Assume you want to write a program to simulate the permutation boxes in Figure 31.8 in the
Question:
Assume you want to write a program to simulate the permutation boxes in Figure 31.8 in the text.
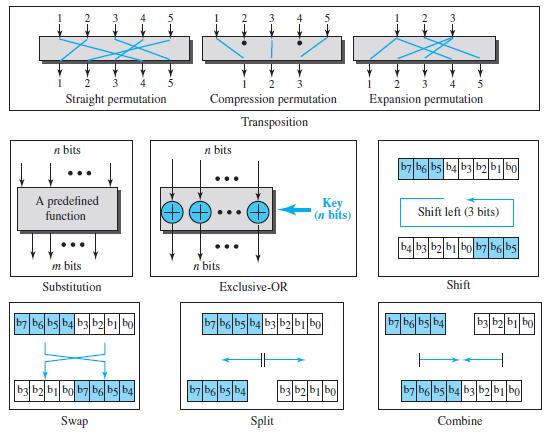
Figure 31.8
a. Show how you represent each box as a table.
b. Show the inversion of each box as a table.
Transcribed Image Text:
3. 2 3 Straight permutation Compression permutation Expansion permutation Transposition п bits n bits b7 b6 bs b4 b3 b2bi bo A predefined Key (n bits) function Shift left (3 bits) b4 b3 b2 b|bob7 b6 bs m bits n bits Substitution Exclusive-OR Shift b7 b6 bs b4 b3 b2bi bo b7 b6 bs b4 b3 b2 bibo b7 b6 bs b4 b3|b2b||bo bbb bob7 be bs b4 b7 b6 bs b4 b3 b2 b1 bo b7 b6 bs b4 b3 b2b bo Swap Split Combine
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 42% (7 reviews)
As we said about the keys for the transposition cipher permutation boxes Pboxes can be represented b...View the full answer

Answered By

HARSH RANJAN
Taken classes at college to graduates, Also worked as an expert to a freelancer online question-solving portal for more than 8 months with an average rating greater than 4.2 out of 5.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write a program to simulate the distance-vector algorithm (Table 20.1). for (y = 1 to N) { if (y is a neighbor) D[y] = c[myself][y] else 10 D[y] = 0 11 } send vector {D[1], D[2], ..., D[N]} to all...
-
Write a program to simulate the path-vector algorithm (Table 20.3). Table 20.3 Path-vector algorithm for a node 1 Path_Vector_Routing ( ) 2 { // Initialization for (y = 1 to N) 3 { if (y is myself)...
-
Write a program to simulate the sending-site FSMs for the simple protocol (Figure 23.18). Figure 23.18 FSMS for the simple protocol Request came from application. Packet arrived. Make a packet and...
-
Develop a data type ResizingArrayQueueOfStrings that implements a queue with a fixed-length array in such a way that all operations take constant time. Then, extend your implementation to use a...
-
Critically examine the usefulness or not to marketers of Holbrook and Hirschman's Hedonic and Experiential theory of buyer behaviour. Contrast this with the more traditional ELM.
-
A sports mortgage is the brainchild of Stadium Capital Financing Group, a company headquartered in Chicago, Illinois. It is an innovative way to finance cash-strapped sports programs by allowing fans...
-
If fines for non-compliance are much higher than ever before, how might increased transparency, brought about by environmental accounting disclosures, still act as a competitive advantage to a...
-
Historically, technology firms have been the most aggressive users of stock-based compensation in the form of stock options granted to almost all employees of the firms. What is the rationale for...
-
A simple gas of mass m with a number density n and temperature T is enclosed in a container. The gas escape into a vacuum through a small circular hole of area A in the container. If the wall...
-
Suppose that a synchronous generator is connected to an infinite bus. Base frequency of the system is 50 Hz, the voltage of the infinite bus is 1.03 pu, the voltage of the machine is 1.01 pu, the...
-
The circular shift operation is one of the components of the modern block ciphers. a. Show the result of a 3-bit circular left shift on the word (10011011) 2 . b. Show the result of a 3-bit circular...
-
A permutation block (P-box) in a modern block cipher is an example of a keyless transposition cipher. What does this statement mean? (See Figure 31.8 in the text.) Figure 31.8 2 3. 2 Straight...
-
Suppose that a comet travels in a parabolic orbit with the sun as its focus. Position a polar coordinate system with the pole at the sun and the axis of the orbit perpendicular to the polar axis....
-
Describe the process for multiplying matrices.
-
In Problems 1-5, perform the indicated matrix operations, if possible, where \[\begin{array}{ll}{[\mathrm{A}]=\left[\begin{array}{rr}1 & 0 \\2 & -1\end{array}ight]} &...
-
Describe a procedure for solving a system of linear inequalities.
-
Can you relate to the Fox Trot comic strip at the beginning of this section? Why or why not? Why might you need to solve a system of equations?
-
Tell what the output value is for each of the function machines in Problems 15-20 for (a) 4 , (b) 6 , (c) -8 , (d) \(\frac{1}{2}\), (e) \(t\) f machine Add 5- Multiply by 2,
-
a. What security threat is 802.1X designed to protect against? 24a.) To prevent anyone from simply walking up to a corporate switch and plugging their computer into its Ethernet port, companies can...
-
Which one of the following anhydrous chloride is not obtained on direct heating of its hydrated chloride? (A) BaCl2 (B) CaClz (C) MgCl2 (D) SrCl2
-
Explain what happens when a C# app attempts to divide one integer by another. What happens to the fractional part of the calculation? How can you avoid that outcome?
-
Describe the two ways in which control statements can be combined.
-
What type of iteration would be appropriate for calculating the sum of the first 100 positive integers? What type of iteration would be appropriate for calculating the sum of an arbitrary number of...
-
If one person is selected Express the following probability as a simplified fraction and as a decimal. Marital Status of a Certain Population, Ages 18 or Older, in from the population Millions...
-
Westerville Company reported the following results from last year's operations: Sales Variable expenses Contribution margin Fixed expenses Net operating income Average operating assets $ 1,300,000...
-
Vertical Adventures has an open line of credit with a zero balance at its credit union using a fixed interest rate of 7.15%. On the last day of every month, the accrued interest must be paid. On July...

Study smarter with the SolutionInn App


