Answered step by step
Verified Expert Solution
Question
1 Approved Answer
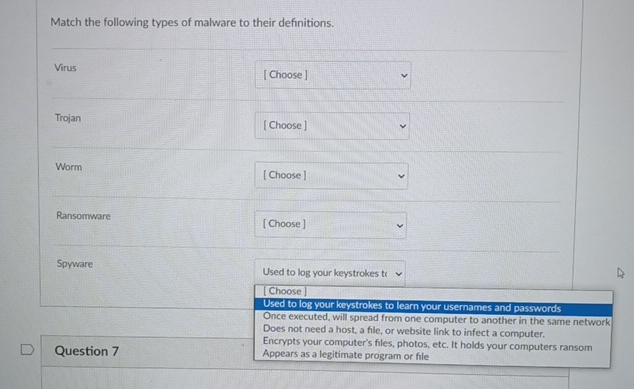
Match the following types of malware to their definitions. Virus Trojan Worm Ransomware Spyware Used to log your keystrokes ti [ Choose ] Used to
Match the following types of malware to their definitions.
Virus
Trojan
Worm
Ransomware
Spyware
Used to log your keystrokes ti
Choose
Used to log your keystrokes to learn your usernames and passwords
Once executed, will spread from one computer to another in the same network Does not need a host, a file, or website link to infect a computer.
Encrypts your computer's files, photos, etc. It holds your computers ransom Appears as a legitimate program or file
Question
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


