on Consider the following protocol designed so that X and Y will decide on fresh secret...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
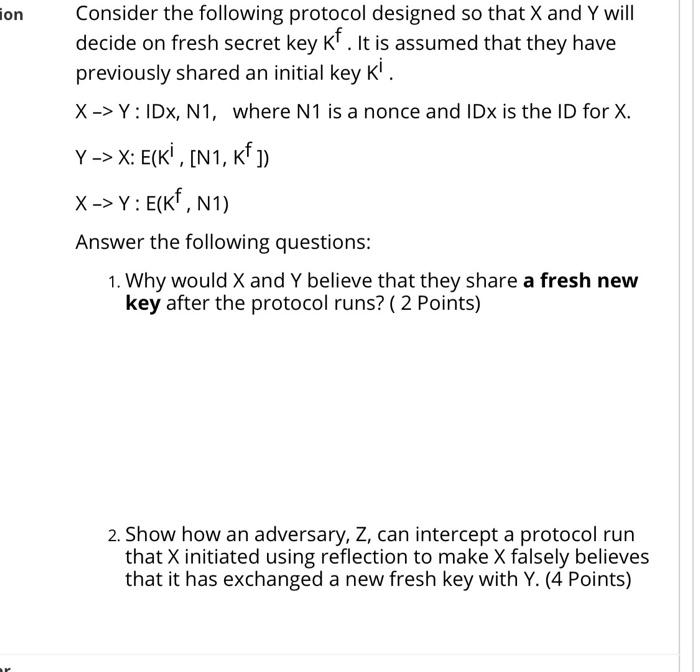
on Consider the following protocol designed so that X and Y will decide on fresh secret key Kf. It is assumed that they have previously shared an initial key K'. X->Y: IDX, N1, where N1 is a nonce and IDX is the ID for X. Y-> X: E(KI, [N1, KF ]) X->Y: E(KF, N1) Answer the following questions: 1. Why would X and Y believe that they share a fresh new key after the protocol runs? ( 2 Points) 2. Show how an adversary, Z, can intercept a protocol run that X initiated using reflection to make X falsely believes that it has exchanged a new fresh key with Y. (4 Points) on Consider the following protocol designed so that X and Y will decide on fresh secret key Kf. It is assumed that they have previously shared an initial key K'. X->Y: IDX, N1, where N1 is a nonce and IDX is the ID for X. Y-> X: E(KI, [N1, KF ]) X->Y: E(KF, N1) Answer the following questions: 1. Why would X and Y believe that they share a fresh new key after the protocol runs? ( 2 Points) 2. Show how an adversary, Z, can intercept a protocol run that X initiated using reflection to make X falsely believes that it has exchanged a new fresh key with Y. (4 Points)
Expert Answer:
Answer rating: 100% (QA)
In our given example the two parties X and Y already share a key Ki They then wish to share a fresh secret key Kf 1 Why would X and Y believe that the... View the full answer

Related Book For 

Introduction to Probability
ISBN: 978-0716771098
1st edition
Authors: Mark Daniel Ward, Ellen Gundlach
Posted Date:
Students also viewed these programming questions
-
A small business has found that the cost to produce x units of its product can be modeled as a linear function. The monthly cost to produce 150 units is $1656 while it costs $1968 to produce 450...
-
Exercise 16-42 (Algo) Variable Cost Variances (LO 16-5) Records at the Farnsworth Corporation contained the following data for the most recent period of activity: Actual total direct labor cost...
-
Data set Theory Assume an informational record with one association parent including matches (a, b) where a can't try not to be a parent of b. (a) Write a Datalog demand which gives the graph of...
-
Q1-Mutual funds provide the following for their shareholders. A. diversification B. professional management C. record keeping and administration D. all of these options
-
Sheridan Company has 9000 units in finished goods. The sales budget show expected sales to be 29000 units. If the production budget shows that 33000 are required for production what was the desired...
-
Zane is examining two studies involving how different generations classify specified items as either luxuries or necessities. In the first study, the Echo generation is defined to be people ages...
-
Sniffer software is a. used by malicious Web sites to sniff data from cookies stored on the user's hard drive. b. used by network administrators to analyze network traffic. c. used by bus topology...
-
Miller Enterprises deposits the cash received during each day at the end of the day. Miller deposited $48,287 on October 3 and $50,116 on October 4. Cash register records and other documents...
-
Joint cost allocation-net realizable value method Nature's Garden Inc. produces wood chips, wood pulp, and mulch. These products are produced through harvesting trees and sending the logs through a...
-
Required information [The following information applies to the questions displayed below.] Demarco and Janine Jackson have been married for 20 years and have four children (no children under age 6 at...
-
Assurance services provided by the external auditor, other than the audit of financial statements, are far more useful than the latter. Discuss.
-
Describe the steps necessary to create a standard income statement.
-
(i) What accounting convention is generally used in the valuation of non-current assets? (ii) What additional costs may sometimes be included within non-current assets costs and to which assets may...
-
The management letter of representation is a key piece of audit evidence. Discuss.
-
We mention frequently in the text the term genuine, accurate and complete. Explain what the term means.
-
Design your own assignment in which you implement five acts of kindness (prosocial behavior) or an entire DAY of compassion and kindness. Use your discretion, common sense, and modesty at all times....
-
If a process has a six-sigma capability, what is the process capability index? a. 1 b. 2 c. 6 d. 12
-
Suppose that Sasha picks an integer X at random between 1 and 6 (inclusive). Then Ravi picks a different integer Y at random, from the 5 integers that remain. Assume that all (6) (5) = 30 choices are...
-
Chocolate chips are randomly distributed onto on a bakery's cookies with a rate, on average, of 11 chips per cookie. Assume that the cookies are independent. a. What is the probability that a...
-
Twenty percent of students will participate in an Honors course this semester. Students who have an Honors course on their schedule are known to have a 99% chance of fully enjoying their semester....
-
Use this website to review the outline of the Bank of Japans objectives. Summarize the mission of the Bank of Japan. How does this mission relate to intervening in the foreign exchange market?
-
As MADD executive director Chuck Hurley describes it, Before the 1980s, drunk driving was how people got home. It was normal behavior. In May of that year, Candy Lightner's 13-year-old daughter was...
-
In the early 1990s, most programs that were working to alleviate homelessness in American cities followed a similar model. Homeless men and women could visit shelters, but could not obtain permanent...

Study smarter with the SolutionInn App