Answered step by step
Verified Expert Solution
Question
1 Approved Answer
SECTION B [70 Marks) Question 1 Identify the most suitable location for switches and routers in the Kingsoft premises.( Marks) Question 2 Draw the network
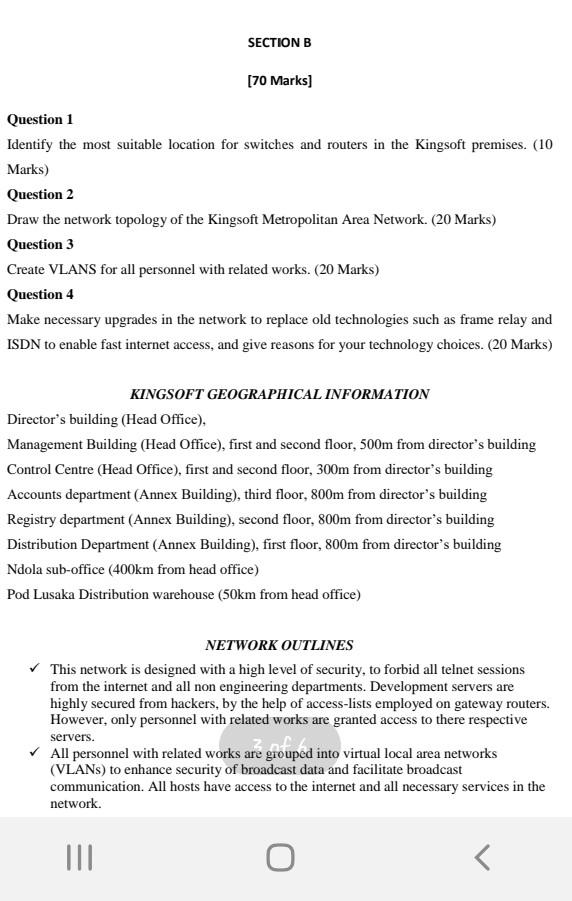
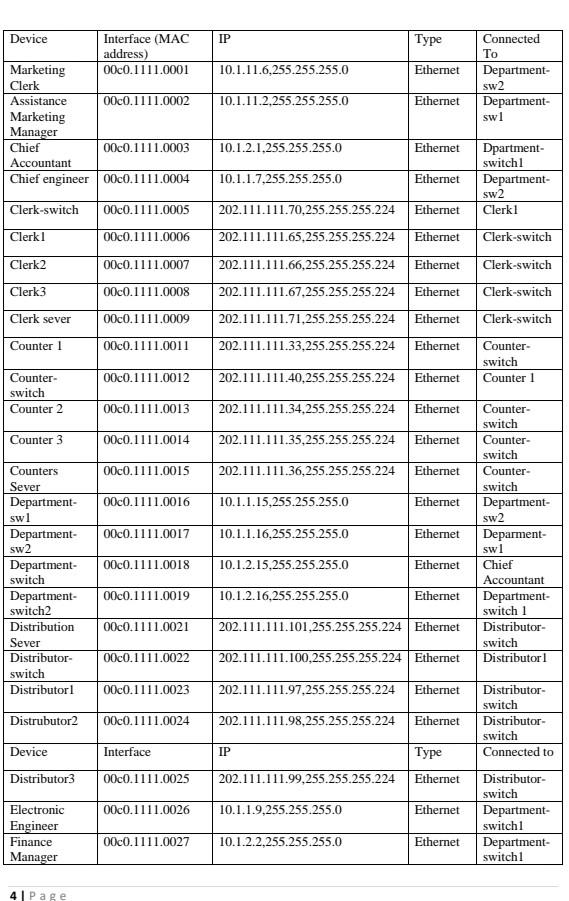
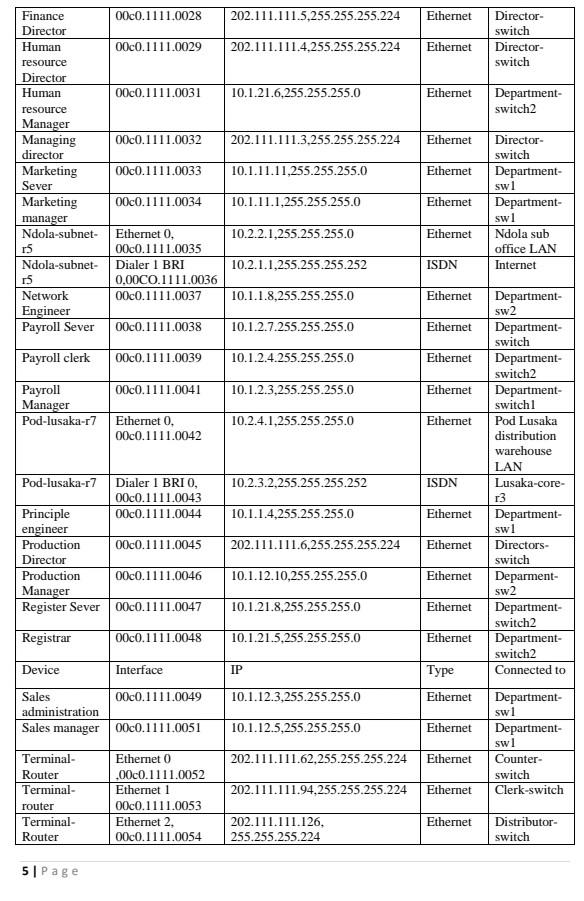
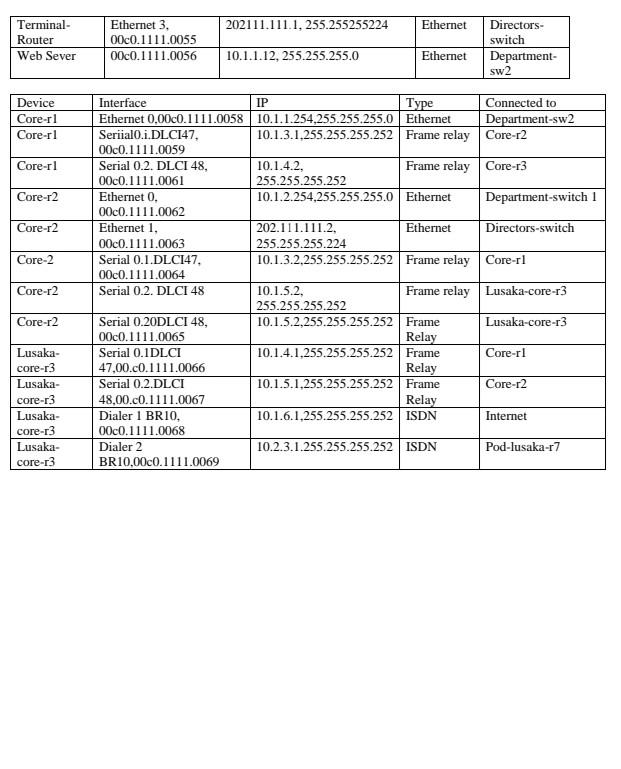
SECTION B [70 Marks) Question 1 Identify the most suitable location for switches and routers in the Kingsoft premises.( Marks) Question 2 Draw the network topology of the Kingsoft Metropolitan Area Network. (20 Marks) Question 3 Create VLANS for all personnel with related works. (20 Marks) Question 4 Make necessary upgrades in the network to replace old technologies such as frame relay at ISDN to enable fast internet access, and give reasons for your technology choices. (20 Mark SECTION B [70 Marks] Question 1 Identify the most suitable location for switches and routers in the Kingsoft premises. (10 Marks) Question 2 Draw the network topology of the Kingsoft Metropolitan Area Network. (20 Marks) Question 3 Create VLANS for all personnel with related works. (20 Marks) Question 4 Make necessary upgrades in the network to replace old technologies such as frame relay and ISDN to enable fast internet access, and give reasons for your technology choices. (20 Marks) KINGSOFT GEOGRAPHICAL INFORMATION Director's building (Head Office), Management Building (Head Office), first and second floor, 500m from director's building Control Centre (Head Office), first and second floor, 300m from director's building Accounts department (Annex Building), third floor, 800m from director's building Registry department (Annex Building), second floor, 800m from director's building Distribution Department (Annex Building), first floor, 800m from director's building Ndola sub-office (400km from head office) Pod Lusaka Distribution warehouse (50km from head office) NETWORK OUTLINES This network is designed with a high level of security, to forbid all telnet sessions from the internet and all non engineering departments. Development servers are highly secured from hackers, by the help of access-lists employed on gateway routers. However, only personnel with related works are granted access to there respective servers. All personnel with related works are grouped into virtual local area networks (VLANs) to enhance security of broadcast data and facilitate broadcast communication. All hosts have access to the internet and all necessary services in the network. III o
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


