Answered step by step
Verified Expert Solution
Question
1 Approved Answer
In this project, you are going to implement a security-aware task scheduling policy using the CloudSim toolkit. Your implementation should assume a heterogenous environment with
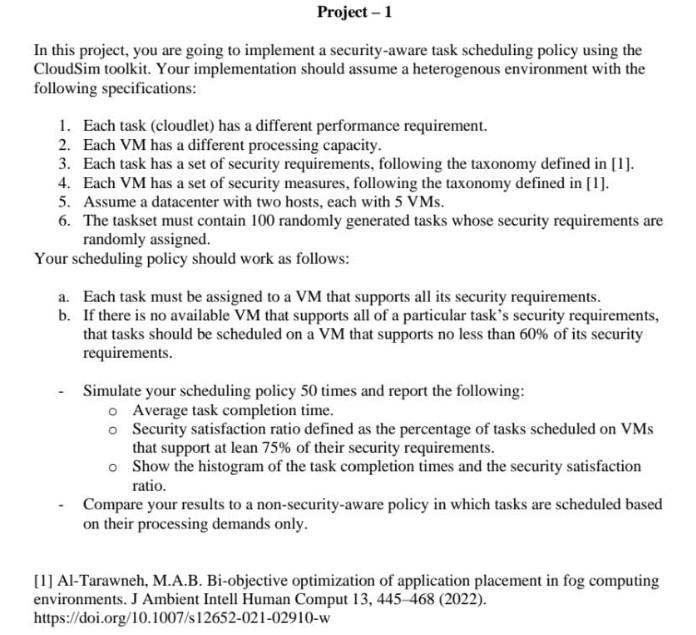
In this project, you are going to implement a security-aware task scheduling policy using the CloudSim toolkit. Your implementation should assume a heterogenous environment with the following specifications: 1. Each task (cloudlet) has a different performance requirement. 2. Each VM has a different processing capacity. 3. Each task has a set of security requirements, following the taxonomy defined in [1]. 4. Each VM has a set of security measures, following the taxonomy defined in [1]. 5. Assume a datacenter with two hosts, each with 5VMs. 6. The taskset must contain 100 randomly generated tasks whose security requirements are randomly assigned. Your scheduling policy should work as follows: a. Each task must be assigned to a VM that supports all its security requirements. b. If there is no available VM that supports all of a particular task's security requirements, that tasks should be scheduled on a VM that supports no less than 60% of its security requirements. - Simulate your scheduling policy 50 times and report the following: Average task completion time. Security satisfaction ratio defined as the percentage of tasks scheduled on VMs that support at lean 75% of their security requirements. Show the histogram of the task completion times and the security satisfaction ratio. - Compare your results to a non-security-aware policy in which tasks are scheduled based on their processing demands only. [1] Al-Tarawneh, M.A.B. Bi-objective optimization of application placement in fog computing environments. J Ambient Intell Human Comput 13, 445-468 (2022). https://doi.org/10.1007/s12652-021-02910-w In this project, you are going to implement a security-aware task scheduling policy using the CloudSim toolkit. Your implementation should assume a heterogenous environment with the following specifications: 1. Each task (cloudlet) has a different performance requirement. 2. Each VM has a different processing capacity. 3. Each task has a set of security requirements, following the taxonomy defined in [1]. 4. Each VM has a set of security measures, following the taxonomy defined in [1]. 5. Assume a datacenter with two hosts, each with 5VMs. 6. The taskset must contain 100 randomly generated tasks whose security requirements are randomly assigned. Your scheduling policy should work as follows: a. Each task must be assigned to a VM that supports all its security requirements. b. If there is no available VM that supports all of a particular task's security requirements, that tasks should be scheduled on a VM that supports no less than 60% of its security requirements. - Simulate your scheduling policy 50 times and report the following: Average task completion time. Security satisfaction ratio defined as the percentage of tasks scheduled on VMs that support at lean 75% of their security requirements. Show the histogram of the task completion times and the security satisfaction ratio. - Compare your results to a non-security-aware policy in which tasks are scheduled based on their processing demands only. [1] Al-Tarawneh, M.A.B. Bi-objective optimization of application placement in fog computing environments. J Ambient Intell Human Comput 13, 445-468 (2022). https://doi.org/10.1007/s12652-021-02910-w
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started