's public key Kristoff's private key Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


