Answered step by step
Verified Expert Solution
Question
1 Approved Answer
In Java Programming Language We will design an authentication system where users will be granted access to certain resources. Create a class called com.secretcompany.Authenticate. Create
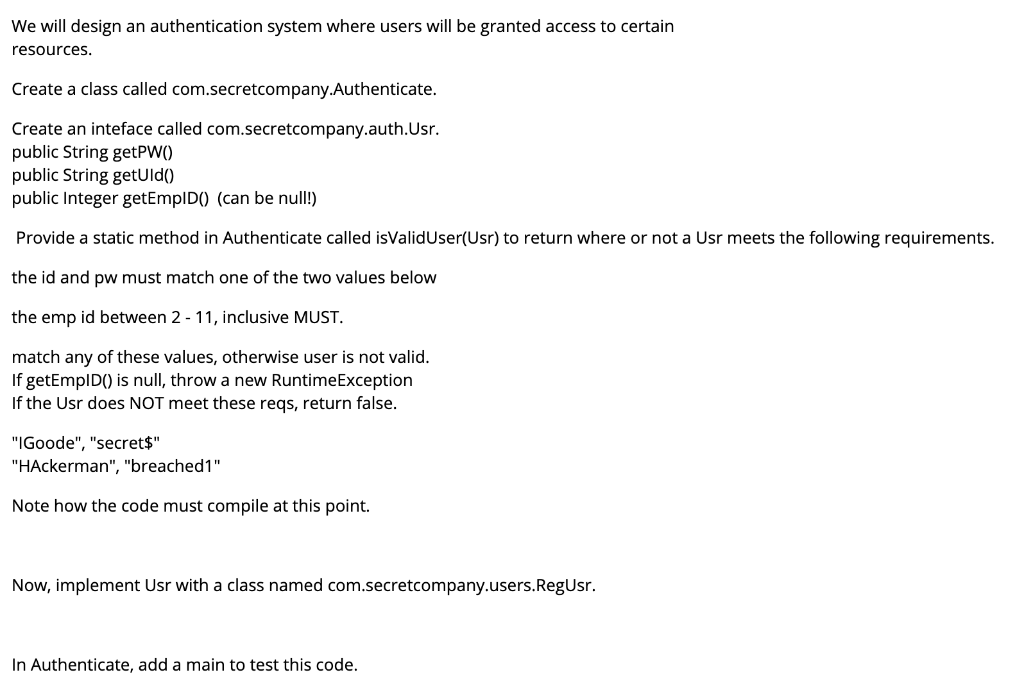
In Java Programming Language
We will design an authentication system where users will be granted access to certain resources. Create a class called com.secretcompany.Authenticate. Create an inteface called com.secretcompany.auth.Usr. public String getPWO) public String getUld() public Integer getEmpId() (can be null!) Provide a static method in Authenticate called isValidUser(Usr) to return where or not a Usr meets the following requirements. the id and pw must match one of the two values below the emp id between 2-11, inclusive MUST. match any of these values, otherwise user is not valid. If getEmpID() is null, throw a new RuntimeException If the Usr does NOT meet these reqs, return false. "IGoode", "secret$" "HAckerman", "breached1" Note how the code must compile at this point. Now, implement Usr with a class named com.secretcompany.users.RegUsr. In Authenticate, add a main to test this code. We will design an authentication system where users will be granted access to certain resources. Create a class called com.secretcompany.Authenticate. Create an inteface called com.secretcompany.auth.Usr. public String getPWO) public String getUld() public Integer getEmpId() (can be null!) Provide a static method in Authenticate called isValidUser(Usr) to return where or not a Usr meets the following requirements. the id and pw must match one of the two values below the emp id between 2-11, inclusive MUST. match any of these values, otherwise user is not valid. If getEmpID() is null, throw a new RuntimeException If the Usr does NOT meet these reqs, return false. "IGoode", "secret$" "HAckerman", "breached1" Note how the code must compile at this point. Now, implement Usr with a class named com.secretcompany.users.RegUsr. In Authenticate, add a main to test this codeStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


