Question
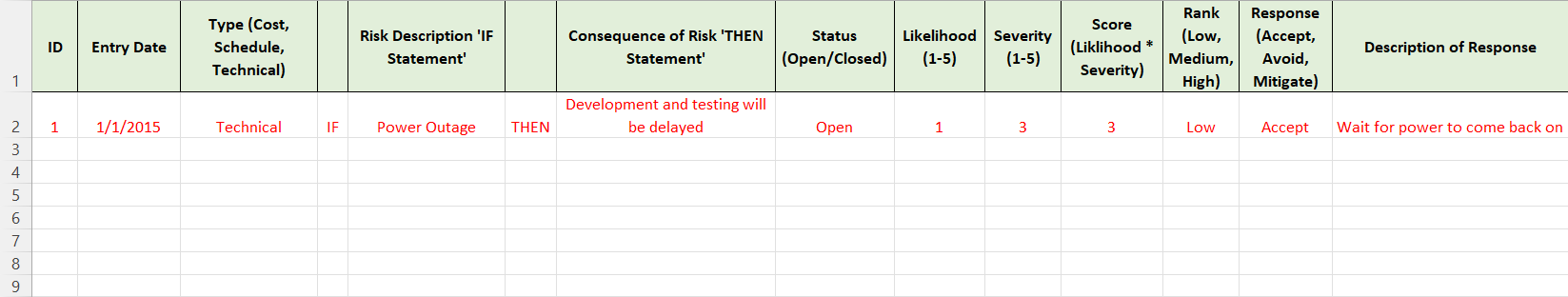
Using this Risk Register for IoT Device Vulnerability Analysis Project Risk ID | Risk Description | Impact | Probability | Current Control Measures | Recommended
Using this
Risk Register for IoT Device Vulnerability Analysis Project
Risk ID | Risk Description | Impact | Probability | Current Control Measures | Recommended Control Measures
1 | Inadequate device security | High | High | None | Conduct vulnerability assessments and penetration testing on all devices before deployment
2 | Unauthorized access to device data | High | Medium | None | Implement secure authentication and access controls
3 | Lack of software update capability | High | Medium | None | Implement over-the-air (OTA) updates for all devices
4 | Weak network security | Medium | High | None | Implement secure network protocols and regularly update network infrastructure
5 | Insufficient device configuration management | Medium | Low | None | Implement centralized device management and monitoring
6 | Inadequate incident response plan | Low | Medium | None | Develop and regularly test incident response plan
7 | Limited knowledge and skills of staff | Low | High | None | Provide regular training and education for staff on device security and best practices.
Label Type, Consequence of Risk, Status, Likelihood, Severity, Score, Rank and Response for all of the 7 risks.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


