Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Objective: The objective of this project is to install and run virtual machines with various IPS / IDS tools, evaluate their effectiveness, and compare their
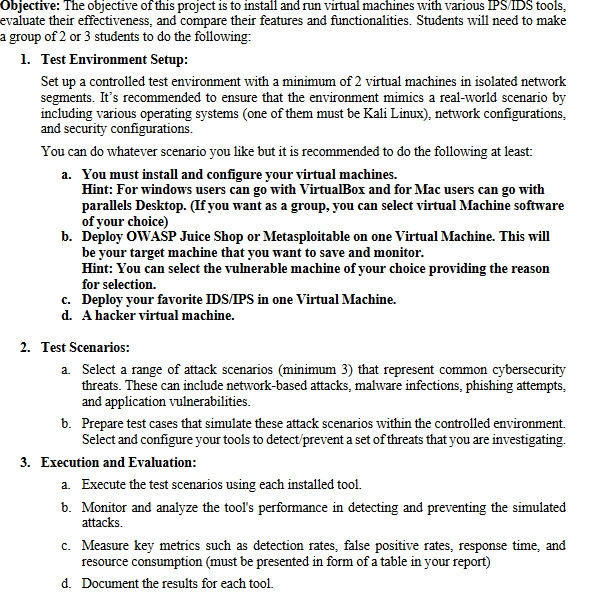
Objective: The objective of this project is to install and run virtual machines with various IPSIDS tools, evaluate their effectiveness, and compare their features and functionalities. Students will need to make a group of or students to do the following:
Test Environment Setup:
Set up a controlled test environment with a minimum of virtual machines in isolated network segments. It's recommended to ensure that the environment mimics a realworld scenario by including various operating systems one of them must be Kali Linux network configurations, and security configurations.
You can do whatever scenario you like but it is recommended to do the following at least:
a You must install and configure your virtual machines.
Hint: For windows users can go with VirtualBox and for Mac users can go with parallels Desktop. If you want as a group, you can select virtual Machine software of your choice
b Deploy OWASP Juice Shop or Metasploitable on one Virtual Machine. This will be your target machine that you want to save and monitor.
Hint: You can select the vulnerable machine of your choice providing the reason for selection.
c Deploy your favorite IDSIPS in one Virtual Machine.
d A hacker virtual machine.
Test Scenarios:
a Select a range of attack scenarios minimum that represent common cybersecurity threats. These can include networkbased attacks, malware infections, phishing attempts, and application vulnerabilities.
b Prepare test cases that simulate these attack scenarios within the controlled environment. Select and configure your tools to detectprevent a set of threats that you are investigating.
Execution and Evaluation:
a Execute the test scenarios using each installed tool.
b Monitor and analyze the tool's performance in detecting and preventing the simulated attacks.
c Measure key metrics such as detection rates, false positive rates, response time, and resource consumption must be presented in form of a table in your report
d Document the results for each tool.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


