What features did you find interesting and useful in Trustev's authentication method? What are the potential disadvantages
Fantastic news! We've Found the answer you've been seeking!
Question:
 What features did you find interesting and useful in Trustev's authentication method? What are the potential disadvantages of Trustev's authentication method?
What features did you find interesting and useful in Trustev's authentication method? What are the potential disadvantages of Trustev's authentication method?
Transcribed Image Text:
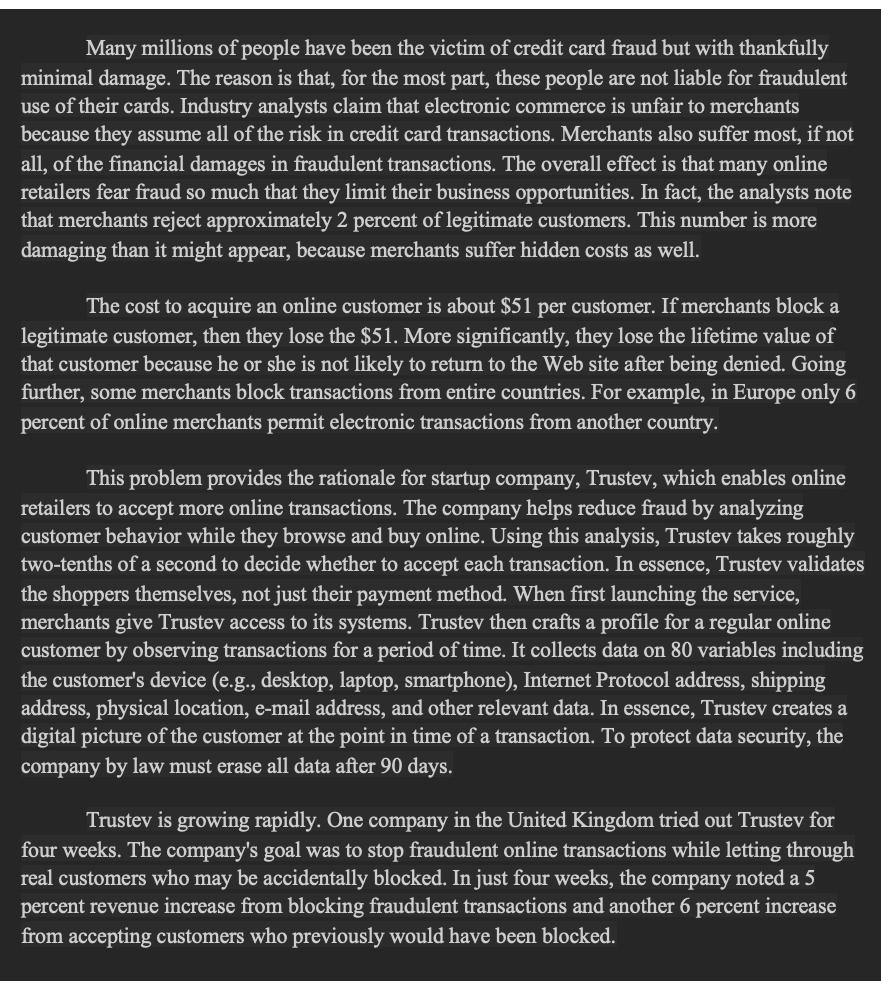
Many millions of people have been the victim of credit card fraud but with thankfully minimal damage. The reason is that, for the most part, these people are not liable for fraudulent use of their cards. Industry analysts claim that electronic commerce is unfair to merchants because they assume all of the risk in credit card transactions. Merchants also suffer most, if not all, of the financial damages in fraudulent transactions. The overall effect is that many online retailers fear fraud so much that they limit their business opportunities. In fact, the analysts note that merchants reject approximately 2 percent of legitimate customers. This number is more damaging than it might appear, because merchants suffer hidden costs as well. The cost to acquire an online customer is about $51 per customer. If merchants block a legitimate customer, then they lose the $51. More significantly, they lose the lifetime value of that customer because he or she is not likely to return to the Web site after being denied. Going further, some merchants block transactions from entire countries. For example, in Europe only 6 percent of online merchants permit electronic transactions from another country. This problem provides the rationale for startup company, Trustev, which enables online retailers to accept more online transactions. The company helps reduce fraud by analyzing customer behavior while they browse and buy online. Using this analysis, Trustev takes roughly two-tenths of a second to decide whether to accept each transaction. In essence, Trustev validates the shoppers themselves, not just their payment method. When first launching the service, merchants give Trustev access to its systems. Trustev then crafts a profile for a regular online customer by observing transactions for a period of time. It collects data on 80 variables including the customer's device (e.g., desktop, laptop, smartphone), Internet Protocol address, shipping address, physical location, e-mail address, and other relevant data. In essence, Trustev creates a digital picture of the customer at the point in time of a transaction. To protect data security, the company by law must erase all data after 90 days. Trustev is growing rapidly. One company in the United Kingdom tried out Trustev for four weeks. The company's goal was to stop fraudulent online transactions while letting through real customers who may be accidentally blocked. In just four weeks, the company noted a 5 percent revenue increase from blocking fraudulent transactions and another 6 percent increase from accepting customers who previously would have been blocked. Many millions of people have been the victim of credit card fraud but with thankfully minimal damage. The reason is that, for the most part, these people are not liable for fraudulent use of their cards. Industry analysts claim that electronic commerce is unfair to merchants because they assume all of the risk in credit card transactions. Merchants also suffer most, if not all, of the financial damages in fraudulent transactions. The overall effect is that many online retailers fear fraud so much that they limit their business opportunities. In fact, the analysts note that merchants reject approximately 2 percent of legitimate customers. This number is more damaging than it might appear, because merchants suffer hidden costs as well. The cost to acquire an online customer is about $51 per customer. If merchants block a legitimate customer, then they lose the $51. More significantly, they lose the lifetime value of that customer because he or she is not likely to return to the Web site after being denied. Going further, some merchants block transactions from entire countries. For example, in Europe only 6 percent of online merchants permit electronic transactions from another country. This problem provides the rationale for startup company, Trustev, which enables online retailers to accept more online transactions. The company helps reduce fraud by analyzing customer behavior while they browse and buy online. Using this analysis, Trustev takes roughly two-tenths of a second to decide whether to accept each transaction. In essence, Trustev validates the shoppers themselves, not just their payment method. When first launching the service, merchants give Trustev access to its systems. Trustev then crafts a profile for a regular online customer by observing transactions for a period of time. It collects data on 80 variables including the customer's device (e.g., desktop, laptop, smartphone), Internet Protocol address, shipping address, physical location, e-mail address, and other relevant data. In essence, Trustev creates a digital picture of the customer at the point in time of a transaction. To protect data security, the company by law must erase all data after 90 days. Trustev is growing rapidly. One company in the United Kingdom tried out Trustev for four weeks. The company's goal was to stop fraudulent online transactions while letting through real customers who may be accidentally blocked. In just four weeks, the company noted a 5 percent revenue increase from blocking fraudulent transactions and another 6 percent increase from accepting customers who previously would have been blocked.
Expert Answer:
Answer rating: 100% (QA)
The features of Trustevs authentication method that are interesting and useful include Realtime anal... View the full answer

Related Book For 

Organizational Behavior Science The Real World and You
ISBN: 978-1111825867
8th edition
Authors: Debra L. Nelson, James Campbell Quick
Posted Date:
Students also viewed these general management questions
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
An LNC can detect alterations in the record by Select one: a. Examining notes written in the margin b. Looking through late entries for detailed explanations c. Finding a doctor's explanation that is...
-
The handcart has wheels with a diameter D. If a crate having a weight W is placed on the cart, determine the force P that must be applied to the handle to overcome the rolling resistance. The...
-
(a) What must the emf E of the battery be in order for a current of 2.00 A to flow through the 5.00-Vbattery as shown? Is the polarity of the battery correct as shown? (b) How long does it take for...
-
What is CREST?
-
Barr Company had total assets of $320,000 in 2010, $340,000 in 2011, and $380,000 in 2012. Its debts to equity ratio was 0.67 times in all three years. In 2011, Barr had net income of $38,556 on...
-
Problem 8-30 Investment Criteria (LO1, LO2, LO4, LO5) A new furnace for your small factory is being installed right now, will cost $39,000, and will be completed in one year. At that point, it will...
-
A flight simulator is used to train pilots on how to recognize spatial disorientation. It has four degrees of freedom, and can rotate around a planetary axis as well as in yaw, pitch, and roll. The...
-
What is the purpose of the regulations the Bureau has implemented for real estate transactions,and how have they been implemented?
-
What is the just-in-time manufacturing philosophy? Describe it.
-
Which inventory costing method requires that a company keep track of the cost of each specific unit of inventory? a. Specific identification b. Lower of cost or market method c. LIFO d. All of the...
-
Should workers compensation insurance continue to be no-fault? Why, or why not?
-
What is the effect on reported net income of applying the lower-of-cost-or-net realizable value method to ending inventory?
-
Which of the following is not an inventory costing method? a. Specific identification b. Weighted-average cost c. Just-in-time manufacturing d. FIFO
-
x-49 12 Multiply and y (x-7)2
-
On average there are four traffic accidents in a city during one hour of rush-hour traffic. Use the Poisson distribution to calculate the probability that in one such hour there arc (a) No accidents...
-
What are positive and negative consequences in shaping behavior? How should they be managed? Explain the value of extinction as a strategy.
-
1. Briefly describe each of the four major challenges that Netflix faces. Which of these four challenges will be the most difficult to address? Why? Which challenge will be the easiest to address?...
-
How do hygiene and motivational factors differ? What are the implications of the two-factor theory for managers?
-
Graham Corporation used the following data to evaluate its current Kin operating system. The company sells items for \($10\) each and used a budgeted selling price of \($10\) per unit. a. Prepare the...
-
Selected data for Miller Company, which operates three departments, follow: During the year, the companys fixed expenses included the following: Assume that the property tax rate is the same for both...
-
Johnson Company has two sources of funds: long term debt and equity capital. Johnson Company has profit centers in the following locations with the following net incomes and total assets: a....

Study smarter with the SolutionInn App