MAX DIVISOR TREE Let a tree exists with the root value N. The property of this...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
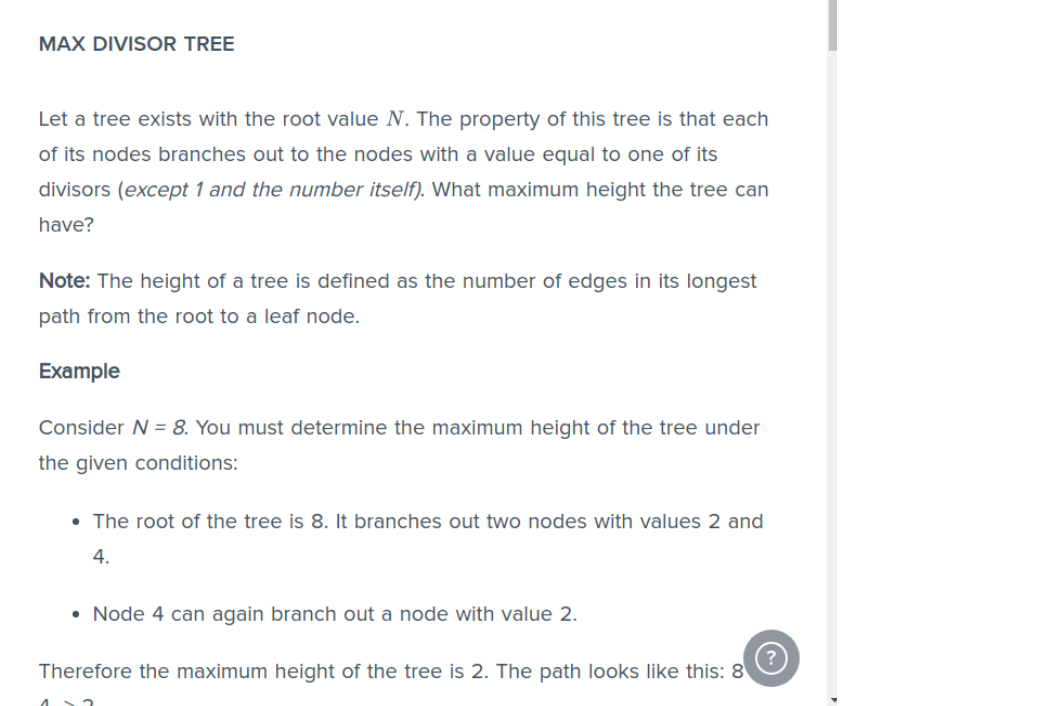
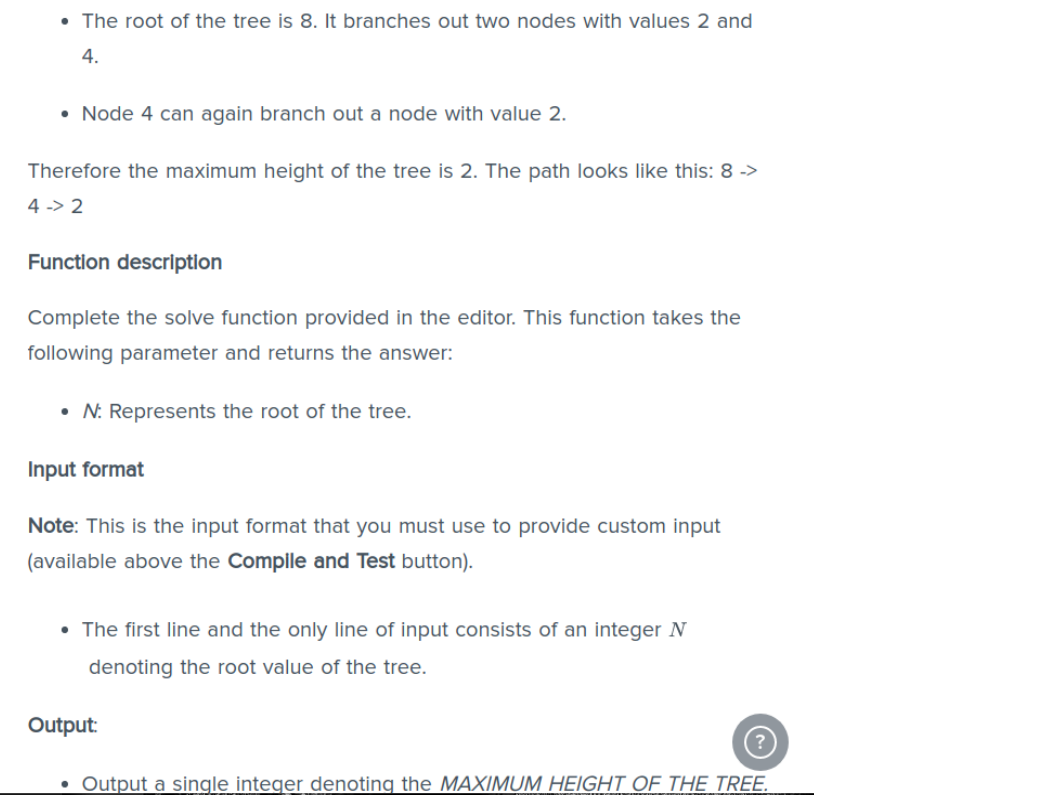
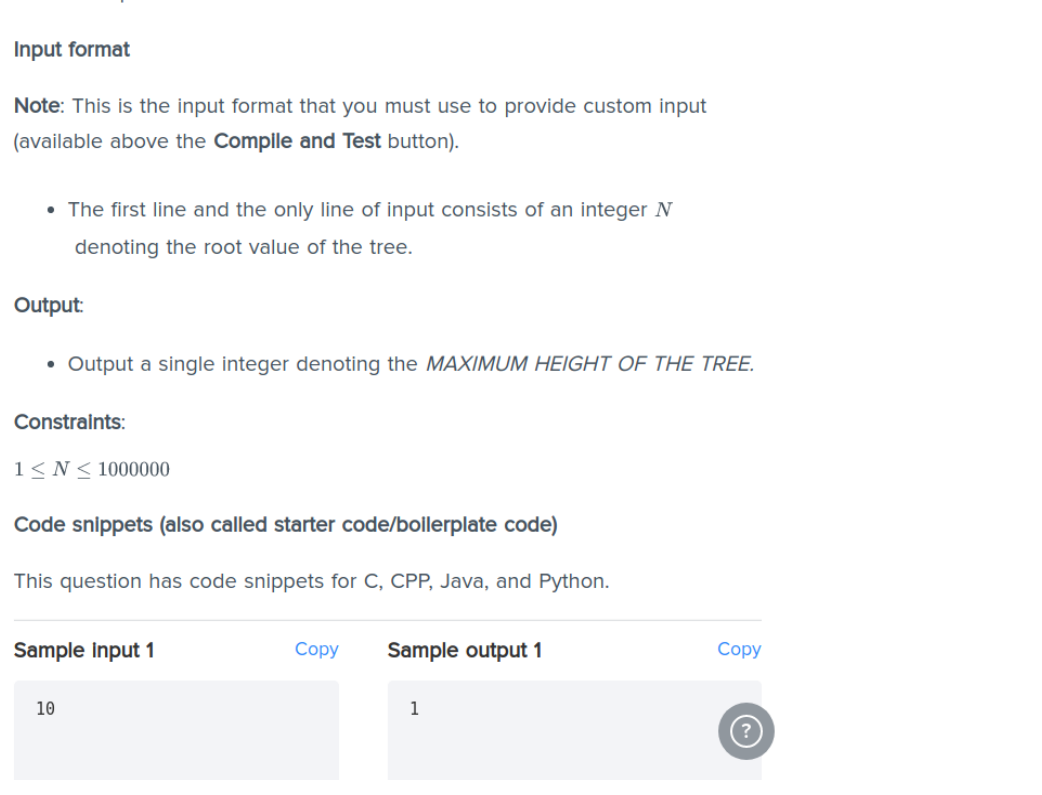
MAX DIVISOR TREE Let a tree exists with the root value N. The property of this tree is that each of its nodes branches out to the nodes with a value equal to one of its divisors (except 1 and the number itself). What maximum height the tree can have? Note: The height of a tree is defined as the number of edges in its longest path from the root to a leaf node. Example Consider N = 8. You must determine the maximum height of the tree under the given conditions: • The root of the tree is 8. It branches out two nodes with values 2 and 4. • Node 4 can again branch out a node with value 2. Therefore the maximum height of the tree is 2. The path looks like this: 8 (~.) • The root of the tree is 8. It branches out two nodes with values 2 and 4. • Node 4 can again branch out a node with value 2. Therefore the maximum height of the tree is 2. The path looks like this: 8 -> 4->2 Function description Complete the solve function provided in the editor. This function takes the following parameter and returns the answer: • N: Represents the root of the tree. Input format Note: This is the input format that you must use to provide custom input (available above the Compile and Test button). • The first line and the only line of input consists of an integer N denoting the root value of the tree. Output: • Output a single integer denoting the MAXIMUM HEIGHT OF THE TREE. Input format Note: This is the input format that you must use to provide custom input (available above the Compile and Test button). • The first line and the only line of input consists of an integer N denoting the root value of the tree. Output: • Output a single integer denoting the MAXIMUM HEIGHT OF THE TREE. Constraints: 1≤N≤ 1000000 Code snippets (also called starter code/bollerplate code) This question has code snippets for C, CPP, Java, and Python. Sample Input 1 10 Copy Sample output 1 1 Copy MAX DIVISOR TREE Let a tree exists with the root value N. The property of this tree is that each of its nodes branches out to the nodes with a value equal to one of its divisors (except 1 and the number itself). What maximum height the tree can have? Note: The height of a tree is defined as the number of edges in its longest path from the root to a leaf node. Example Consider N = 8. You must determine the maximum height of the tree under the given conditions: • The root of the tree is 8. It branches out two nodes with values 2 and 4. • Node 4 can again branch out a node with value 2. Therefore the maximum height of the tree is 2. The path looks like this: 8 (~.) • The root of the tree is 8. It branches out two nodes with values 2 and 4. • Node 4 can again branch out a node with value 2. Therefore the maximum height of the tree is 2. The path looks like this: 8 -> 4->2 Function description Complete the solve function provided in the editor. This function takes the following parameter and returns the answer: • N: Represents the root of the tree. Input format Note: This is the input format that you must use to provide custom input (available above the Compile and Test button). • The first line and the only line of input consists of an integer N denoting the root value of the tree. Output: • Output a single integer denoting the MAXIMUM HEIGHT OF THE TREE. Input format Note: This is the input format that you must use to provide custom input (available above the Compile and Test button). • The first line and the only line of input consists of an integer N denoting the root value of the tree. Output: • Output a single integer denoting the MAXIMUM HEIGHT OF THE TREE. Constraints: 1≤N≤ 1000000 Code snippets (also called starter code/bollerplate code) This question has code snippets for C, CPP, Java, and Python. Sample Input 1 10 Copy Sample output 1 1 Copy
Expert Answer:

Related Book For 

Introduction to Algorithms
ISBN: 978-0262033848
3rd edition
Authors: Thomas H. Cormen, Charles E. Leiserson, Ronald L. Rivest
Posted Date:
Students also viewed these programming questions
-
A major theme of this chapter is that our cognitive processes influence ethical decision making. Use the theme to comment on the following statement, which various religions claim as their own and...
-
One of the messages of this chapter is that while Monte Carlo is a clever method of calculation, it shouldnt be used when some better method exists. The MC valuation of in section 25.2, for example,...
-
The implication of this diagram is that elimination of what structures would prevent or eradicate eyeblink conditioning? Stelioto col Parale foren Besket col Punrje Ceroler cotox Golg Grare ol Musey...
-
A 15.00 g metal sphere was found to have a diameter of 1.85 cm. The volume of a sphere is V = (4/3)r. Calculate the density of the sphere and assuming that the sphere is made out of one of the...
-
Jaycie Phelps Inc. acquired 20% of the outstanding common stock of Theresa Kulikowski Inc. on December 31, 2008. The purchase price was $1,200,000 for 50,000 shares. Kulikowski Inc. declared and paid...
-
Use technology and the frequency distribution from Try It Yourself 2 to construct a frequency histogram that represents the ages of the 50 most powerful women listed on page 39. 26, 31, 35, 37, 43,...
-
Use prime factorization to find the LCM of 20 and 28.
-
Edington Electronics Inc. produces and sells two models of pocket calculators, XQ-103 and XQ-104. The calculators sell for $12 and $25, respectively. Because of the intense competition Edington...
-
solve this quickly. Blossom Products Company uses a job order cost system. For a number of months, there has been an ongoing rift between the sales department and the production department concerning...
-
Using a computer spreadsheet, set up a cash flow statement to capture the anticipated cash flow in the following case study scenario. Cash Flow Planning Exercise This exercise is an opportunity to...
-
Ethical Finance brings Value to Society, do you think Islamic finance also brings value to society? What are the Islamic social financing channels?
-
How do decentralized finance (DeFi) platforms utilize smart contracts and decentralized autonomous organizations (DAOs) to create novel financial instruments and protocols, enabling peer-to-peer...
-
The following unadjusted trial balance has been prepared for Sellit Realty Corporation at the end of its first year of operations, December 31, 2022 Acct. No. Account 101 Cash 110 Accounts receivable...
-
Most spreadsheets do not have a built in formula to calculate the payback period. Write a VBA script that calculates the payback period for a project. Year Cash Flow 0 $ 6 2 5 , 0 0 0 , 0 0 0 1 ...
-
On January 1, 2022, the Sheridan Company budget committee has reached agreement on the following data for the 6 months ending June 30, 2022. Sales units: Ending raw materials inventory: Ending...
-
Southwestern Wear Inc. has the following balance sheet: Current assets Fixed assets $1,875,000 Accounts payable 1,875,000 Notes payable Subordinated debentures Total assets Total debt Common equity...
-
https://cdn.ymaws.com/www.psichi.org/resource/resmgr/journal_2018/23-1_Spring_Miska.pdf State Miska, Hemmesch, and Buswell's (2018) two hypotheses for this line of research. 2. Identify the research...
-
Pearl Medavoy will invest $10,240 a year for 20 years in a fund that will earn 10% annual interest. . If the first payment into the fund occurs today, what amount will be in the fund in 20 years? If...
-
What is the largest k such that if you can multiply 3 3 matrices using k multiplications (not assuming commutativity of multiplication), then you can multiply n n matrices in time o(n lg 7 )? What...
-
Show that if an algorithm makes at most a constant number of calls to polynomial time subroutines and performs an additional amount of work that also takes polynomial time, then it runs in polynomial...
-
Show that by making a different inductive hypothesis, we can overcome the difficulty with the boundary condition T(1) = 1 for recurrence (4.19) without adjusting the boundary conditions for the...
-
In the 1960s, what legendary U.S. crime- fighter began to emphasize fraud detection in his federal government bureau?
-
What was the title and who was the author of the first forensic book?
-
What book introduced the structural and behavioral consideration of fraud? What is the iceberg theory?

Study smarter with the SolutionInn App