Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Subanit handwritten work in the class. Modern Security Applications Sender Hash(-) Network Hash() Receiver Compare Figure 1: General message authentication code (MAC) system 3. Consider
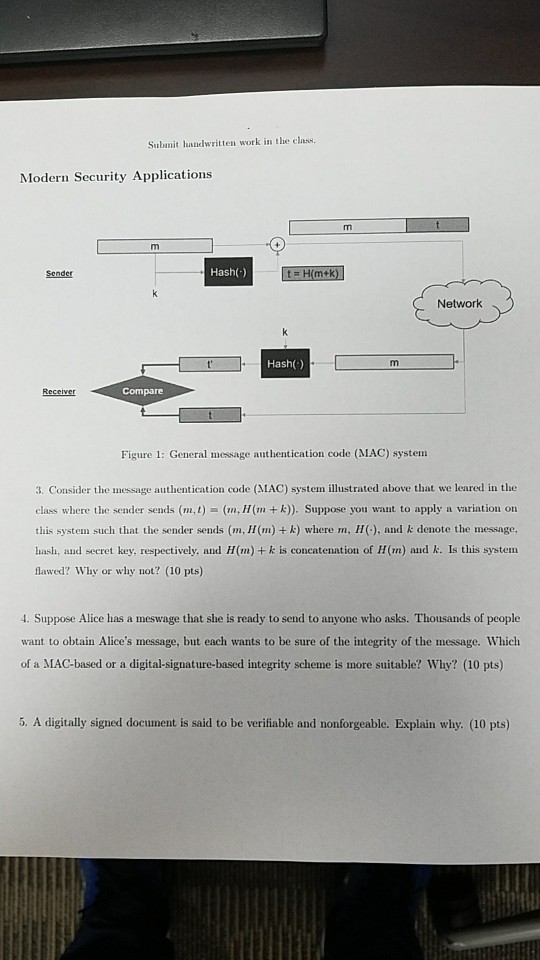
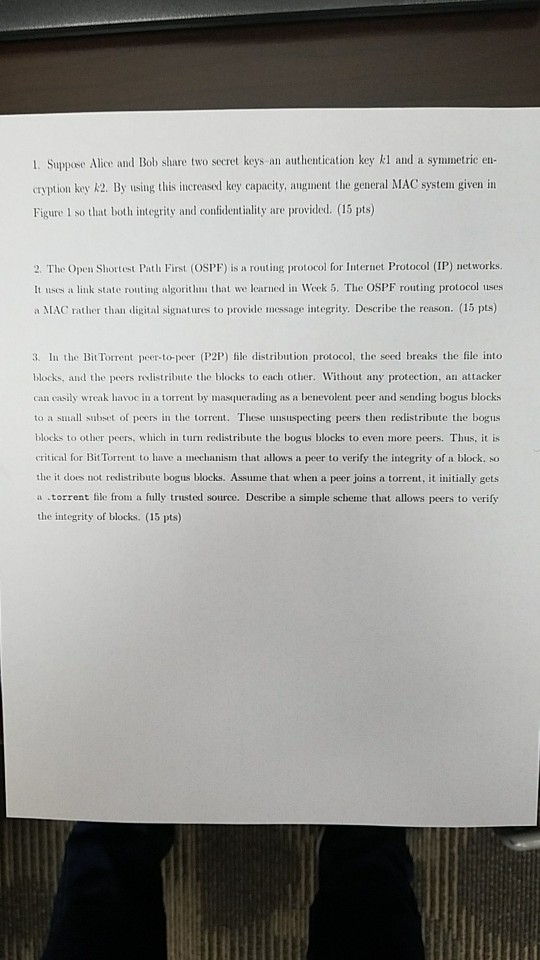
Subanit handwritten work in the class. Modern Security Applications Sender Hash(-) Network Hash() Receiver Compare Figure 1: General message authentication code (MAC) system 3. Consider the message authentication code (MAC) system illustrated above that we leared in the class where the sender sends (m,t)(m, H(mk)). Suppose you want to apply a variation on this system such that the sender sends (m, H(m) + k) where m, H. and k denote the message, hash, aud secret key, respectively, and H(m) + k is concatenation of H(m) aud k. Is this system flawed? Why or why not? (10 pts) . Suppose Alice has a meswage that she is ready to send to anyone who asks. Thousands of people want to obtain Alice's message, but each wants to be sure of the integrity of the message. Which of a MAC-based or a digital-signature-based integrity scheme is more suitable? Why? (10 pts) 5. A digitally signed document is said to be verifiable and nonforgeable. Explain why. (10 pts) Subanit handwritten work in the class. Modern Security Applications Sender Hash(-) Network Hash() Receiver Compare Figure 1: General message authentication code (MAC) system 3. Consider the message authentication code (MAC) system illustrated above that we leared in the class where the sender sends (m,t)(m, H(mk)). Suppose you want to apply a variation on this system such that the sender sends (m, H(m) + k) where m, H. and k denote the message, hash, aud secret key, respectively, and H(m) + k is concatenation of H(m) aud k. Is this system flawed? Why or why not? (10 pts) . Suppose Alice has a meswage that she is ready to send to anyone who asks. Thousands of people want to obtain Alice's message, but each wants to be sure of the integrity of the message. Which of a MAC-based or a digital-signature-based integrity scheme is more suitable? Why? (10 pts) 5. A digitally signed document is said to be verifiable and nonforgeable. Explain why. (10 pts)
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started