Answered step by step
Verified Expert Solution
Question
1 Approved Answer
This problem deals with the protocol in Figure 9.17. a) Show that this protocol is insecure. Hint: Let Trudy be the man-in-the-middle, and show that
This problem deals with the protocol in Figure 9.17.
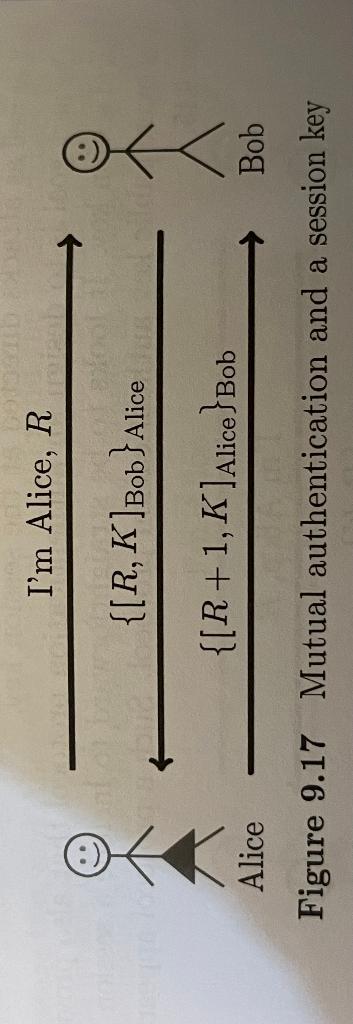
a) Show that this protocol is insecure. Hint: Let Trudy be the man-in-the-middle, and show that Trudy can convince Alice that she is Bob, and Trudy can determine Alice's session key K.
b) Slightly modify the protocol so that Trudy cannot obtain the session key
Figure 9.17 Mutual authentication and a session key
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


