Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Part of Seed Labs 2.0 for Seed Ubuntu 20.04 (Firewall Exploration) 4.4 Task 2.B: Protecting the Internal Network In this task, we will set up
Part of Seed Labs 2.0 for Seed Ubuntu 20.04 (Firewall Exploration)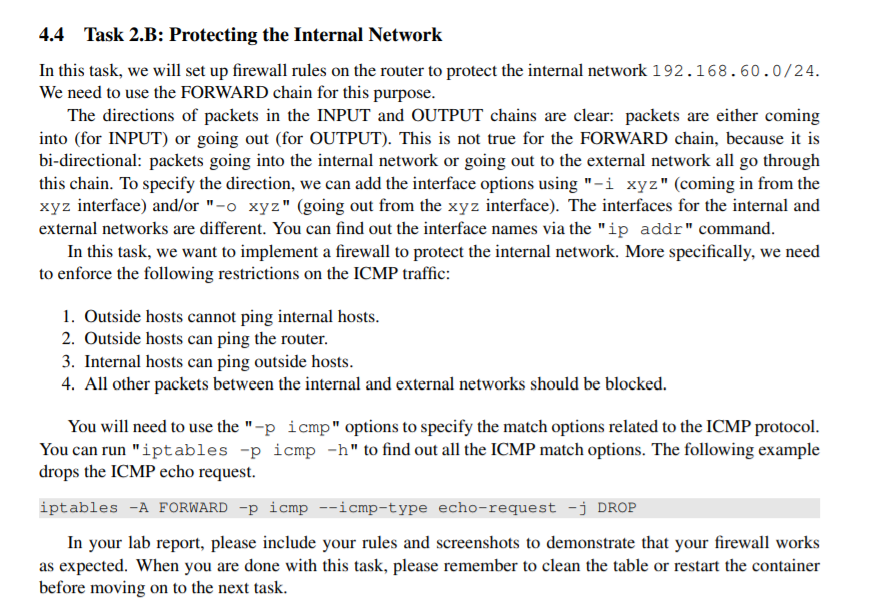
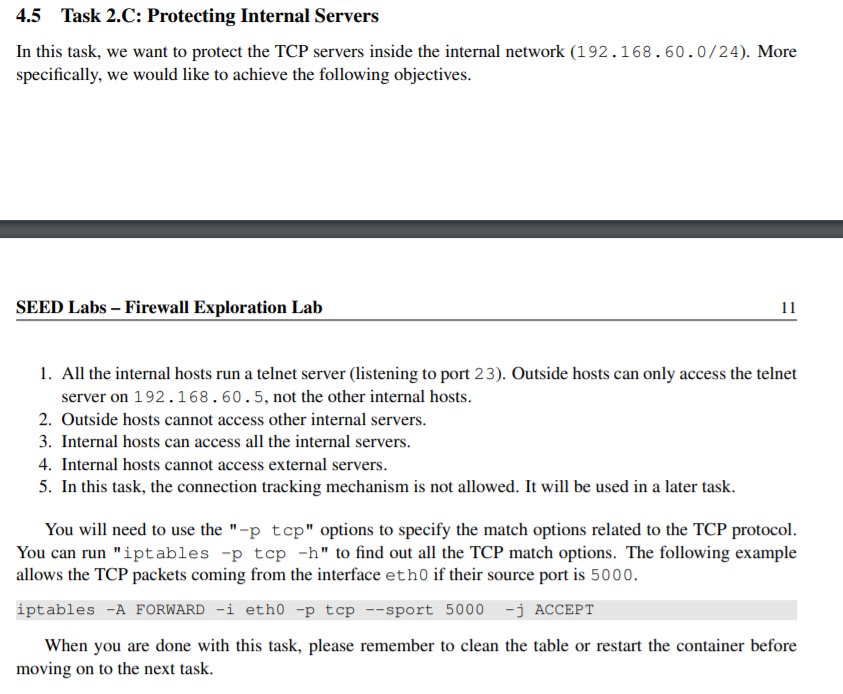
4.4 Task 2.B: Protecting the Internal Network In this task, we will set up firewall rules on the router to protect the internal network 192.168.60.0/24. We need to use the FORWARD chain for this purpose. The directions of packets in the INPUT and OUTPUT chains are clear: packets are either coming into (for INPUT) or going out (for OUTPUT). This is not true for the FORWARD chain, because it is bi-directional: packets going into the internal network or going out to the external network all go through this chain. To specify the direction, we can add the interface options using "-i xyz" (coming in from the xyz interface) and/or "-o xyz" (going out from the xyz interface). The interfaces for the internal and external networks are different. You can find out the interface names via the "ip addr" command. In this task, we want to implement a firewall to protect the internal network. More specifically, we need to enforce the following restrictions on the ICMP traffic: 1. Outside hosts cannot ping internal hosts. 2. Outside hosts can ping the router. 3. Internal hosts can ping outside hosts. 4. All other packets between the internal and external networks should be blocked. You will need to use the "-p icmp" options to specify the match options related to the ICMP protocol. You can run "iptables -p icmp -h" to find out all the ICMP match options. The following example drops the ICMP echo request. iptables -A FORWARD -p icmp --icmp-type echo-request -j DROP In your lab report, please include your rules and screenshots to demonstrate that your firewall works as expected. When you are done with this task, please remember to clean the table or restart the container before moving on to the next task. 4.5 Task 2.C: Protecting Internal Servers In this task, we want to protect the TCP servers inside the internal network (192.168.60.0/24). More specifically, we would like to achieve the following objectives. SEED Labs - Firewall Exploration Lab 11 1. All the internal hosts run a telnet server (listening to port 23). Outside hosts can only access the telnet server on 192.168.60.5, not the other internal hosts. 2. Outside hosts cannot access other internal servers. 3. Internal hosts can access all the internal servers. 4. Internal hosts cannot access external servers. 5. In this task, the connection tracking mechanism is not allowed. It will be used in a later task. You will need to use the "-p tcp" options to specify the match options related to the TCP protocol. You can run "iptables -p top -h" to find out all the TCP match options. The following example allows the TCP packets coming from the interface eth0 if their source port is 5000. iptables -A FORWARD -i etho -p top --sport 5000 -j ACCEPT When you are done with this task, please remember to clean the table or restart the container before moving on to the next task. 4.4 Task 2.B: Protecting the Internal Network In this task, we will set up firewall rules on the router to protect the internal network 192.168.60.0/24. We need to use the FORWARD chain for this purpose. The directions of packets in the INPUT and OUTPUT chains are clear: packets are either coming into (for INPUT) or going out (for OUTPUT). This is not true for the FORWARD chain, because it is bi-directional: packets going into the internal network or going out to the external network all go through this chain. To specify the direction, we can add the interface options using "-i xyz" (coming in from the xyz interface) and/or "-o xyz" (going out from the xyz interface). The interfaces for the internal and external networks are different. You can find out the interface names via the "ip addr" command. In this task, we want to implement a firewall to protect the internal network. More specifically, we need to enforce the following restrictions on the ICMP traffic: 1. Outside hosts cannot ping internal hosts. 2. Outside hosts can ping the router. 3. Internal hosts can ping outside hosts. 4. All other packets between the internal and external networks should be blocked. You will need to use the "-p icmp" options to specify the match options related to the ICMP protocol. You can run "iptables -p icmp -h" to find out all the ICMP match options. The following example drops the ICMP echo request. iptables -A FORWARD -p icmp --icmp-type echo-request -j DROP In your lab report, please include your rules and screenshots to demonstrate that your firewall works as expected. When you are done with this task, please remember to clean the table or restart the container before moving on to the next task. 4.5 Task 2.C: Protecting Internal Servers In this task, we want to protect the TCP servers inside the internal network (192.168.60.0/24). More specifically, we would like to achieve the following objectives. SEED Labs - Firewall Exploration Lab 11 1. All the internal hosts run a telnet server (listening to port 23). Outside hosts can only access the telnet server on 192.168.60.5, not the other internal hosts. 2. Outside hosts cannot access other internal servers. 3. Internal hosts can access all the internal servers. 4. Internal hosts cannot access external servers. 5. In this task, the connection tracking mechanism is not allowed. It will be used in a later task. You will need to use the "-p tcp" options to specify the match options related to the TCP protocol. You can run "iptables -p top -h" to find out all the TCP match options. The following example allows the TCP packets coming from the interface eth0 if their source port is 5000. iptables -A FORWARD -i etho -p top --sport 5000 -j ACCEPT When you are done with this task, please remember to clean the table or restart the container before moving on to the next task
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


