#include
#include
using namespace std ; char messageBuffer [1024];
char msgCopy = NULL;
/ Print a string out to the console @param buffer buffer to be printed /
void printString(char buffer) { void tmp = buffer ; cout
}
int main() { cout > messageBuffer ;
msgCopy = new char[strlen(messageBuffer) + 1]; strcpy(&msgCopy[0] , &messageBuffer [0]);
void functionAddress = (void) printString ; cout
p r i n t S t r i n g (&msgCopy [ 0 ] ) ;
cout > ignore ;
delete [] msgCopy;
return 0; }
1. Enter the code that is on the next page and compile it with static linking, generating a map file. Open up the generated map file and find the address where the messageBuffer and msgCopy variables reside in memory. This will be a hex address. Next, start the programming running and enter a message into the program when prompted. However, make sure the message does not have any spaces in it. Simply use underscores instead. 2. Now, in a second terminal window, determine the pid of the given process. Open up gdb by typing the command gdb attach
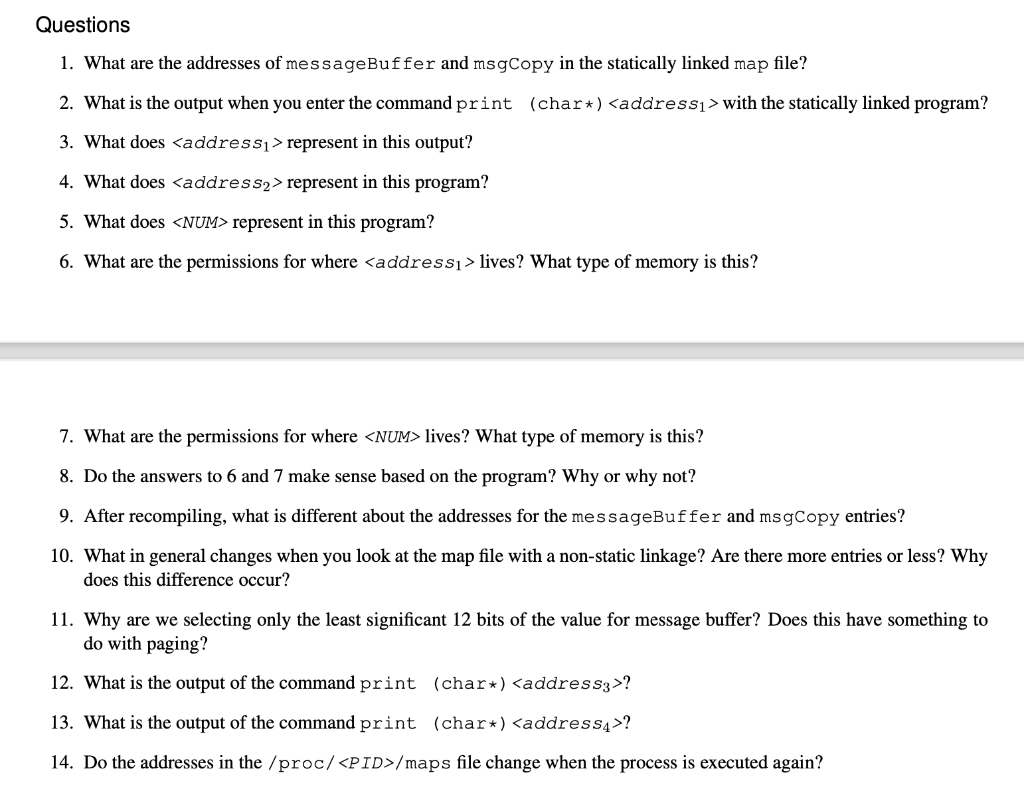
. (Note, you may need to do sudo apt-get install gdb if it is not already installed.) This will attach to the running program. At the console, enter the command print (char*) where is the hex address in the map file for messageBuffer. Take a look at the output. Next issue the command print /x +() where is the address of msgCopy in memory. This will print out a hex number which we will call . Then issue the command print (char*) (). What is printed out? 3. Now change into the directory /proc/ where is the process ID of the process. Cat out the file maps. From the file, determine which segment of memory each of these addresses resides within. Take a look at the permissions for that segment. (Permissions are r, w, x, p, etc.) 4. In the gdb window, type quit to exit out of the debugger, and then enter a key to allow the program to complete. Re- compile the code without the -static option. Open up the map file and find the messageBuffer and msg Copy entries in the map file. Look at them carefully. What do you notice? 5. Start the program running again. Run the program again, being careful not to put any spaces in the entry. Deter- mine the pid of the process again and issue the command gdb attach . In another window, change into /proc/ and again cat out the contents of the maps file. What is different? Find the starting address for the program data segment (hint: this will be readable, writeable, and pageable and have the name of the program in it). Take the least significant 12 bits of the value for messageBuffer from the map file and or them into the starting ad- dress for the data segment, giving you and address we will call . In gdb, issue the command print (char*) . What is output? Now take the least significant 12 bits of the msgCopy value in the map file and repeat what we did, creating . Issue the command print (char*) . What happens? 6. Now exit the program and start it running again. Take a look at the /proc//maps file for the second running process. Are the addresses the same? Questions 1. What are the addresses of messageBuffer and msgCopy in the statically linked map file? 2. What is the output when you enter the command print (char*) with the statically linked program? 3. What does represent in this output? 4. What does represent in this program? 5. What does represent in this program? 6. What are the permissions for where lives? What type of memory is this? 7. What are the permissions for where lives? What type of memory is this? 8. Do the answers to 6 and 7 make sense based on the program? Why or why not? 9. After recompiling, what is different about the addresses for the messageBuffer and msgCopy entries? 10. What in general changes when you look at the map file with a non-static linkage? Are there more entries or less? Why does this difference occur? 11. Why are we selecting only the least significant 12 bits of the value for message buffer? Does this have something to do with paging? 12. What is the output of the command print (char*) ? 13. What is the output of the command print (char*) ? 14. Do the addresses in the /proc//maps file change when the process is executed again