Answered step by step
Verified Expert Solution
Question
1 Approved Answer
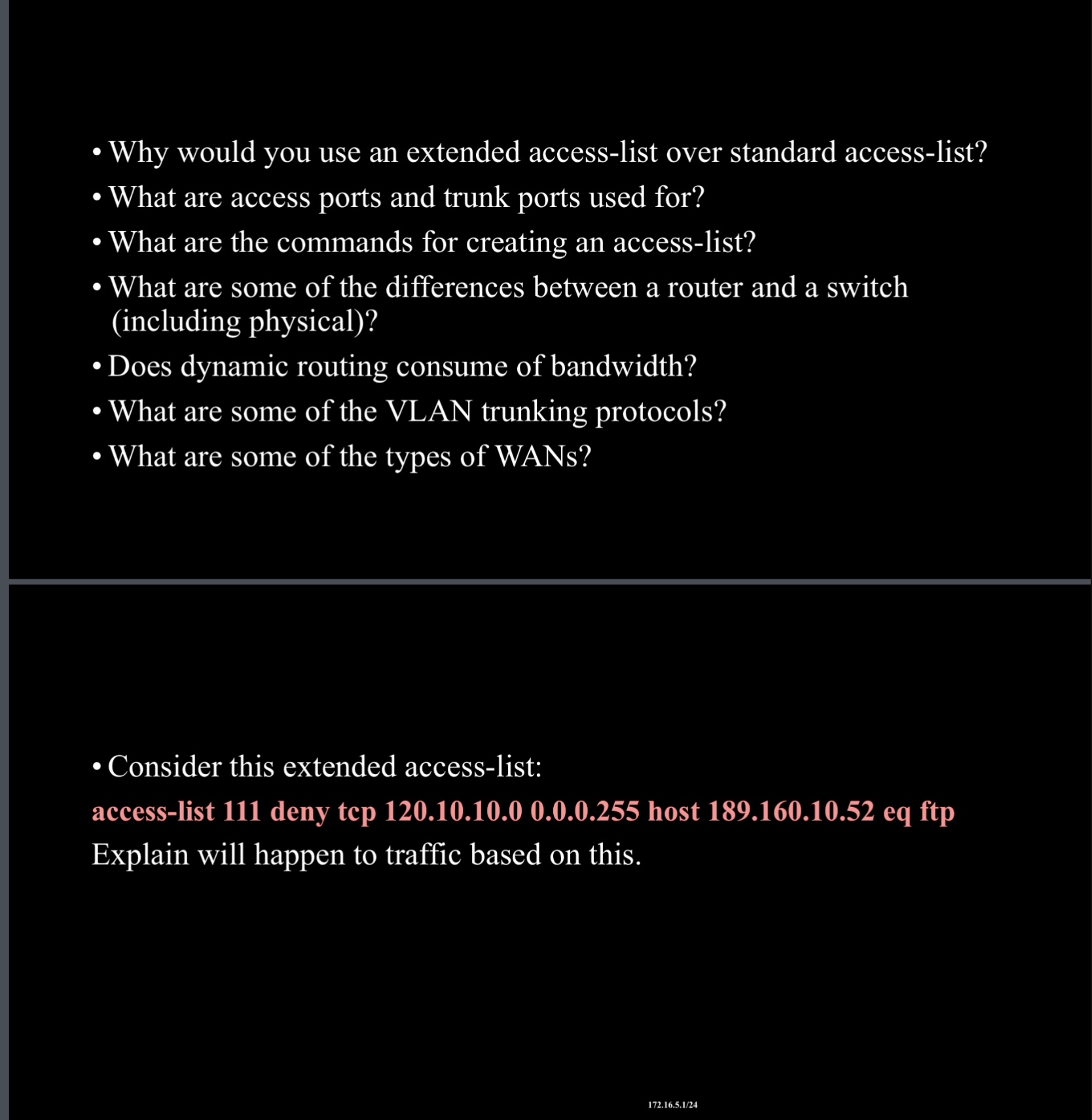
- Why would you use an extended access - list over standard access - list? - What are access ports and trunk ports used for?
Why would you use an extended accesslist over standard accesslist?
What are access ports and trunk ports used for?
What are the commands for creating an accesslist?
What are some of the differences between a router and a switch including physical
Does dynamic routing consume of bandwidth?
What are some of the VLAN trunking protocols?
What are some of the types of WANs?
Consider this extended accesslist:
accesslist deny tep host eq ftp Explain will happen to traffic based on this.
Step by Step Solution
There are 3 Steps involved in it
Step: 1

Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get Started


