Question
You are at work and you open up an email from a coworker asking you to download an application attachment. You do so, and
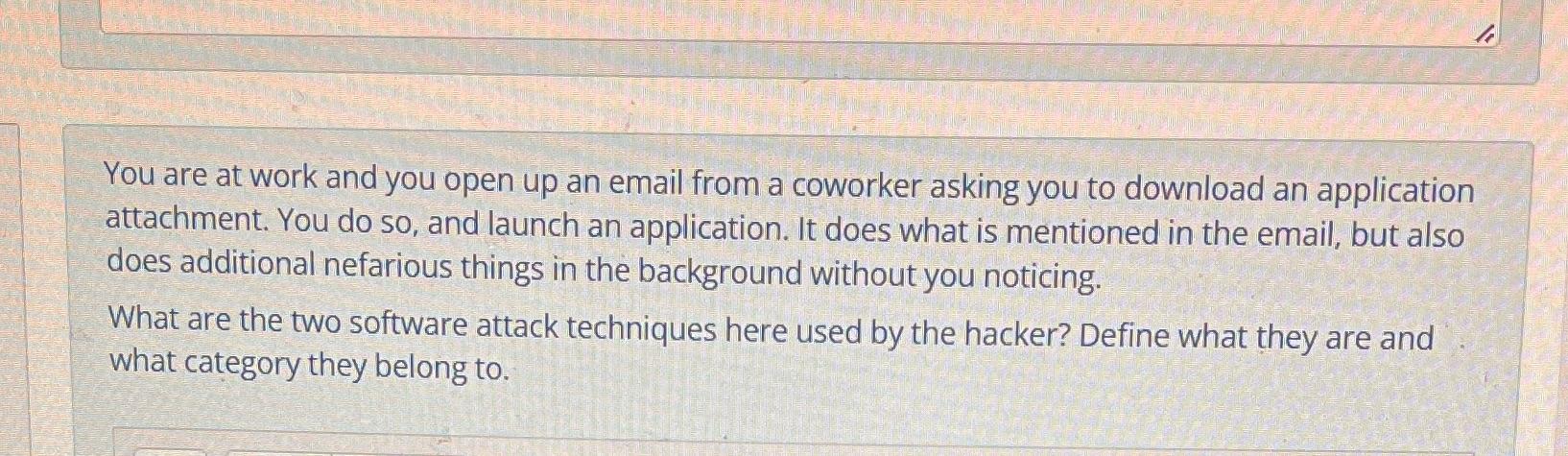
You are at work and you open up an email from a coworker asking you to download an application attachment. You do so, and launch an application. It does what is mentioned in the email, but also does additional nefarious things in the background without you noticing. What are the two software attack techniques here used by the hacker? Define what they are and what category they belong to.
Step by Step Solution
There are 3 Steps involved in it
Step: 1
Answer The two software attack techniques used by the hacker in this scenario are 1 Trojan Horse A T...
Get Instant Access to Expert-Tailored Solutions
See step-by-step solutions with expert insights and AI powered tools for academic success
Step: 2

Step: 3

Ace Your Homework with AI
Get the answers you need in no time with our AI-driven, step-by-step assistance
Get StartedRecommended Textbook for
Management Accounting
Authors: Leslie G. Eldenburg, Albie Brooks, Judy Oliver, Gillian Vesty, Rodney Dormer, Vijaya Murthy, Nick Pawsey
4th Edition
0730369382, 978-0730369387
Students also viewed these Business Communication questions
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
Question
Answered: 1 week ago
View Answer in SolutionInn App