Answered step by step
Verified Expert Solution
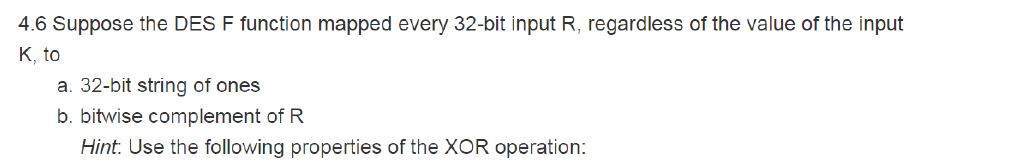
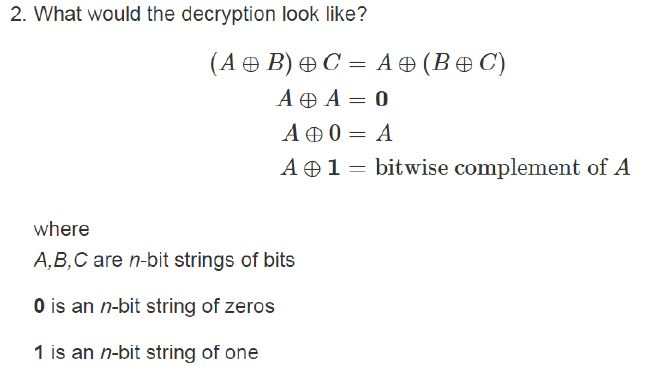
Question
1 Approved Answer
There is no solution to this in the cryptography and network security 7th edition solutions manual. Someone answered the first part of question 4.6 but
There is no solution to this in the cryptography and network security 7th edition solutions manual. Someone answered the first part of question 4.6 but not the second part. I am stuck on this
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


