Answered step by step
Verified Expert Solution
Question
1 Approved Answer
4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information
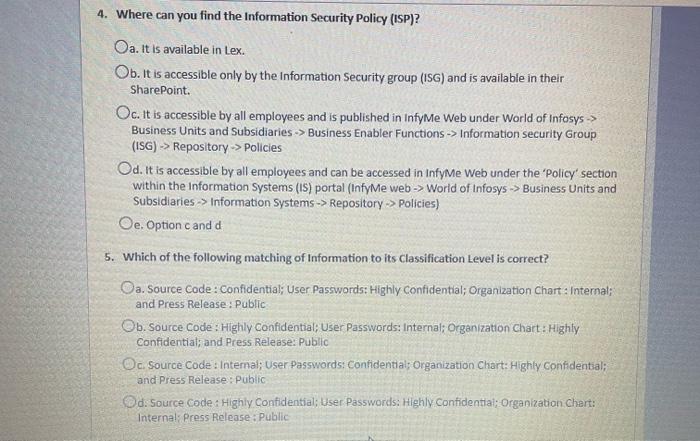
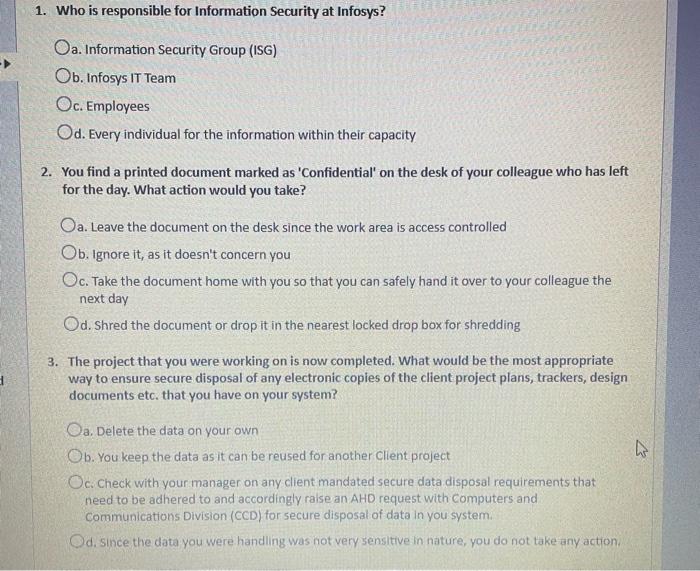
4. Where can you find the Information Security Policy (ISP)? Oa. It is available in Lex. Ob. It is accessible only by the Information Security group (ISG) and is available in their SharePoint. Oc. It is accessible by all employees and is published in InfyMe Web under World of Infosys > Business Units and Subsidiaries > Business Enabler Functions -> Information security Group (ISG) -> Repository-> Policies Od. It is accessible by all employees and can be accessed in InfyMe Web under the 'Policy' section within the Information Systems (IS) portal (InfyMe web-> World of Infosys > Business Units and Subsidiaries > Information Systems -> Repository-> Policies) Oe. Option c and d 5. Which of the following matching of Information to its Classification Level is correct? Oa. Source Code : Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; and Press Release: Public Ob. Source Code: Highly Confidential; User Passwords: Internal; Organization Chart: Highly Confidential; and Press Release: Public Oc. Source Code: Internal; User Passwords: Confidential; Organization Chart: Highly Confidential; and Press Release: Public Od: Source Code: Highly Confidential; User Passwords: Highly Confidential; Organization Chart: Internal; Press Release: Public 1. Who is responsible for Information Security at Infosys? Oa. Information Security Group (ISG) Ob. Infosys IT Team Oc. Employees Od. Every individual for the information within their capacity 2. You find a printed document marked as 'Confidential' on the desk of your colleague who has left for the day. What action would you take? Oa. Leave the document on the desk since the work area is access controlled Ob. Ignore it, as it doesn't concern you Oc. Take the document home with you so that you can safely hand it over to your colleague the next day Od. Shred the document or drop it in the nearest locked drop box for shredding 3. The project that you were working on is now completed. What would be the most appropriate way to ensure secure disposal of any electronic copies of the client project plans, trackers, design documents etc. that you have on your system? Oa. Delete the data on your own Ob. You keep the data as it can be reused for another Client project Oc. Check with your manager on any client mandated secure data disposal requirements that need to be adhered to and accordingly raise an AHD request with Computers and Communications Division (CCD) for secure disposal of data in you system. Od. Since the data you were handling was not very sensitive in nature, you do not take any action, 4
Step by Step Solution
★★★★★
3.63 Rating (160 Votes )
There are 3 Steps involved in it
Step: 1
Question Answer 1 The Information Security group ISC Reason The Information Security group ISG is th...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


