Answered step by step
Verified Expert Solution
Question
1 Approved Answer
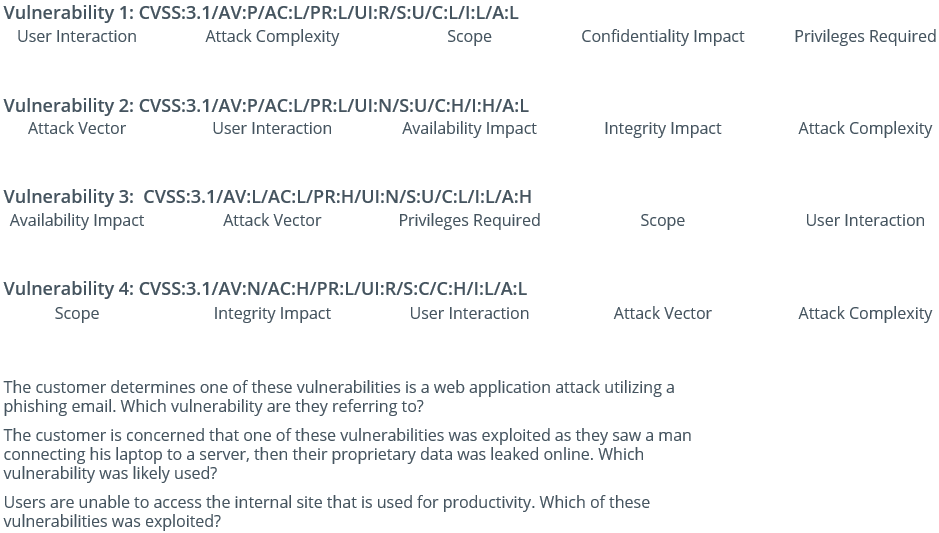
Vulnerability 1 : CVSS: 3 . 1 / AV:P / AC:L / PR:L / UI:R / S:U / C:L / I:L / A:L The customer
Vulnerability : CVSS:AV:PAC:LPR:LUI:RS:UC:LI:LA:L
The customer determines one of these vulnerabilities is a web application attack utilizing a
phishing email. Which vulnerability are they referring to
The customer is concerned that one of these vulnerabilities was exploited as they saw a man
connecting his laptop to a server, then their proprietary data was leaked online. Which
vulnerability was likely used?
Users are unable to access the internal site that is used for productivity. Which of these
vulnerabilities was exploited?
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started