Please solve part 2) 3) thanks!
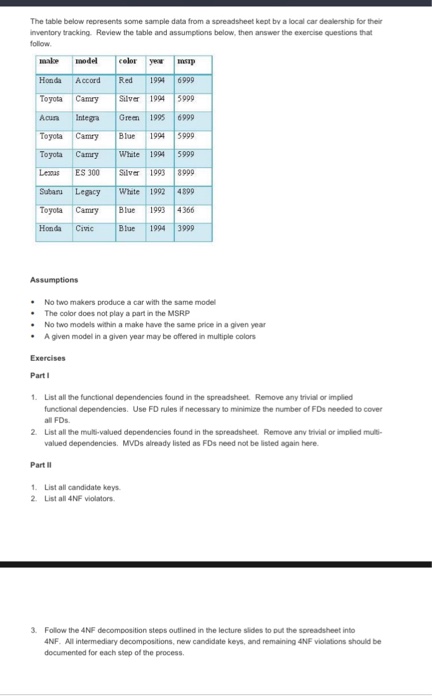
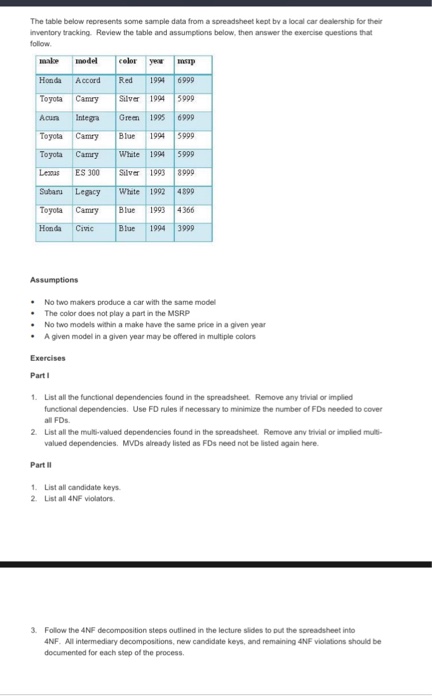
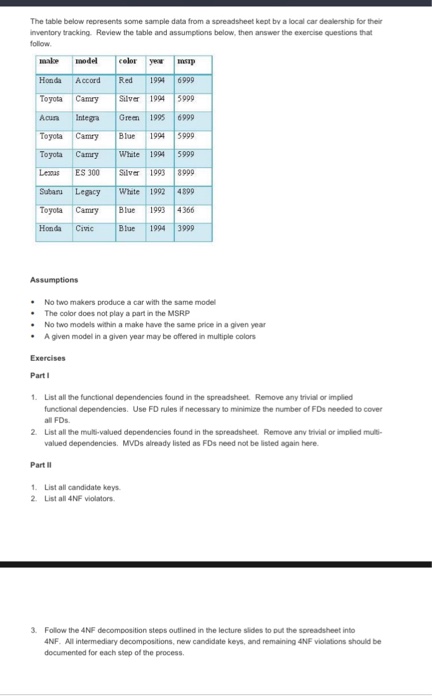
The table below represents some sample data from a spreadsheet kept by a local car dealership for their inventory tracking. Review the table and assumptions below, then answer the exercise questions that follow. No two makers produce a car with the same model The color does not play a part in the MSRP No two models within a make have the same price in a given year A given model in a given year may be offered in multiple colors 1. List all the functional dependencies found in the spreadsheet. Remove any trivial or implied functional dependencies. Use FD rules if necessary to minimize the number of FDs needed to cover all FDs. List all the multi-valued dependencies found in the spreadsheet. Remove any trivial or implied multivalued dependencies. MVDs already listed as FDs need not be listed again here. 1. List all candidate keys. Listall 4NF violators. Follow the ANF decomposition steps outlined in the lecture sides to put the spreadsheet into 4NF. All intermediary decompositions, new candidate keys, and remaining 4NF violations should be for each step of the process. The table below represents some sample data from a spreadsheet kept by a local car dealership for their inventory tracking. Review the table and assumptions below, then answer the exercise questions that follow. No two makers produce a car with the same model The color does not play a part in the MSRP No two models within a make have the same price in a given year A given model in a given year may be offered in multiple colors 1. List all the functional dependencies found in the spreadsheet. Remove any trivial or implied functional dependencies. Use FD rules if necessary to minimize the number of FDs needed to cover all FDs. List all the multi-valued dependencies found in the spreadsheet. Remove any trivial or implied multivalued dependencies. MVDs already listed as FDs need not be listed again here. 1. List all candidate keys. Listall 4NF violators. Follow the ANF decomposition steps outlined in the lecture sides to put the spreadsheet into 4NF. All intermediary decompositions, new candidate keys, and remaining 4NF violations should be for each step of the process