Answered step by step
Verified Expert Solution
Question
1 Approved Answer
This question and the two following questions relate to the Cuckoo report shown below. All APIs in the summary presented in the report were part
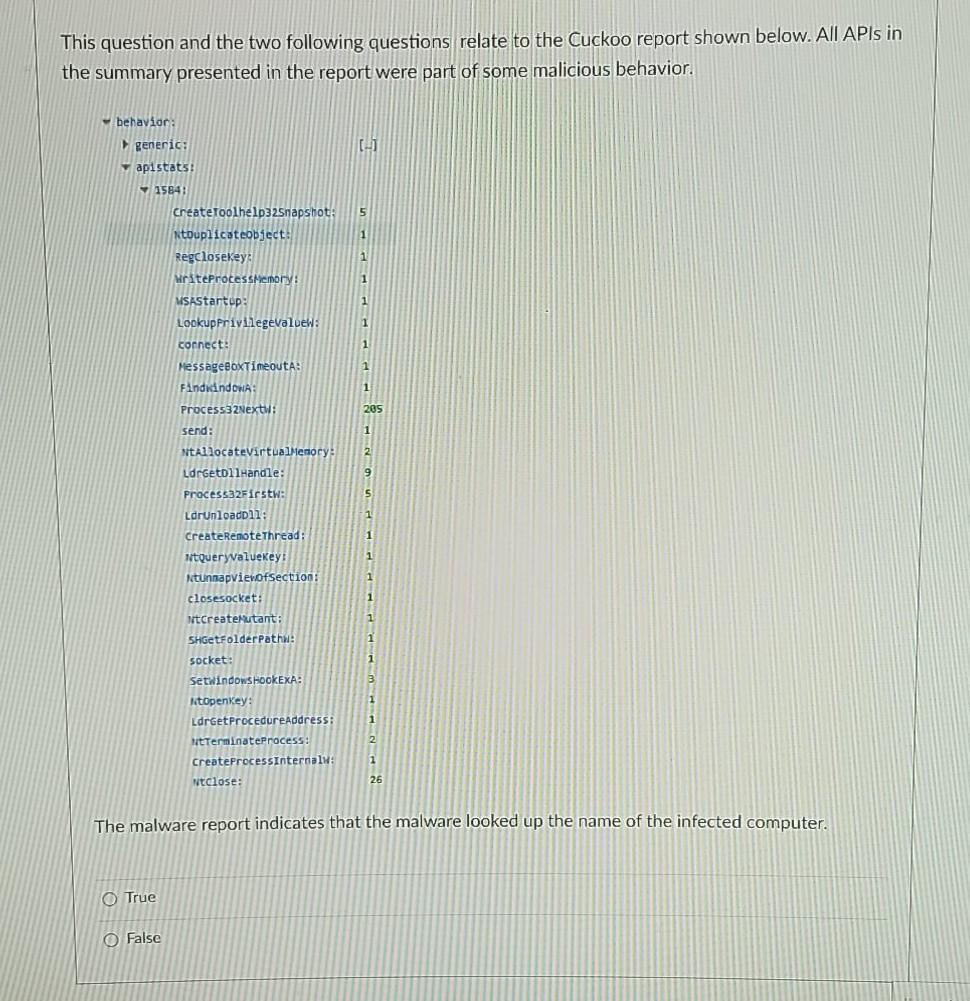
This question and the two following questions relate to the Cuckoo report shown below. All APIs in the summary presented in the report were part of some malicious behavior. behavior: generic: apistats: [-] 5 1 1 1 1 1 1 1 205 7 1584: Create Toolhelp32Snapshot: NtDuplicateobject: RegcloseKey: WriteProcessMemory: MSAStartup: LookupFrivilegevaluew: connect MessageBoxTimeoutA: Find dindow: Process32Next : send: NtAllocateVirtualMemory: LorgetollHandle: Process32Firstw: LdrunloadDll: CreateRemote Thread: 1tQueryvalueKey NtunnapviewOfSection: closesocket: litcreateMutant: SHGetFolder pathi: socket: 1 2 9 S. 1 1 1 1 1 1 1 SetWindows HOOKEXA: 3 1 1 KtOpenKey: LdrGetProcedureAddress: WtTerminateProcess: CreateProcessInternal: Ntclose: 2 1 26 The malware report indicates that the malware looked up the name of the infected computer. O True O False
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


