Question: Security network administrators can create their own ACL rules for firewall based on which of the following attributes. I. II. III. IV. A. B.
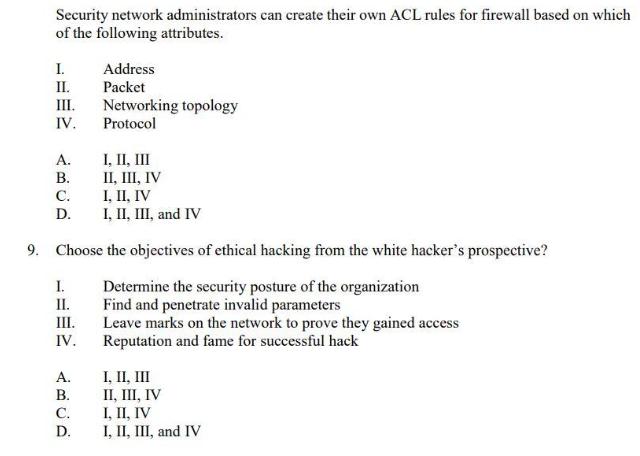
Security network administrators can create their own ACL rules for firewall based on which of the following attributes. I. II. III. IV. A. B. C. D. I. II. III. IV. Address Packet 9. Choose the objectives of ethical hacking from the white hacker's prospective? Determine the security posture of the organization Find and penetrate invalid parameters Leave marks on the network to prove they gained access Reputation and fame for successful hack A. B. C. D. Networking topology Protocol I, II, III II, III, IV I, II, IV I, II, III, and IV I, II, III II, III, IV I, II, IV I, II, III, and IV
Step by Step Solution
3.43 Rating (159 Votes )
There are 3 Steps involved in it
The detailed answer for the above question is provided below Answer For the fi... View full answer

Get step-by-step solutions from verified subject matter experts


