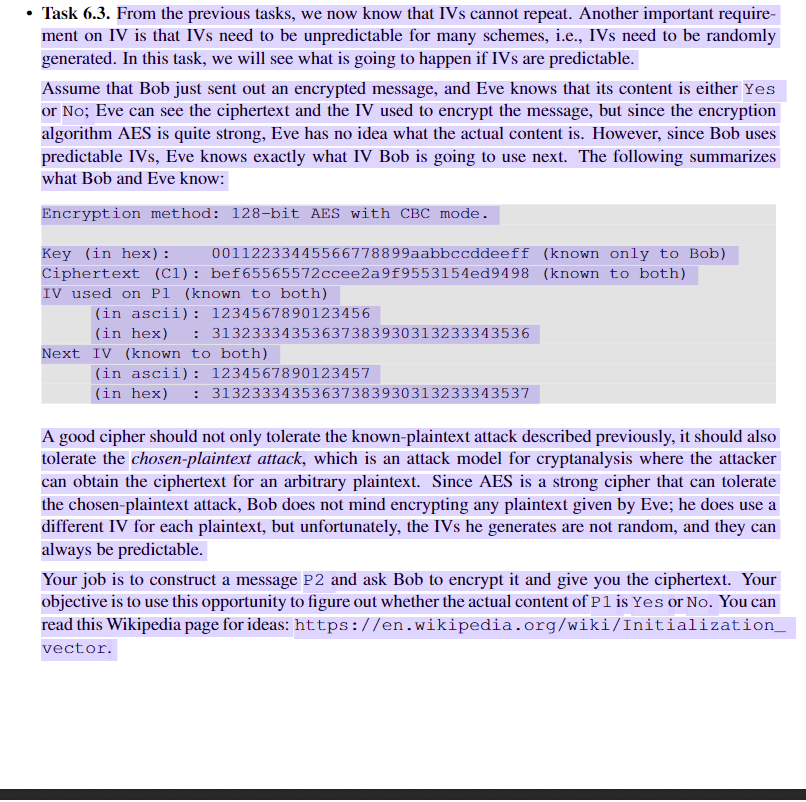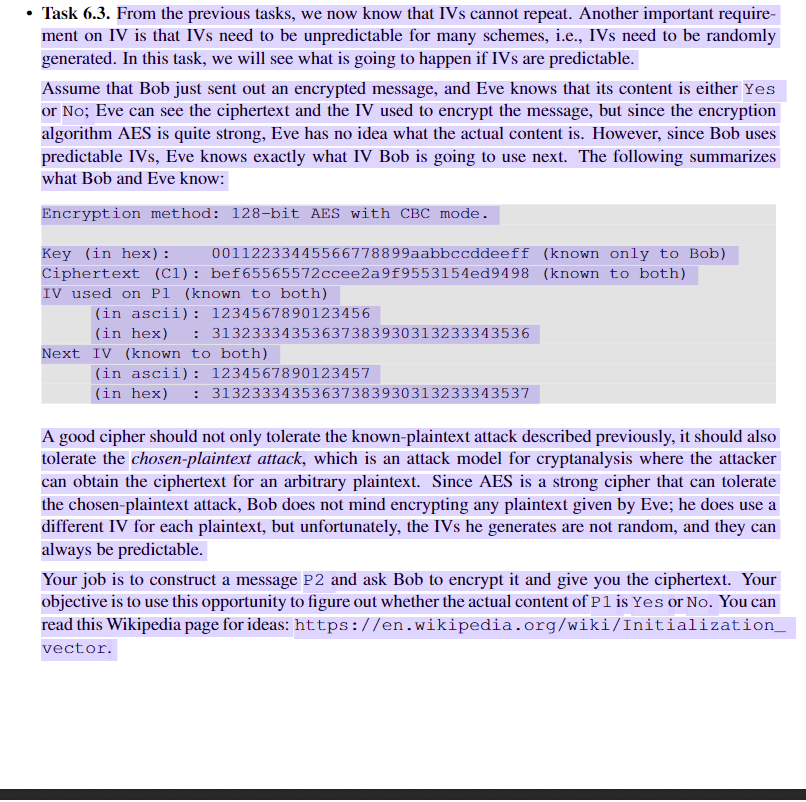
Task 6.3. From the previous tasks, we now know that IVs cannot repeat. Another important require ment on IV is that IVs need to be unpredictable for many schemes, i.e., IVs need to be randomly generated. In this task, we will see what is going to happen if IVs are predictable Assume that Bob just sent out an encrypted message, and Eve knows that its content is either Yes or No; Eve can see the ciphertext and the IV used to encrypt the message, but since the encryption algorithm AES is quite strong, Eve has no idea what the actual content is. However, since Bob uses predictable IVs, Eve knows exactly what IV Bob is going to use next. The following summarizes what Bob and Eve know Encryption method: 128-bit AES with CBC mode Key (in hex): Ciphertext (Cl):bef65565572ccee2a9f9553154ed9498 (known to both) IV used on P1 (known to both) 00112233445566778899aabbccddeeff (known only to Bob) (in ascii): 1234567890123456 (in hex)31323334353637383930313233343536 Next IV (known to both) (in ascii): 1234567890123457 in hex)31323334353637383930313233343537 A good cipher should not only tolerate the known-plaintext attack described previously, it should also tolerate the chosen-plaintext attack, which is an attack model for cryptanalysis where the attacker can obtain the ciphertext for an arbitrary plaintext. Since AES is a strong cipher that can tolerate the chosen-plaintext attack, Bob does not mind encrypting any plaintext given by Eve; he does use a different IV for each plaintext, but unfortunately, the IVs he generates are not random, and they can always be predictable Your job is to construct a message P2 and ask Bob to encrypt it and give you the ciphertext. Your objective is to use this opportunity to figure out whether the actual content of P 1 is Yes or No. You can read this Wikipedia page for ideas: https://en.wikipedia.org/wiki/Initializatiorn vector. Task 6.3. From the previous tasks, we now know that IVs cannot repeat. Another important require ment on IV is that IVs need to be unpredictable for many schemes, i.e., IVs need to be randomly generated. In this task, we will see what is going to happen if IVs are predictable Assume that Bob just sent out an encrypted message, and Eve knows that its content is either Yes or No; Eve can see the ciphertext and the IV used to encrypt the message, but since the encryption algorithm AES is quite strong, Eve has no idea what the actual content is. However, since Bob uses predictable IVs, Eve knows exactly what IV Bob is going to use next. The following summarizes what Bob and Eve know Encryption method: 128-bit AES with CBC mode Key (in hex): Ciphertext (Cl):bef65565572ccee2a9f9553154ed9498 (known to both) IV used on P1 (known to both) 00112233445566778899aabbccddeeff (known only to Bob) (in ascii): 1234567890123456 (in hex)31323334353637383930313233343536 Next IV (known to both) (in ascii): 1234567890123457 in hex)31323334353637383930313233343537 A good cipher should not only tolerate the known-plaintext attack described previously, it should also tolerate the chosen-plaintext attack, which is an attack model for cryptanalysis where the attacker can obtain the ciphertext for an arbitrary plaintext. Since AES is a strong cipher that can tolerate the chosen-plaintext attack, Bob does not mind encrypting any plaintext given by Eve; he does use a different IV for each plaintext, but unfortunately, the IVs he generates are not random, and they can always be predictable Your job is to construct a message P2 and ask Bob to encrypt it and give you the ciphertext. Your objective is to use this opportunity to figure out whether the actual content of P 1 is Yes or No. You can read this Wikipedia page for ideas: https://en.wikipedia.org/wiki/Initializatiorn vector