Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Please answer! Asymmetrical encryption uses one key to encrypt and another key to decrypt. The most common algorithm used in applications is the RSA algorithm.
Please answer!
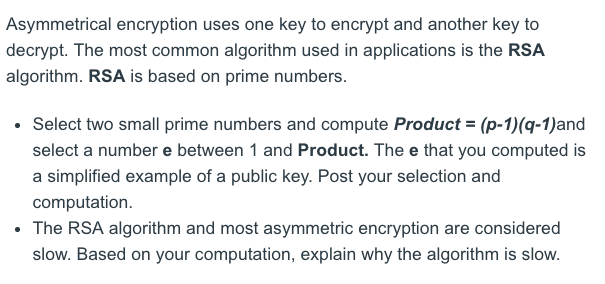
Asymmetrical encryption uses one key to encrypt and another key to decrypt. The most common algorithm used in applications is the RSA algorithm. RSA is based on prime numbers. . Select two small prime numbers and compute Product- (p-1)(q-1)and select a number e between 1 and Product. The e that you computed is a simplified example of a public key. Post your selection and computation . The RSA algorithm and most asymmetric encryption are considered n, explain why the algorithm is slowStep by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


