Write a program to simulate the distance-vector algorithm (Table 20.1). for (y = 1 to N) {
Question:
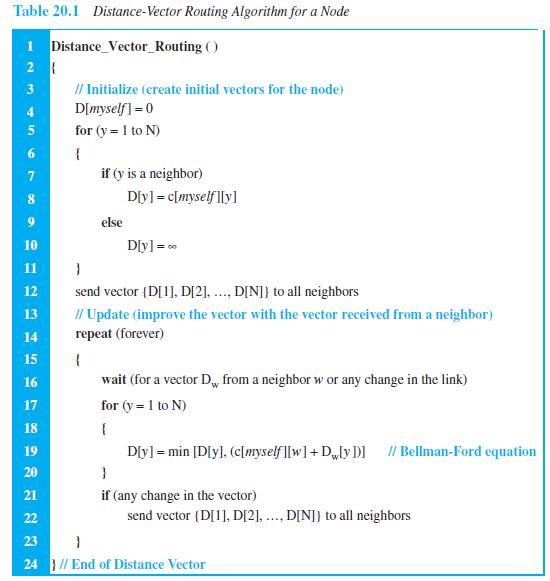
Write a program to simulate the distance-vector algorithm (Table 20.1).
Transcribed Image Text:
for (y = 1 to N) { if (y is a neighbor) D[y] = c[myself][y] else 10 D[y] = 0 11 } send vector {D[1], D[2], ..., D[N]} to all neighbors // Update (improve the vector with the vector received from a neighbor) repeat (forever) 12 13 14 15 { 16 wait (for a vector Dw from a neighbor w or any change in the link) for (y = 1 to N) 17 18 { 19 D[y] = min [D[y], (c[myself][w] + Dw[y])] // Bellman-Ford equation 20 } 21 if (any change in the vector) 22 send vector {D[1], D[2], ..., D[N]} to all neighbors 23 } 24 } // End of Distance Vector 6.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 91% (12 reviews)
The first program simulates the DistanceVector protocol The input object ...View the full answer

Answered By

Charles mwangi
I am a postgraduate in chemistry (Industrial chemistry with management),with writing experience for more than 3 years.I have specialized in content development,questions,term papers and assignments.Majoring in chemistry,information science,management,human resource management,accounting,business law,marketing,psychology,excl expert ,education and engineering.I have tutored in other different platforms where my DNA includes three key aspects i.e,quality papers,timely and free from any academic malpractices.I frequently engage clients in each and every step to ensure quality service delivery.This is to ensure sustainability of the tutoring aspects as well as the credibility of the platform.
4.30+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Write a program to simulate the link-state algorithm (Table 20.2). Dijkstra's Algorithm ( ) // Initialization Tree = {root} 3 I/ Tree is made only of the root 4. for (y = 1 to N) II N is the number...
-
Write a program to simulate the path-vector algorithm (Table 20.3). Table 20.3 Path-vector algorithm for a node 1 Path_Vector_Routing ( ) 2 { // Initialization for (y = 1 to N) 3 { if (y is myself)...
-
Write a program to simulate the sending-site FSMs for the Stop-and-Wait protocol (Figure 23.21). Figure 23.21 FSMS for the Stop-and-Wait protocol Sender Request came from application. Make a packet...
-
Jack Williams works in a very active department called purchasing. He works with store managers, marketing, and supply companies. The people in his department try to have the right product, in the...
-
Wilson Corporation (not real) has a targeted capital structure of 40% long term debt and 60% common stock. The debt is yielding 6% and the corporate tax rate is 35%. The common stock is trading at...
-
Why does the write-off of uncollectible accounts have no effect on the net realizable accounts receivable on the balance sheet if bad debts are estimated? What is the effect of this write-off on the...
-
Cotton, Corp., uses the allowance method to account for uncollectible accounts. On May 31,2010, Allowance for Uncollectible Accounts has a $1,300 credit bal ance. Journalize the year-end adjusting...
-
1. After taking into account the income that Sophia will receive from Social Security and her company sponsored pension plan, the financial planner has estimated that her investment assets will need...
-
How does the phenomenon of "emotional contagion" influence group dynamics within organizations, and what strategies can leaders employ to mitigate its potentially detrimental effects on team cohesion...
-
Vierra Popova Ltd now wishes to prepare its cash budget for the second six months of the year. The budgeted income statements for each month of the second half of the year are as follows: The...
-
In a graph, if we know that the shortest path from node A to node G is (A B E G), what is the shortest path from node G to node A?
-
Distinguish between multicasting and multiple unicasting.
-
Benfords Law: a. Is usually unsuccessful as a fraud detection tool. b. Predicts that the first digit of random number sets will begin with a 1 more often than a 2, a 2 more often than a 3, and so on....
-
Companies in the United State follow a set of accounting rules (GAAP) different from companies in many other counties in the world (IFRS). The SEC once worked hard on the convergence of GAAP and...
-
Based on this model, households earn income when purchase in markets for factors of production. Suppose Alyssa earns $700 per week working as a programmer for Maction. She uses $8 to have dessert at...
-
Dataset A: This dataset contains input/output data generated from a noisy polynomial model: y = f(x) + , where x 1 = [2,2] and K f(x) = m(x,a) = px(x; a):= [: m=0 xmam+1. Here, K 1 denotes the...
-
In early 2023, a New York attorney - Steven A. Schwartz - was investigated following the submission of a legal brief he filed in support of his client in a personal injury lawsuit against an airline....
-
Competitiveness is defined as how effectively an organization meets the wants and needs of its customers relative to other organizations with similar goods or services. Organizations compete through...
-
What four financial statements can be found in a firms filing with its provincial securities commission? What checks exist to ensure the accuracy of these statements?
-
Evaluate the line integral, where C is the given curve. C x 2 dx + y 2 dy, C consists of the arc of the circle x 2 + y 2 = 4 from (2, 0) to (0, 2) followed by the line segment from (0, 2) to (4, 3)
-
Compare the medium of a wired LAN with that of a wireless LAN in todays communication environment.
-
A program to simulate the calculation of CRC.
-
In an 802.11, give the value of the address 1 field in each of the following situations (left bit defines To DS and right bit defines From DS). a. 00 b. 01 c. 10 d. 11
-
Role play Accounts and ledgers - debtor management the student to participate and facilitate a role play meeting with Peter Crowe, a client from Hurst & Smith Plumbing Pty Ltd, who owes Azure Beach...
-
Conduct a financial analysis of the firm including calculating ratios in the following areas: Liquidity Asset management Debt Management Profitability Internal and Sustainable Growth Write Executive...
-
On June 8, Sheridan Ltd. was incorporated and issued 34,200 common shares for $342,000. On August 19, an additional 8,550 shares were issued for $102,600. On November 2, the company paid $32,832 to...

Study smarter with the SolutionInn App


