Answered step by step
Verified Expert Solution
Question
1 Approved Answer
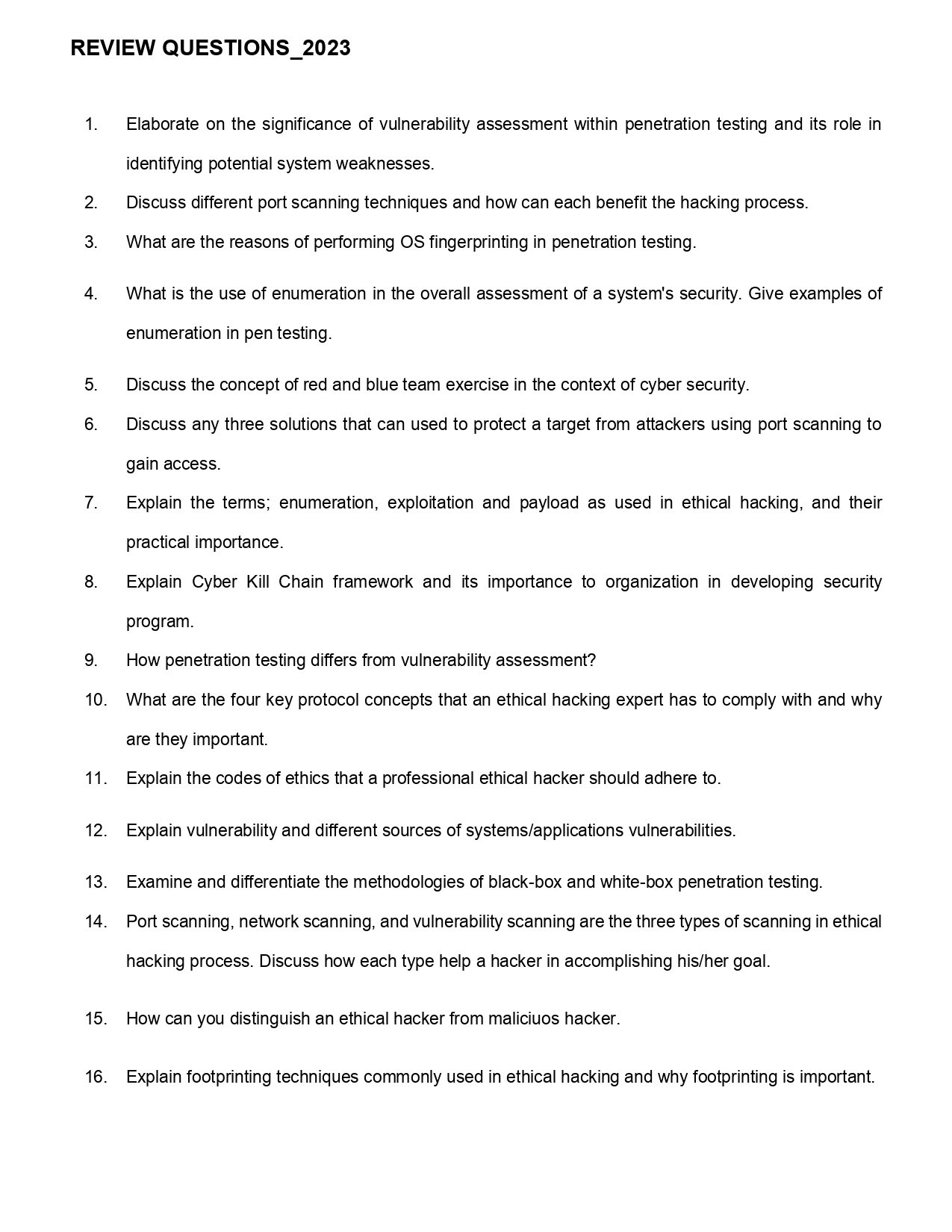
REVIEW QUESTIONS _ 2 0 2 3 Elaborate on the significance of vulnerability assessment within penetration testing and its role in identifying potential system weaknesses.
REVIEW QUESTIONS
Elaborate on the significance of vulnerability assessment within penetration testing and its role in
identifying potential system weaknesses.
Discuss different port scanning techniques and how can each benefit the hacking process.
What are the reasons of performing OS fingerprinting in penetration testing.
What is the use of enumeration in the overall assessment of a system's security. Give examples of
enumeration in pen testing.
Discuss the concept of red and blue team exercise in the context of cyber security.
Discuss any three solutions that can used to protect a target from attackers using port scanning to
gain access.
Explain the terms; enumeration, exploitation and payload as used in ethical hacking, and their
practical importance.
Explain Cyber Kill Chain framework and its importance to organization in developing security
program.
How penetration testing differs from vulnerability assessment?
What are the four key protocol concepts that an ethical hacking expert has to comply with and why
are they important.
Explain the codes of ethics that a professional ethical hacker should adhere to
Explain vulnerability and different sources of systemsapplications vulnerabilities.
Examine and differentiate the methodologies of blackbox and whitebox penetration testing.
Port scanning, network scanning, and vulnerability scanning are the three types of scanning in ethical
hacking process. Discuss how each type help a hacker in accomplishing hisher goal.
How can you distinguish an ethical hacker from maliciuos hacker.
Explain footprinting techniques commonly used in ethical hacking and why footprinting is important.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


