The following table shows a list of access matrix that defines the access rights of users...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
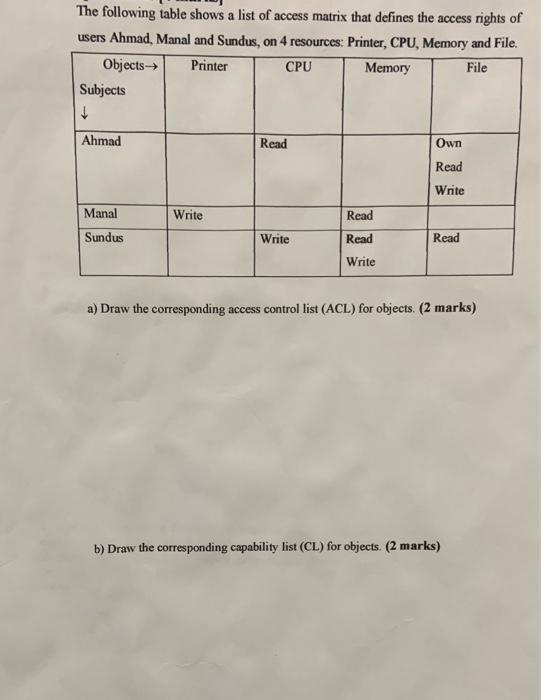
The following table shows a list of access matrix that defines the access rights of users Ahmad, Manal and Sundus, on 4 resources: Printer, CPU, Memory and File. Objects Printer CPU Memory File Subjects Ahmad Manal Sundus Write Read Write Read Read Write Own Read Write Read a) Draw the corresponding access control list (ACL) for objects. (2 marks) b) Draw the corresponding capability list (CL) for objects. (2 marks) The following table shows a list of access matrix that defines the access rights of users Ahmad, Manal and Sundus, on 4 resources: Printer, CPU, Memory and File. Objects Printer CPU Memory File Subjects Ahmad Manal Sundus Write Read Write Read Read Write Own Read Write Read a) Draw the corresponding access control list (ACL) for objects. (2 marks) b) Draw the corresponding capability list (CL) for objects. (2 marks)
Expert Answer:
Answer rating: 100% (QA)
Answer Access Control List ACL for Objects 1 Printer Ahmed read Manal read ... View the full answer

Related Book For 

Computer Architecture A Quantitative Approach
ISBN: 978-0123704900
4th edition
Authors: John L. Hennessy, David A. Patterson
Posted Date:
Students also viewed these computer network questions
-
A ball is dropped onto a horizontal pavement from a height of 3m. How high will the ball bounce if the coefficient of restitution is 0.2? How high does it bounce the second time? A snooker ball of...
-
1. Consider the market for some good produced by a competitive industry. The market begins in equilibrium. a. At the initial equilibrium price and quantity, what are consumer surplus, producer...
-
The following table shows a portion of the results from a clinical trial investigating the effectiveness of a monoamine oxidase inhibitor as a treatment for depression (207). The relationship between...
-
Histogram. Suppose that the standard input stream is a sequence of double values. Write a program that takes an integer n and two real numbers lo and hi as command-line arguments and uses StdDraw to...
-
Atlantic Cruise Co. is owned by Irina Temelkova. The following information is an alphabetical listing of financial statement items for the company for the year ended May 31, 2014: Instructions...
-
What accounts on the balance sheet must be evaluated when completing the financing activities section of the statement of cash flows?
-
Debit and Credit Effects of Transactions} Mackenzie Corporation was involved in the following transactions during the current year: a. Mackenzie borrowed cash from the local bank on a note payable....
-
Castro Company makes and sells a single product. Castro incurred the following costs in its most recent fiscal year. Cost Items Appearing on the Income Statement Materials cost ($9 per unit)...
-
QUESTION S Graph the following function on your calculator: f(x) = -0.0015x4 + 0.54x3 _ 12.6x2 - 5,280x + 288,000 Which of the following statements about f(x) is true? O This function has an absolute...
-
Consumer Research, owned by Chandler Robertson, is retained by large companies to test consumer reaction to new products. On January 31, 20X1, the firms worksheet showed the following adjustments...
-
Hello, I'm studying Intermiadiate Acc II, I need help with to calculate the effect of the PBO pension debt of a company with the following information: A company has a defined pension plan. As of...
-
Briefly explain the nature of trusted processes within a security kernel. Why do trusted processes need special attention during the audit of an operating system?
-
What is collateral? Give some examples.
-
Briefly describe a strategy that can be used to implement concurrency controls in a distributed database subsystem when the database is a. Replicated b. Partitioned
-
Distinguish between the implosion and the explosion purposes of an accounting audit trail for the database subsystem. Use an accounts payable system to illustrate your answer.
-
What is meant by noise on a communication line? What factors affect the amount of noise that exists on a line? What are the effects of noise?
-
If x + y+z = 9, dx dt = 8, and dy dt dz = : 5, find when (x, y, z) = (2, 2, 1). dt
-
You have just begun your summer internship at Omni Instruments. The company supplies sterilized surgical instruments for physicians. To expand sales, Omni is considering paying a commission to its...
-
Reorder the instructions to improve performance of the code in Figure 2.35. Assume the two-pipe machine in Exercise 2.3, and that the out-of-order completion issues of Exercise 2.4 have been dealt...
-
You are provisioning a server based on the system above. All 8 cores on the CMP will be busy with an overall CPI of 2.0 (assuming level 2 cache miss refills are not delayed). What bandwidth is...
-
Virtual machines have the potential for adding many beneficial capabilities to computer systems, for example, resulting in improved total cost of ownership (TCO) or availability. Could VMs be used to...
-
When considering data quality, what are the differences among validity, reliability, and representativeness? How do you know the data have high levels of these characteristics?
-
What are some advantages and disadvantages of telephone interviews, mail questionnaires, face-to-face interviews, and online interviews?
-
What is data mining? How is it used by marketers?

Study smarter with the SolutionInn App