Answered step by step
Verified Expert Solution
Question
1 Approved Answer
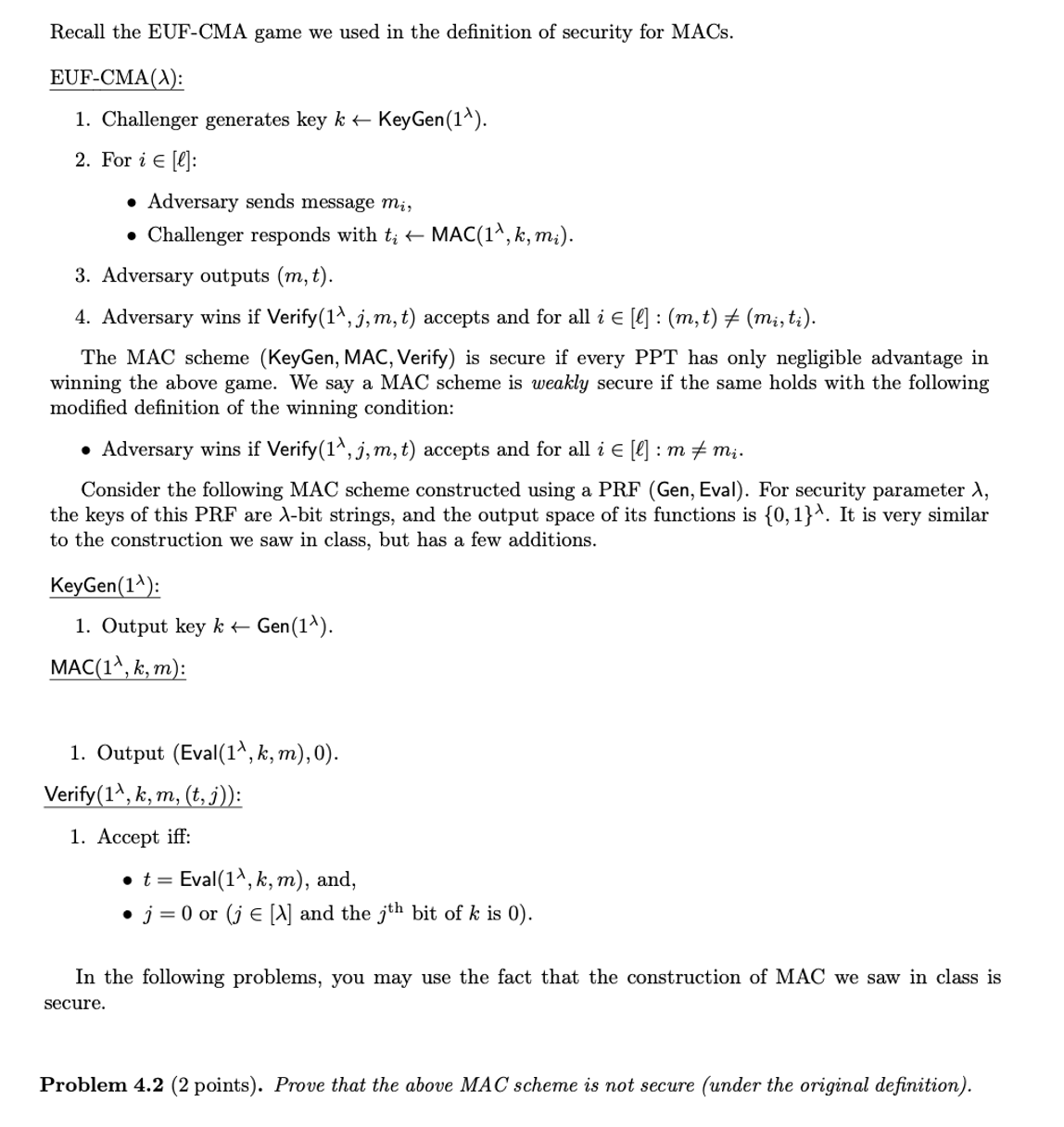
Recall the EUF - CMA game we used in the definition of security for MACs. EUF - CMA ( ) : Challenger generates key klarrKeyGen
Recall the EUFCMA game we used in the definition of security for MACs.
EUFCMA :
Challenger generates key klarrKeyGen
For iin :
Adversary sends message
Challenger responds with larrMAC
Adversary outputs
Adversary wins if Verify accepts and for all iin:
The MAC scheme KeyGen MAC, Verify is secure if every PPT has only negligible advantage in
winning the above game. We say a MAC scheme is weakly secure if the same holds with the following
modified definition of the winning condition:
Adversary wins if Verify accepts and for all iin:
Consider the following MAC scheme constructed using a PRF Gen Eval For security parameter
the keys of this PRF are bit strings, and the output space of its functions is It is very similar
to the construction we saw in class, but has a few additions.
KeyGen :
Output key klarrGen
MAC:
Output Eval :
Verify :
Accept iff:
Eval and,
or and the bit of is
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


