Answered step by step
Verified Expert Solution
Question
1 Approved Answer
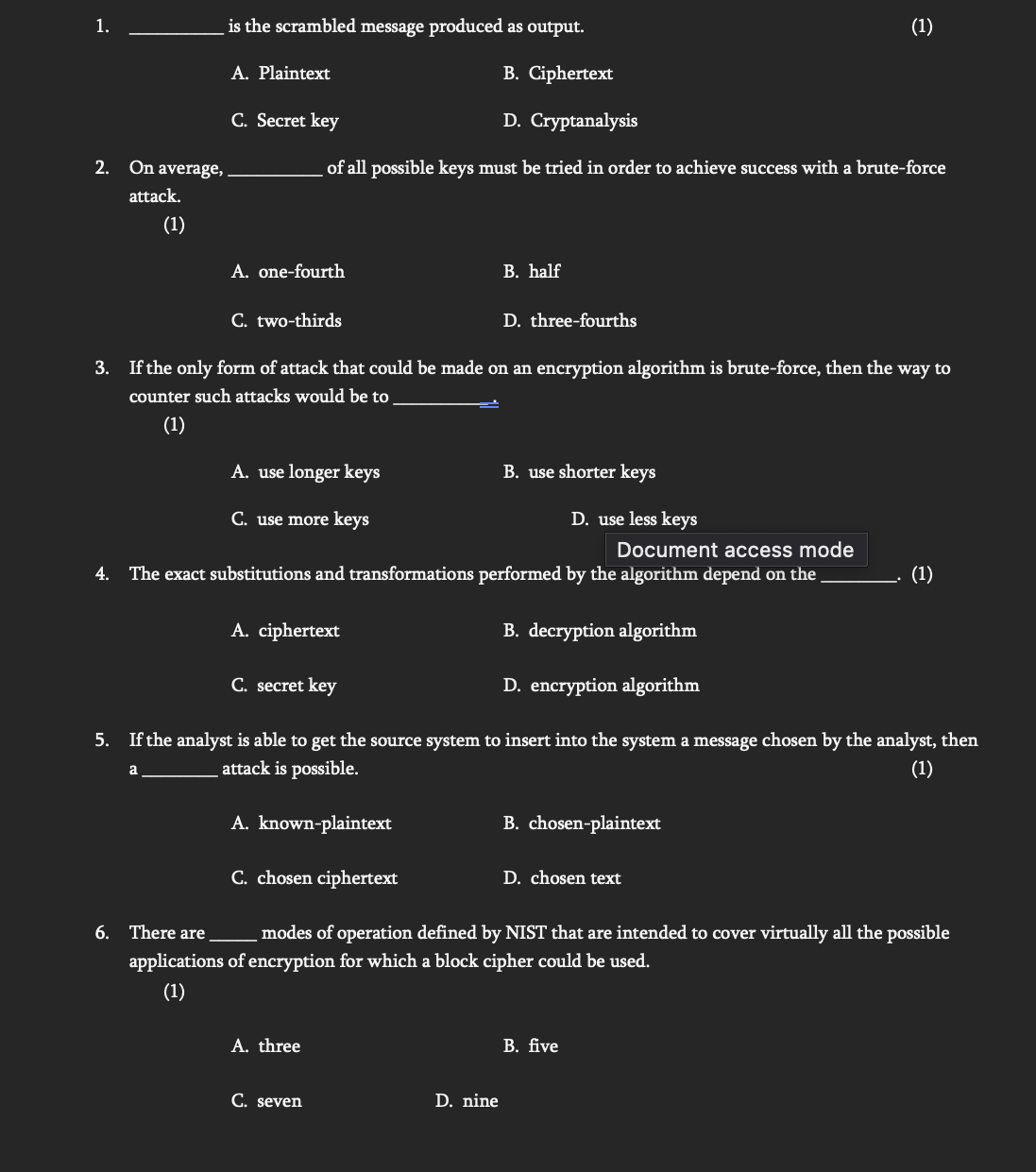
is the scrambled message produced as output. A . Plaintext B . Ciphertext C . Secret key D . Cryptanalysis On average, of all possible
is the scrambled message produced as output.
A Plaintext
B Ciphertext
C Secret key
D Cryptanalysis
On average,
of all possible keys must be tried in order to achieve success with a bruteforce
attack.
A onefourth
B half
C twothirds
D threefourths
If the only form of attack that could be made on an encryption algorithm is bruteforce, then the way to
counter such attacks would be to
A use longer keys
B use shorter keys
C use more keys
D use less keys
Document access mode
The exact substitutions and transformations performed by the algorithm depend on the
A ciphertext
B decryption algorithm
C secret key
D encryption algorithm
If the analyst is able to get the source system to insert into the system a message chosen by the analyst, then
a
attack is possible.
A knownplaintext
B chosenplaintext
C chosen ciphertext
D chosen text
There are
modes of operation defined by NIST that are intended to cover virtually all the possible
applications of encryption for which a block cipher could be used.
A three
B five
C seven
D nine
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


