Question
MIPS ASSIGNMENT DO NOT CHANGE ANY OF THIS BOILERPLATE CODE!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! .data Key: .word 0x1234ABCD Messagetext: .asciiz This string will be encrypted. Output1: .asciiz Original message
MIPS ASSIGNMENT
 DO NOT CHANGE ANY OF THIS BOILERPLATE CODE!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
DO NOT CHANGE ANY OF THIS BOILERPLATE CODE!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
.data
Key:
.word 0x1234ABCD
Messagetext:
.asciiz "This string will be encrypted."
Output1:
.asciiz "Original message text: "
Output2:
.asciiz " Encrypted text (hex): "
Output3:
.asciiz " Decrypted text: "
CR:
.asciiz " "
.align 2
Ciphertext:
.space 40
.align 2
Plaintext:
.space 40
.text #most of this code is string printing
la $a0, Output1
addi $v0, $0, 4
syscall
la $a0, Messagetext
addi $v0, $0, 4
syscall
la $a0, CR
addi $v0, $0, 4
syscall
la $a0, Messagetext
la $a1, Ciphertext
jal Encrypt #encrypt the message text to the ciphertext buffer
la $a0, Output2
addi $v0, $0, 4
syscall
la $a0, Ciphertext
jal PrintBufferHex #print out the hex of the ciphertext
la $a0, CR
addi $v0, $0, 4
syscall
addi $a0, $a1, 0
la $a1, Plaintext
jal Decrypt #decrypt the cipher text to plaintext
la $a0, Output3
addi $v0, $0, 4
syscall
addi $a0, $a1, 0
addi $v0, $0, 4
syscall
la $a0, CR
addi $v0, $0, 4
syscall
addi $v0, $0, 10 #end of program
syscall
PrintBufferHex: #subroutine which prints buffer in hex
addi $sp, $sp, -4
sw $a0, ($sp)
addi $t0, $a0, 0
addi $t1, $0, 10
PrintLoop:
addi $v0, $0, 34
lw $a0, ($t0)
syscall
la $a0, CR
addi $v0, $0, 4
syscall
addi $t0, $t0, 4
addi $t1, $t1, -1
bne $t1, $0, PrintLoop
lw $a0, ($sp)
addi $sp, $sp, 4
jr $ra
Encrypt:
#your code goes here
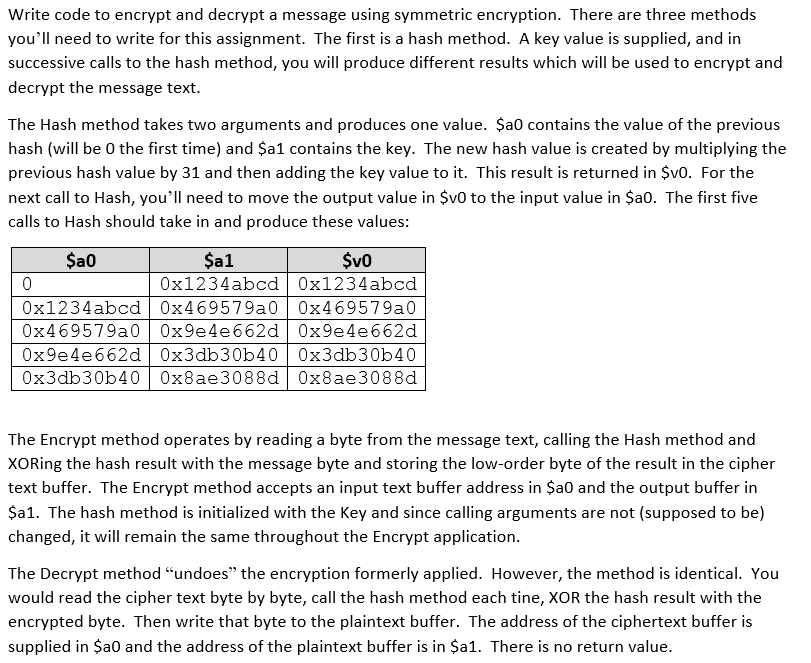
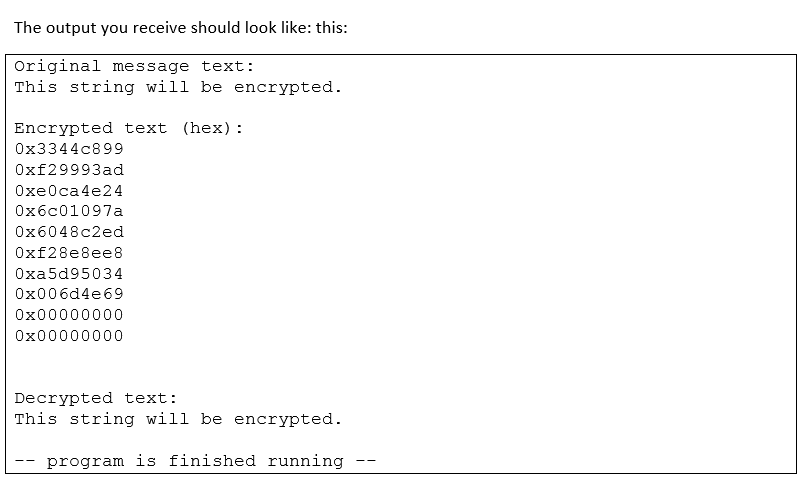
Write code to encrypt and decrypt a message using symmetric encryption. There are three methods you'll need to write for this assignment. The first is a hash method. A key value is supplied, and in successive calls to the hash method, you will produce different results which will be used to encrypt and decrypt the message text The Hash method takes two arguments and produces one value. $a0 contains the value of the previous hash (will be 0 the first time) and Sa1 contains the key. The new hash value is created by multiplying the previous hash value by 31 and then adding the key value to it. This result is returned in SvO. For the next call to Hash, you'll need to move the output value in $vO to the input value in Sa0. The first five calls to Hash should take in and produce these values: a0 al SvO 0 0x1234abcd 0x469579a0 0x469579a0 0x469579a00x9e4e662d 0x9e4e662d 0x9e4e662d 0x3db30b40 0z3db30b40 0x3db30b400x8ae3088d 0x8ae3088d 0x1234abcd 0x1234abcd The Encrypt method operates by reading a byte from the message text, calling the Hash method and XORing the hash result with the message byte and storing the low-order byte of the result in the cipher text buffer. The Encrypt method accepts an input text buffer address in $a0 and the output buffer in a1. The hash method is initialized with the Key and since calling arguments are not (supposed to be) changed, it will remain the same throughout the Encrypt application. The Decrypt method "undoes" the encryption formerly applied. However, the method is identical. You would read the cipher text byte by byte, call the hash method each tine, XOR the hash result with the encrypted byte. Then write that byte to the plaintext buffer. The address of the ciphertext buffer is supplied in a0 and the address of the plaintext buffer is in $a1. There is no return valueStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started