Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Question 1 Write down correct answer for the corresponding statements provided. Column A (Marks: 10) Q.1.1 Shows users how to complete a task that
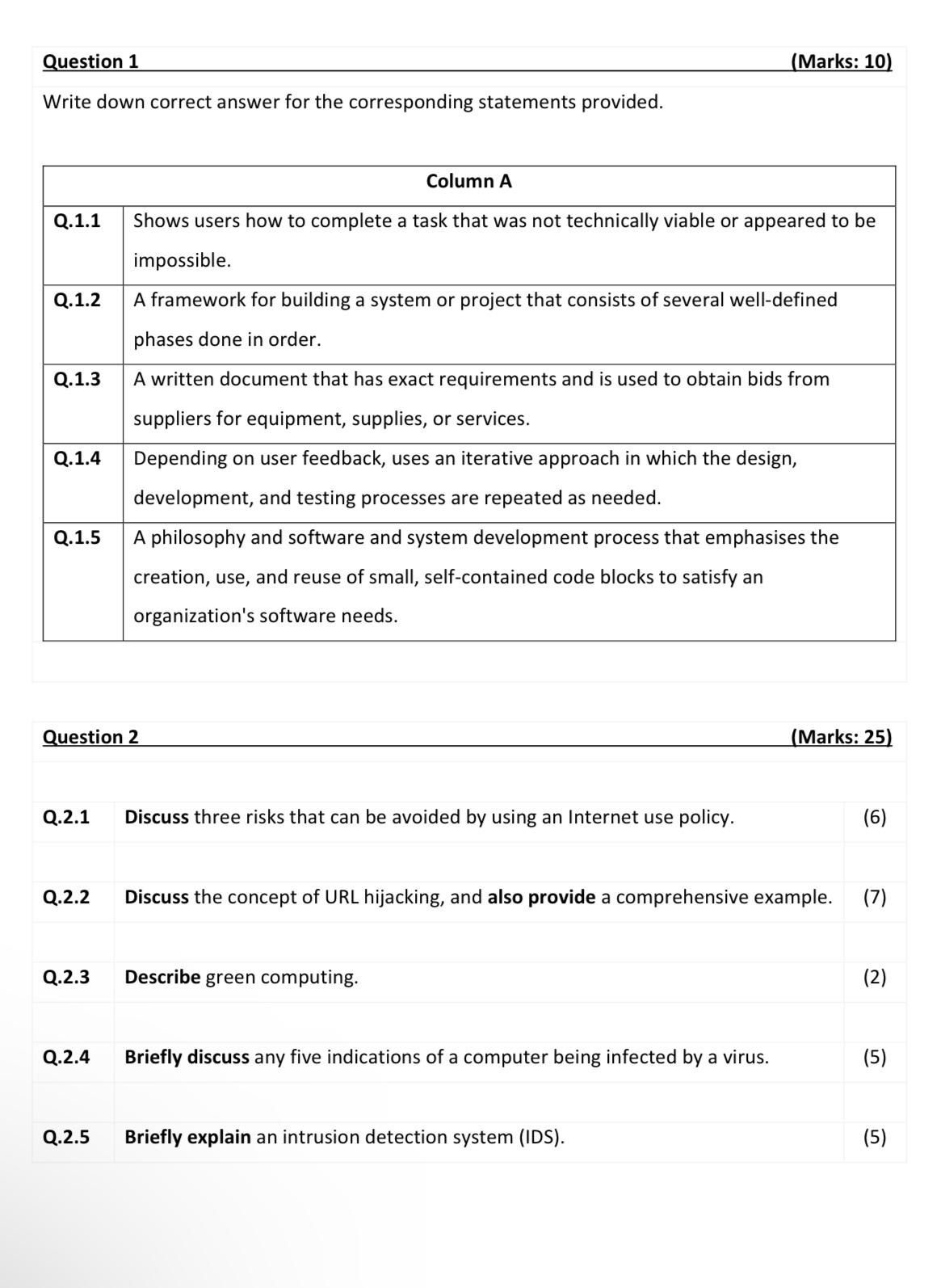
Question 1 Write down correct answer for the corresponding statements provided. Column A (Marks: 10) Q.1.1 Shows users how to complete a task that was not technically viable or appeared to be Q.1.2 Q.1.3 Q.1.4 impossible. A framework for building a system or project that consists of several well-defined phases done in order. A written document that has exact requirements and is used to obtain bids from suppliers for equipment, supplies, or services. Depending on user feedback, uses an iterative approach in which the design, development, and testing processes are repeated as needed. Q.1.5 A philosophy and software and system development process that emphasises the creation, use, and reuse of small, self-contained code blocks to satisfy an organization's software needs. Question 2 Q.2.1 Discuss three risks that can be avoided by using an Internet use policy. (Marks: 25) (6) Q.2.2 Discuss the concept of URL hijacking, and also provide a comprehensive example. (7) Q.2.3 Describe green computing. (2) Q.2.4 Briefly discuss any five indications of a computer being infected by a virus. (5) Q.2.5 Briefly explain an intrusion detection system (IDS). (5)
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


