Answered step by step
Verified Expert Solution
Question
1 Approved Answer
The Discover packet has a source port of 68 and destination port of 67 The Offer packet has a source port of 67 and a
The Discover packet has a source port of 68 and destination port of 67
The Offer packet has a source port of 67 and a destination port of 68
The Request packet has a source port of 68 and a destination of 67
The ACK packet has a source port of 67 and a destination of 68
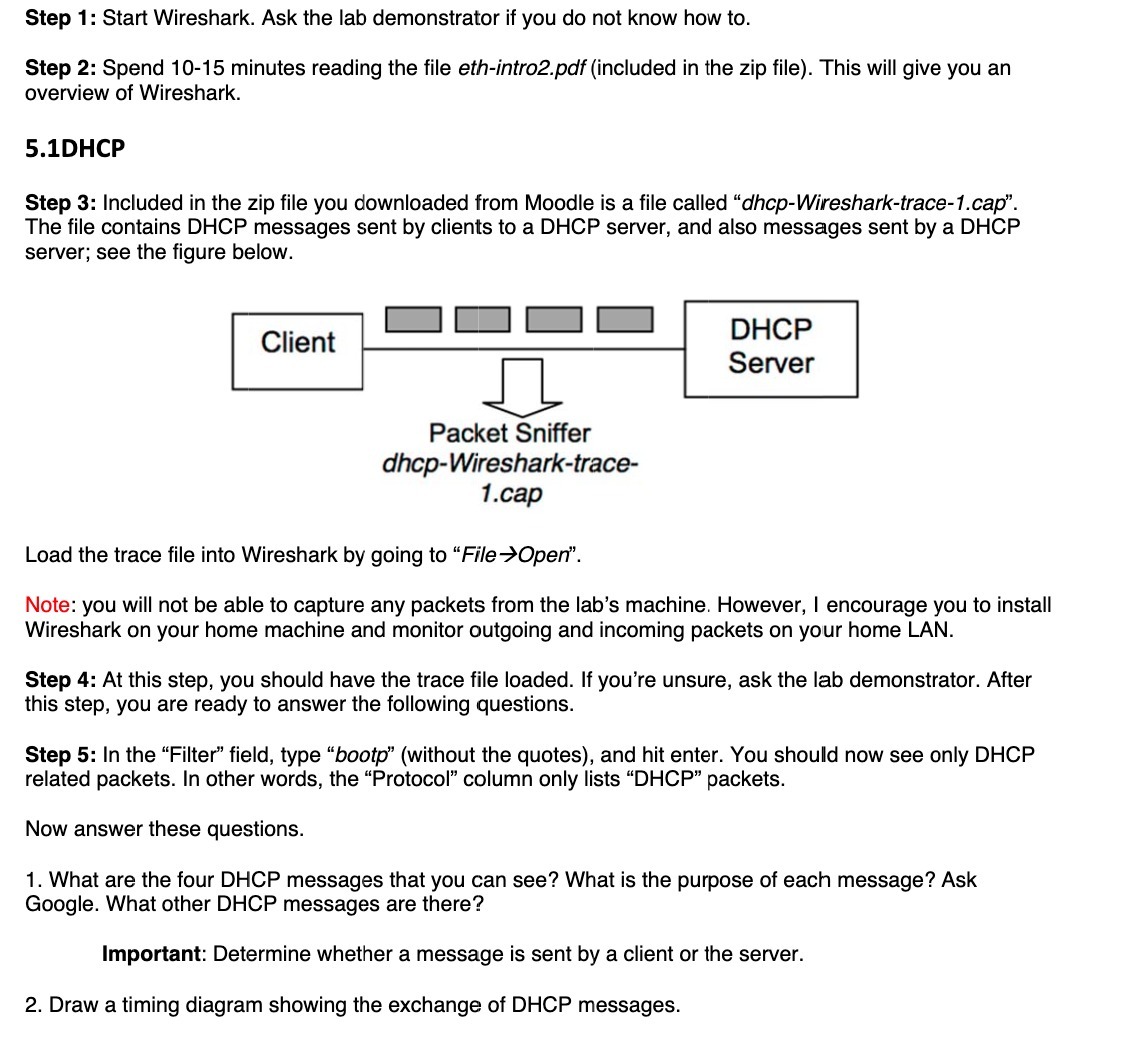
Step 1: Start Wireshark. Ask the lab demonstrator if you do not know how to. Step 2: Spend 10-15 minutes reading the file eth-intro2.pdf (included in the zip file). This will give you an overview of Wireshark. 5.1DHCP Step 3: Included in the zip file you downloaded from Moodle is a file called "dhcp-Wireshark-trace-1.cap". The file contains DHCP messages sent by clients to a DHCP server, and also messages sent by a DHCP server; see the figure below. Client Packet Sniffer dhcp-Wireshark-trace- 1.cap DHCP Server Load the trace file into Wireshark by going to "FileOpen". Note: you will not be able to capture any packets from the lab's machine. However, I encourage you to install Wireshark on your home machine and monitor outgoing and incoming packets on your home LAN. Step 4: At this step, you should have the trace file loaded. If you're unsure, ask the lab demonstrator. After this step, you are ready to answer the following questions. Step 5: In the "Filter" field, type "bootp" (without the quotes), and hit enter. You should now see only DHCP related packets. In other words, the "Protocol" column only lists "DHCP" packets. Now answer these questions. 1. What are the four DHCP messages that you can see? What is the purpose of each message? Ask Google. What other DHCP messages are there? Important: Determine whether a message is sent by a client or the server. 2. Draw a timing diagram showing the exchange of DHCP messages.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


