Answered step by step
Verified Expert Solution
Question
1 Approved Answer
B.18) Consider the following sequence of events in a two-processor shared memory system. Assume that the cache blocks in each cache are all initially
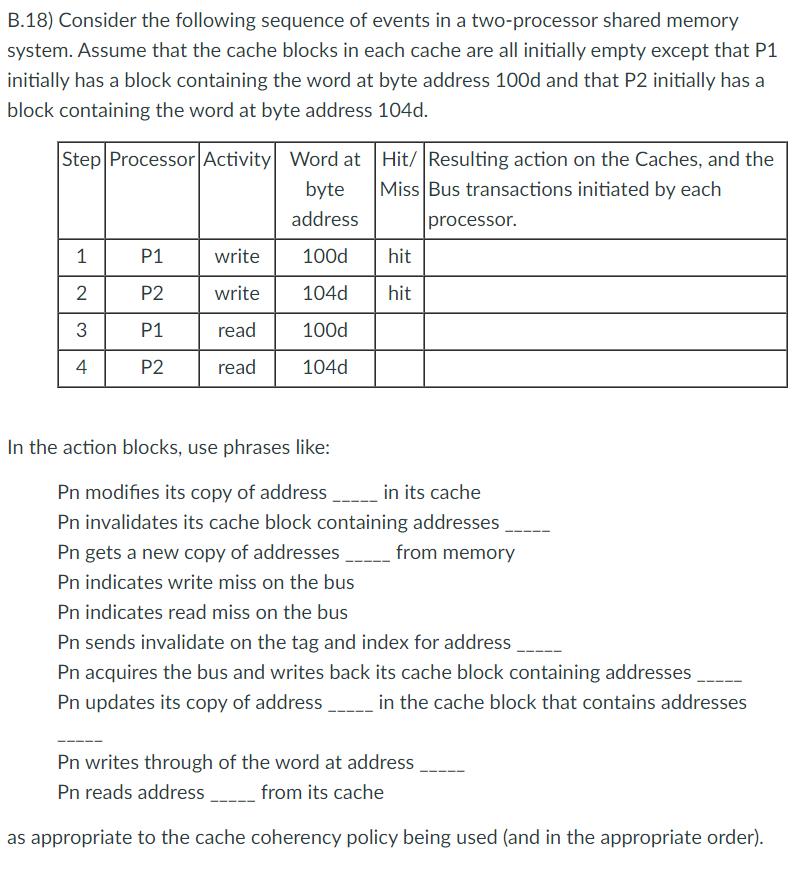

B.18) Consider the following sequence of events in a two-processor shared memory system. Assume that the cache blocks in each cache are all initially empty except that P1 initially has a block containing the word at byte address 100d and that P2 initially has a block containing the word at byte address 104d. Step Processor Activity Word at byte address 100d 104d 100d 104d 1 2 3 4 P1 P2 P1 P2 write write read read In the action blocks, use phrases like: Hit/ Resulting action on the Caches, and the Miss Bus transactions initiated by each processor. hit hit Pn modifies its copy of address_____ in its cache Pn invalidates its cache block containing addresses Pn gets a new copy of addresses from memory Pn indicates write miss on the bus Pn indicates read miss on the bus Pn sends invalidate on the tag and index for address Pn acquires the bus and writes back its cache block containing addresses Pn updates its copy of address_____ in the cache block that contains addresses Pn writes through of the word at address Pn reads address from its cache as appropriate to the cache coherency policy being used (and in the appropriate order). a) Complete the two right hand columns of the above table assuming that the processors use write-back caches with a write invalidate cache coherency policy (in which read or write misses in one processor's cache require that another cache that has a modified copy of the data be required to write it back to memory before the first cache can then read it from memory) and a block size of one word. b) What is the range of addresses of the data that falls in the same cache block as the word at 100d and the word at 104d if the cache block size is 4.(4-byte) words? (Note that the addresses given are byte addresses, and both the word at 100 and the word at 104 will fall in the same four word block.) c) Complete the right hand entries of the above table assuming that the processors use write-back caches with a write-invalidate cache coherency policy, and a block size of 4 (4-byte) words. d) Repeat part c above, but assume write-through caches and a write-update coherency_policy. (In a write-through cache, no invalidate signal is required. Other caches would simply see the write on the bus through their snoop units. Also, a write update policy would simply have caches, that also have a copy of the addressed location, copy the new data off the bus, updating their own copies, as it is written back to main memory.)
Step by Step Solution
★★★★★
3.40 Rating (166 Votes )
There are 3 Steps involved in it
Step: 1
a Assuming writeback caches with a write invalidate cache coherency policy and a block size of one word the completed table would look as follows Step ...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started