A permutation block (P-box) in a modern block cipher is an example of a keyless transposition cipher.
Question:
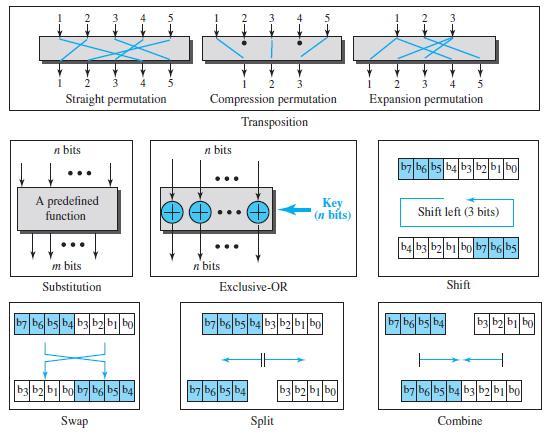
A permutation block (P-box) in a modern block cipher is an example of a keyless transposition cipher. What does this statement mean? (See Figure 31.8 in the text.)
Figure 31.8
Transcribed Image Text:
2 3. 2 Straight permutation Compression permutation Expansion permutation Transposition п bits n bits b7 b6 bs b4 b3 b2bi bo A predefined Key (n bits) function Shift left (3 bits) b4 b3 b2 b1 bo b7 b6 b5 m bits n bits Substitution Exclusive-OR Shift b7 b6 bsb4 b3b2bi bo b7 b6 bs b4 b3 b2 bi bo b7 bg bs b4 b3|b2b| bo bbb bob7 be bs b4 b7 b6 bs b4 b3 b2 b1 bo b7 b6 bs b4 b3 b2b bo Swap Split Combine
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 81% (16 reviews)
This means that the ...View the full answer

Answered By

Ashington Waweru
I am a lecturer, research writer and also a qualified financial analyst and accountant. I am qualified and articulate in many disciplines including English, Accounting, Finance, Quantitative spreadsheet analysis, Economics, and Statistics. I am an expert with sixteen years of experience in online industry-related work. I have a master's in business administration and a bachelor’s degree in education, accounting, and economics options.
I am a writer and proofreading expert with sixteen years of experience in online writing, proofreading, and text editing. I have vast knowledge and experience in writing techniques and styles such as APA, ASA, MLA, Chicago, Turabian, IEEE, and many others.
I am also an online blogger and research writer with sixteen years of writing and proofreading articles and reports. I have written many scripts and articles for blogs, and I also specialize in search engine
I have sixteen years of experience in Excel data entry, Excel data analysis, R-studio quantitative analysis, SPSS quantitative analysis, research writing, and proofreading articles and reports. I will deliver the highest quality online and offline Excel, R, SPSS, and other spreadsheet solutions within your operational deadlines. I have also compiled many original Excel quantitative and text spreadsheets which solve client’s problems in my research writing career.
I have extensive enterprise resource planning accounting, financial modeling, financial reporting, and company analysis: customer relationship management, enterprise resource planning, financial accounting projects, and corporate finance.
I am articulate in psychology, engineering, nursing, counseling, project management, accounting, finance, quantitative spreadsheet analysis, statistical and economic analysis, among many other industry fields and academic disciplines. I work to solve problems and provide accurate and credible solutions and research reports in all industries in the global economy.
I have taught and conducted masters and Ph.D. thesis research for specialists in Quantitative finance, Financial Accounting, Actuarial science, Macroeconomics, Microeconomics, Risk Management, Managerial Economics, Engineering Economics, Financial economics, Taxation and many other disciplines including water engineering, psychology, e-commerce, mechanical engineering, leadership and many others.
I have developed many courses on online websites like Teachable and Thinkific. I also developed an accounting reporting automation software project for Utafiti sacco located at ILRI Uthiru Kenya when I was working there in year 2001.
I am a mature, self-motivated worker who delivers high-quality, on-time reports which solve client’s problems accurately.
I have written many academic and professional industry research papers and tutored many clients from college to university undergraduate, master's and Ph.D. students, and corporate professionals. I anticipate your hiring me.
I know I will deliver the highest quality work you will find anywhere to award me your project work. Please note that I am looking for a long-term work relationship with you. I look forward to you delivering the best service to you.
3.00+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
What does this statement mean: "Hardware is useless without software"?
-
Each round in a block cipher should be invertible to make the whole block invertible. Modern block ciphers use two approaches to achieve this. In the first approach, each component is invertible; in...
-
A d-dimensional box with dimensions (x 1 , x 2 , . . . ,x d ) nests within another box with dimensions (y 1 , y 2 , . . . ,y d ) if there exists a permutation on {1, 2, . . . ,d} such that x (1) < y...
-
Implement the method contains() for BST.
-
Illustrate the importance of 'word-of-mouth' and opinion leadership in terms of buyer behaviour. Explain how peer group pressure might be made to work in magazine advertising.
-
A chemical processing corporation is considering three methods to dispose of a non-hazardous chemical sludge: land application, fluidized-bed incineration, and private disposal contract. The...
-
What mechanisms are available to help provide stakeholders with an assurance that a company complies with environmental regulations?
-
On August 1, Wilshire Company borrowed $150,000 from Peoples National Bank on a one-year, 8 percent note. Required: What adjusting entry should Wilshire make at December 31?
-
Suppose you have two different continuous and aligned fiber-reinforced composites. Both are made with carbon fibers and epoxy matrix, with composition and properties as in problem 2. In the first...
-
Suppose that a synchronous generator is connected to an infinite bus. Base frequency of the system is 50 Hz, the voltage of the infinite bus is 1.03 pu, the voltage of the machine is 1.01 pu, the...
-
Assume you want to write a program to simulate the permutation boxes in Figure 31.8 in the text. Figure 31.8 a. Show how you represent each box as a table. b. Show the inversion of each box as a...
-
Assume we have a very simple message digest. Our unrealistic message digest is just one number between 0 and 25. The digest is initially set to 0. The cryptographic hash function adds the current...
-
Selected transactions of Orange Corporation during 20X1 are given below. Record them in the general journal. Analyze: If the dividends declared on October 30 were to be paid on January 15, what...
-
When are two matrices equal?
-
A stone tunnel is to be constructed such that the opening is a semielliptic arch, as shown in Figure 15.45. It is necessary to know the height at 4 -ft intervals from the center. That is, how high is...
-
Five identical containers (shoe boxes, paper cups, etc.) must be prepared for this problem, with contents as follows: There are five boxes containing red and white items (such as marbles, poker...
-
Find the area of a circle as a function of its circumference.
-
Tell what the output value is for each of the function machines in Problems 15-20 for (a) 4 , (b) 6 , (c) -8 , (d) \(\frac{1}{2}\), (e) \(t\) x 421 + N/A C x +
-
a. What is the security benefit of Ethernet VLANs? 23a.) Which of the following provides security in Ethernet? a. RSTP b. SNMP c. VLANs d. All of the above b. In Figure 5-28, to which hosts can Host...
-
What are multinational corporations (MNCs) and what economic roles do they play?
-
What is the difference between the prefix increment operator and the postfix increment operator?
-
Identify and correct the errors in each of the following pieces of code. [There may be more than one error in each piece of code.] a) if (age >= 65); { Console.WriteLine("Age greater than or equal to...
-
What does the following app display? // Ex. 5.16: Mystery.cs 2 using System; 3 4 class Mystery { static void Main() { int x = 1; int total 0; 10 while (x
-
4. Calculate the expected concentration of the sodium hydroxide solution. The molar mass of NaOH is 39.997 g/mol. 5. Calculate and record the expected mass of benzoic acid required to react with...
-
The new bookkeeper at Karlin Construction Company was asked to write off two accounts totaling $1,680 that had been determined to be uncollectible. Accordingly, he debite- Accounts Receivable for...
-
Ammonium carbonate, (NH 4 ) 2 CO 3 dissolves in water releasing the ammonium ion, NH 4 + , and carbonate ion, CO 3 2- into solution. Both of these ions hydrolyze (react with water). The chemical...

Study smarter with the SolutionInn App


