Answered step by step
Verified Expert Solution
Question
1 Approved Answer
Which of the following five security services are implemented by the protocol given below, assuming that the session key KAB is generated at random by
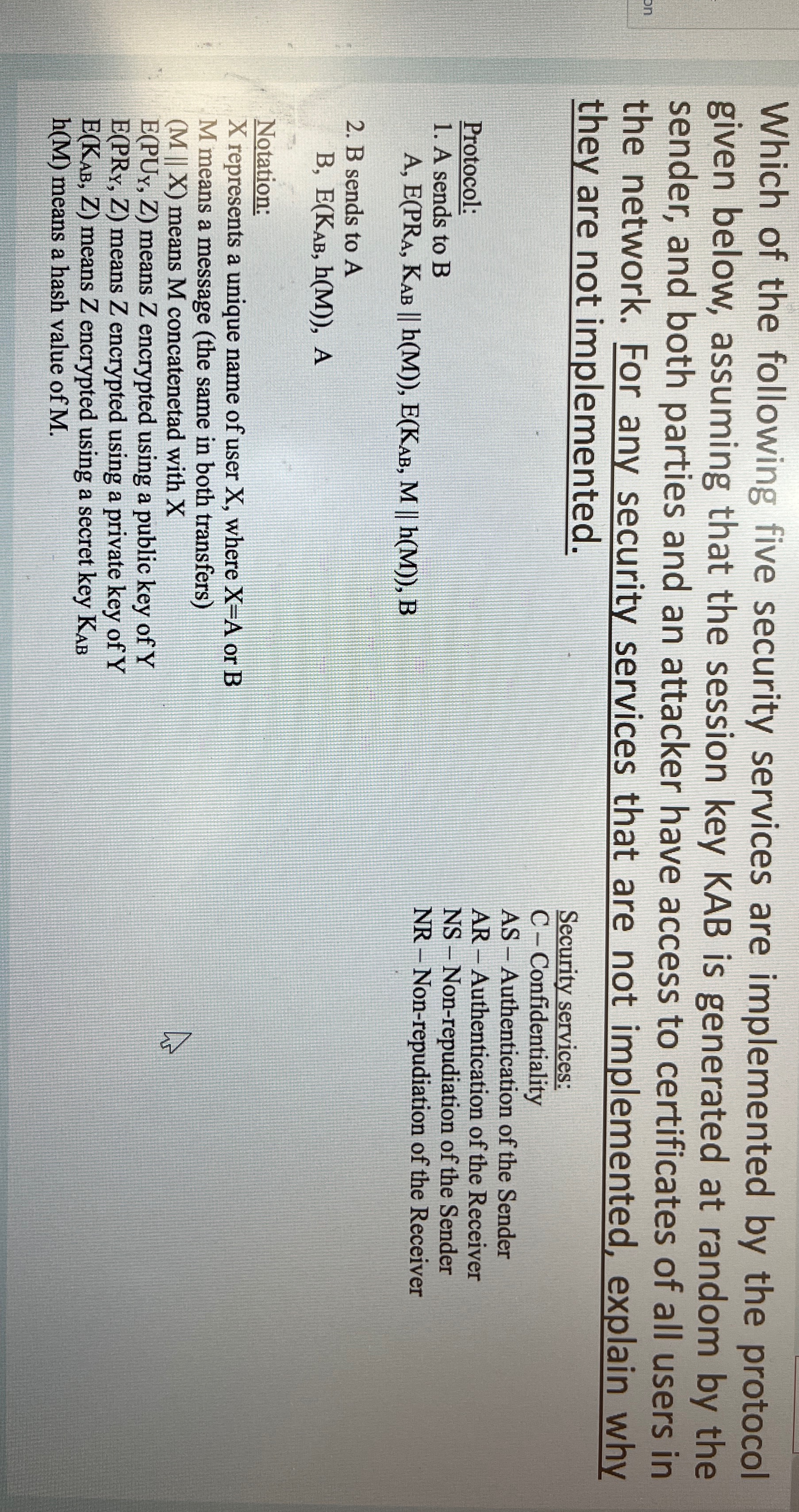
Which of the following five security services are implemented by the protocol given below, assuming that the session key KAB is generated at random by the sender and both parties and an attacker have access to certificates of all users in the network. For any security services that are not implemented, explain why they are not implemented.
Protocol:
A sends to
B sends to
Notation:
represents a unique name of user where or
means a message the same in both transfers
means concatenetad with
means encrypted using a public key of
means encrypted using a private key of
means encrypted using a secret key
means a hash value of
Security services:
CConfidentiality
AS Authentication of the Sender
AR Authentication of the Receiver
NS Nonrepudiation of the Sender
NR Nonrepudiation of the Receiver
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


