Question
Programming in C, you will implement Vigenere encryption and decryption with Cipher Block Chaining (CBC). The inputs to the encryption algorithm include Vigenere key,
Programming in C, you will implement Vigenere encryption and decryption with Cipher Block Chaining (CBC). \
The inputs to the encryption algorithm include Vigenere key, initial vector (IV) and plaintext and the inputs to the decryption algorithm include Vigenere key, IV and cyphertext
The encipher program will be run first. When encrypting, the encipher program will take inputs including plaintext, key and IV. The encipher encrypts the plaintext with the key & IV, and generate a file to store the ciphertext. Then when the decipher program is run, the ciphertext file will be used as input along with key & IV. The decipher program decrypts the ciphertext to recover the plaintext.
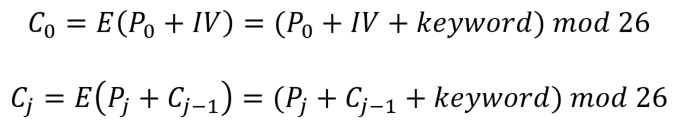
the encryption of Vigenere with CBC can be expressed as:
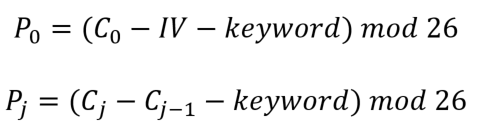
decryption of Vigenere with CBC as:
The plaintext input to the Vigenere CBC encipher should come from a text file. You may use any text file that is less than 4 Kilobytes in size.
You can generate your text file by simply copying and pasting any text content. However, the normal text file contains upper case and lower case alphabetic characters, numbers, punctuations and other special characters including space and line feed etc.. These are way more than 26 letters defined in Vigenere cipher. So you have to preprocess the text file to eliminate all the special characters, numbers, white space and punctuations, as well as convert all upper case letters into lower case letters. The result of preprocessing should be a string of lower case letters.
For this assignment, you would allow the user to enter a key (key length ranges from 2 to 10) and an IV with the same length as key. You may want to mandate that the length of IV should be the same as the key. Inputs to the Vigenere CBC decipher should be the same key and IV, as well as the ciphertext. The ciphertext sequence should be generated by the Vigenere CBC encipher.
The outputs of the encipher program should include the following:
Original text file name
Key
IV
Block size
Plaintext (after preprocessing) printed on the screen
Number of characters in plaintext (before padding)
Ciphertext printed on the screen
Name of ciphertext file (ciphertext saved to a file)
Number of padding characters
The ciphertext file will be used as one of the inputs to the decipher. The outputs of the decipher program should include the following:
Ciphertext file name
Number of characters in ciphertext
Recovered plaintext printed on the screen
Co = E (Po + IV) = (Po + IV + keyword) mod 26 Gj = E (P, + Cj-1)-(P, + Cj-1-keyword) mod 26 Co = E (Po + IV) = (Po + IV + keyword) mod 26 Gj = E (P, + Cj-1)-(P, + Cj-1-keyword) mod 26Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started