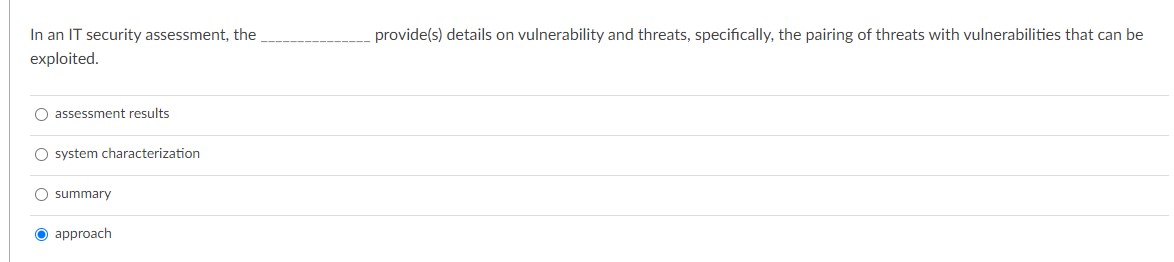
Question: In an IT security assessment, the . provide ( s ) details on vulnerability and threats, specifically, the pairing of threats with vulnerabilities that can
In an IT security assessment, the
provides details on vulnerability and threats, specifically, the pairing of threats with vulnerabilities that can be
exploited.
assessment results
system characterization
summary
approach
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


